A sophisticated zero-click attack framework called RenderShock that exploits passive file processing systems in modern operating systems and enterprise environments.
Unlike traditional malware that requires user interaction, RenderShock leverages built-in preview mechanisms, file indexing services, and automation features to execute malicious payloads without any user clicks or actions.
RenderShock targets the passive execution surfaces that modern systems use for convenience and productivity.
The attack framework exploits file preview subsystems in Windows Explorer and macOS Quick Look, which automatically render content when files are selected or hovered over.
Email clients like Outlook that display attachment previews, metadata indexers including Windows Search and Spotlight, and antivirus scanning engines all become potential attack vectors.
The framework operates through five distinct stages: payload design, delivery mechanisms, trigger activation, payload effects, and lateral movement.
During the payload design phase, attackers craft malicious documents that execute when parsed by system processes metadata processors, sync clients, and content indexers.

These include PDFs with external references that trigger outbound connections, Office documents with remote templates that resolve during preview, and specially crafted shortcut files with UNC icon paths that leak NTLM credentials.
Advanced payload techniques include polyglot file formats that confuse multiple parsers, remote template injection in Office files without macros, and poisoned metadata in image files that crash indexing engines.
The attack leverages the system’s assumption that previewing or indexing a file is inherently safe, transforming routine background processes into unmonitored attack surfaces.
RenderShock 0-Click Vulnerability
Researchers demonstrated a practical proof-of-concept showing how RenderShock can steal Windows credentials without user interaction.
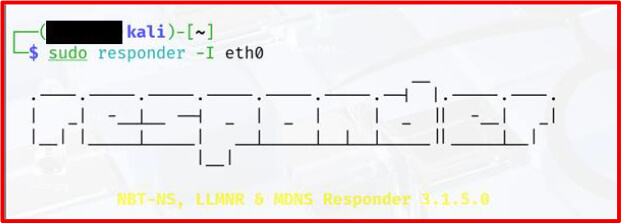
The attack involves creating a malicious .lnk shortcut file embedded within a ZIP archive. When a user simply selects the ZIP file in Windows Explorer with the preview pane enabled, the system attempts to load a remote icon from an attacker-controlled server, automatically transmitting NTLM authentication hashes.
The framework draws from real-world attack patterns observed in recent campaigns Windows attempts to load the icon and will silently initiate an SMB connection to the attacker

APT28 previously used Outlook calendar reminders with UNC paths to leak NTLM hashes without user clicks, while other threat actors have employed .library-ms files in ZIP archives to trigger authentication beacons during file preview.
These precedents validate RenderShock’s approach of weaponizing passive system behaviors.
RenderShock’s impact extends beyond credential theft to include reconnaissance through passive beacons, remote code execution via preview-based macro execution, and system disruption through indexing engine crashes.
The framework’s modular design allows attackers to adapt payloads for different environments and objectives while maintaining stealth through various evasion techniques.
Defense Strategies
Security experts recommend a multi-layered defense approach to counter RenderShock attacks.
Strategic recommendations include redefining trust boundaries to treat internal previews and indexing as potential execution surfaces rather than mere productivity features.
Organizations should implement sandboxed file processing pipelines that isolate preview generation from user contexts.
Tactical defenses involve disabling preview features in Windows Explorer and macOS Quick Look, restricting outbound SMB traffic, and hardening Office configurations to prevent automatic loading of remote templates.
File upload controls should sanitize content through sandbox analysis before preview, while behavioral monitoring should track preview-related processes making network calls.
The discovery of RenderShock highlights a fundamental shift in threat landscape, where attackers increasingly target automated system behaviors rather than relying on social engineering.
As enterprises adopt more convenience features and automation tools, security teams must expand their threat models to include zero-click attack vectors that exploit the very systems designed to enhance productivity.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




