A new social engineering attack technique called “FileFix” that exploits Windows File Explorer’s address bar functionality to execute malicious commands without leaving the browser environment.
This method represents an evolution of the popular ClickFix attacks that have been plaguing users over the past year.
The FileFix attack leverages a previously overlooked capability where File Explorer’s address bar can execute operating system commands when accessed through a web browser’s file upload functionality.
Unlike traditional ClickFix attacks that rely heavily on the Windows Run Dialog (Windows Key + R), this new technique operates entirely within the browser environment, making it potentially more deceptive to users.
Security researcher mr.d0x, who documented the attack method, discovered that HTML file input elements can trigger File Explorer windows that retain the ability to execute commands through the address bar.
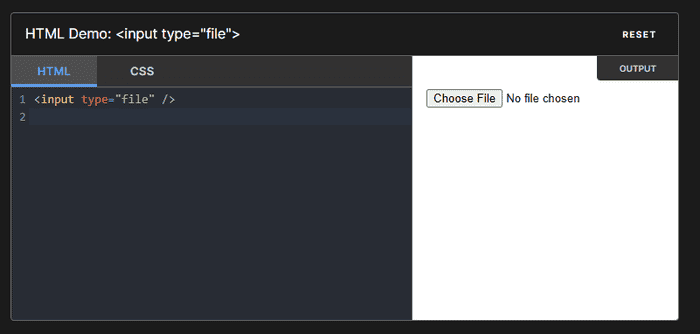
The attack works by creating a malicious webpage with a hidden file upload input and an “Open File Explorer” button that simultaneously copies a PowerShell command to the clipboard and launches the File Explorer window.
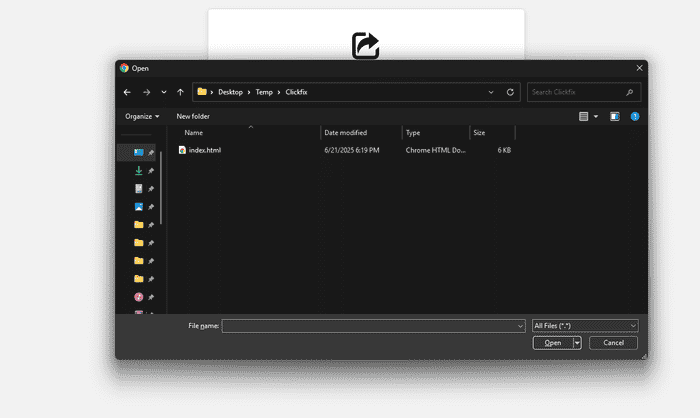
The social engineering aspect involves convincing users they need to access a shared file by pasting what appears to be a legitimate file path into File Explorer’s address bar.
However, the copied content actually contains a malicious PowerShell command disguised with a comment that displays the fake file path.
When users paste the content and press Enter, they unknowingly execute the hidden command while seeing only the benign file path.
Technical Implementation
The attack demonstrates sophisticated technical implementation that includes several evasion techniques.
The malicious PowerShell command is concatenated with a dummy file path after a comment symbol, effectively hiding the actual command from users while displaying what appears to be a legitimate file location.
The technique uses commands like “Powershell.exe -c ping example.com # C:\company\internal-secure\filedrive\HRPolicy.docx” where everything after the hash symbol appears as a comment.
Testing revealed that processes executed through File Explorer’s address bar are spawned as child processes of Chrome, indicating successful command execution within the browser’s security context.
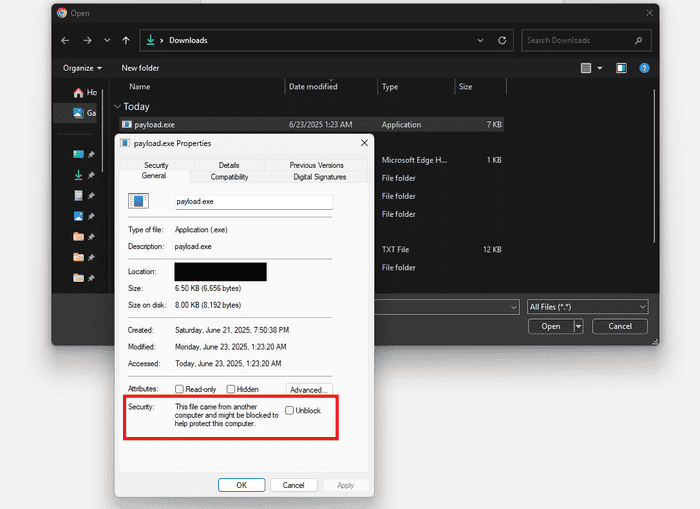
Additionally, researchers discovered that executable files launched through this method have their Mark of The Web (MOTW) attributes removed, potentially bypassing certain security restrictions that typically apply to downloaded files.
The attack includes defensive measures against accidental file uploads, intercepting any file selection attempts and redirecting users back to the malicious instructions.
This ensures users follow the intended attack path rather than using the file upload functionality as designed.
Security Implications
According to Report, FileFix attack represents a significant evolution in social engineering techniques, combining the effectiveness of ClickFix methods with improved stealth capabilities.
Security experts warn that the technique’s simplicity and effectiveness make it likely to be adopted by cybercriminals targeting unsuspecting users.
Organizations should implement monitoring for suspicious browser child processes, particularly cmd.exe, powershell.exe, and mshta.exe spawned by web browsers.
The attack’s ability to operate entirely within the browser environment while executing system-level commands makes traditional perimeter security measures less effective.
The discovery highlights the ongoing arms race between cybersecurity professionals and malicious actors, demonstrating how seemingly basic system functionalities can be weaponized for social engineering attacks.
Users should exercise extreme caution when websites request unusual file access procedures and organizations should consider implementing additional browser security policies to prevent such exploitation.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




