A proof-of-concept (PoC) for CVE-2025-5777, dubbed “CitrixBleed 2,” a critical memory disclosure vulnerability affecting Citrix NetScaler devices.
The vulnerability, which bears striking similarities to the infamous 2023 CitrixBleed incident, is currently being exploited in the wild by multiple threat actors, prompting urgent warnings from the security community.
The vulnerability affects NetScaler devices configured as Gateway (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) or AAA virtual servers, potentially exposing sensitive memory contents to unauthorized attackers.
Citrix has officially described the vulnerability as “insufficient input validation leading to memory overread,” a classification that mirrors the original CitrixBleed vulnerability (CVE-2023-4966) that caused widespread damage across enterprise networks in 2023.
The technical analysis reveals that CVE-2025-5777 stems from improper handling of HTTP authentication requests at the NetScaler login interface.
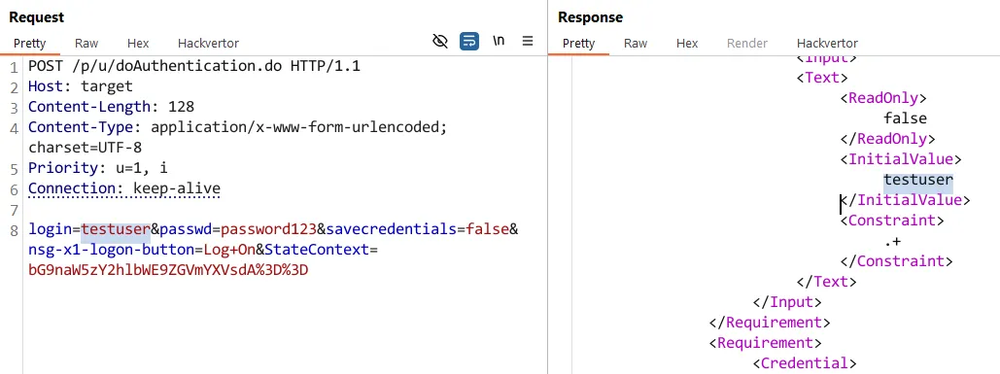
When attackers send malformed POST requests to the /p/u/doAuthentication.do endpoint without properly formatted login parameters, the system responds with uninitialized memory contents wrapped in XML tags.
The vulnerability occurs when the login parameter is provided without an equals sign or value, triggering a classic case of uninitialized variable usage.
The backend parser fails to properly initialize memory buffers, causing the system to leak whatever residual data occupied that memory space.
Using a format string %.*s, the leaked data continues until a null byte is encountered, potentially exposing several bytes of sensitive information with each request.
During testing, researchers successfully extracted HTTP request data from memory by repeatedly sending crafted requests.
While initial tests did not reveal cookies or session tokens, the researchers noted that production environments with active VPN connections could potentially leak more sensitive information.
CitrixBleed 2 Vulnerability
watchTowr Labs has provided specific detection methodology for identifying vulnerable systems.
The researchers emphasize that organizations should immediately patch vulnerable systems and monitor for unusual authentication traffic.
A simple HTTP POST request containing only the “login” parameter without assignment can reliably determine if a NetScaler device is vulnerable.
Vulnerable systems will return XML responses containing random memory data within <InitialValue></InitialValue> tags, while patched systems return empty or error responses.
The decision to release the Proof-of-concept came after researchers observed minimal information sharing regarding indicators of compromise (IoCs) and exploitation artifacts.
This lack of threat intelligence has left many organizations unable to determine their exposure levels or implement appropriate defensive measures.
Ongoing Exploitation
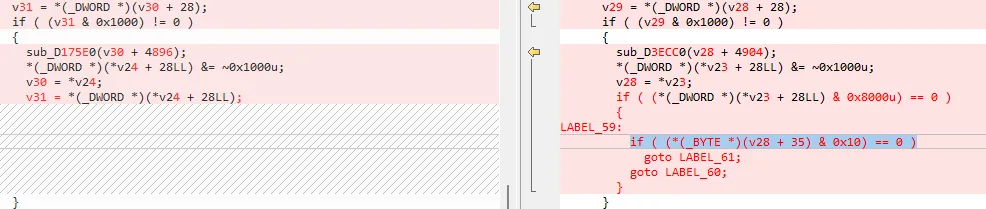
According to Report,the vulnerability affects Citrix NetScaler versions prior to 14.1.47.46.64, with the patch involving additional input validation checks.
Analysis showed that Citrix’s fix for the issue boils down to this line:
However, a significant portion of the NetScaler user base remains unpatched, creating an attractive target for threat actors who are already exploiting both CVE-2025-5777 and the related CVE-2025-6543.
Security experts warn that the exploitation pattern mirrors the original CitrixBleed campaign, which resulted in prolonged compromise campaigns affecting healthcare systems, government networks, and critical infrastructure.
The release of detection tools aims to enable defenders to identify vulnerable appliances and make evidence-based patching decisions, potentially preventing another wave of widespread compromises similar to those experienced during the original CitrixBleed incident.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




