A critical zero-click vulnerability that circumvents Microsoft’s security patch for CVE-2025-24054, enabling attackers to extract NTLM credentials without any user interaction.
The new vulnerability, assigned CVE-2025-50154, demonstrates that Microsoft’s April security update was incomplete, leaving Windows systems vulnerable to credential theft and malicious payload delivery.
The vulnerability exploits a subtle gap in Microsoft’s patch by manipulating how Windows Explorer handles desktop shortcuts and their associated icons.
While the original CVE-2025-24054 allowed attackers to steal NTLM hashes through specially crafted shortcut files with remote icons, Microsoft’s patch blocked shortcuts from rendering icons based on UNC (Universal Naming Convention) paths.
However, researcher Ruben Enkaoua discovered that the patch doesn’t apply to remote binary files that contain their own icon data within the file itself.
By creating a shortcut that points to a remote executable file while using a default system icon, Windows Explorer automatically retrieves the entire binary to extract its embedded icon from the .rsrc section.
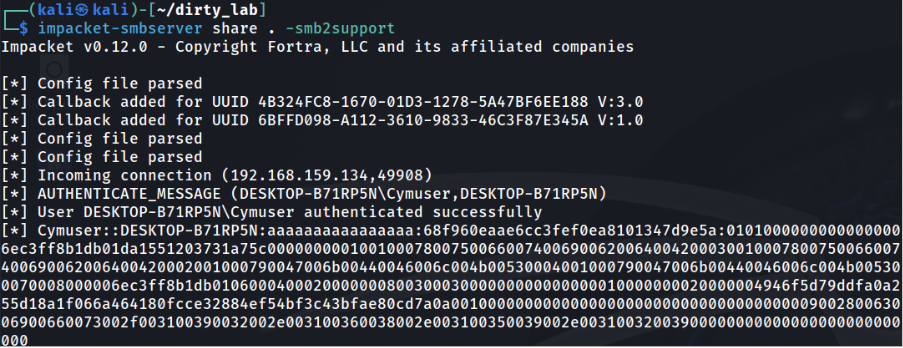
This process triggers NTLM authentication requests, exposing the user’s credentials to attackers monitoring network traffic.
The attack requires no user clicks or interaction – simply viewing the malicious shortcut in Windows Explorer is sufficient to compromise credentials.
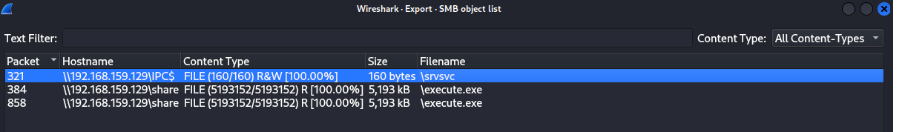
Testing revealed that the entire remote binary gets downloaded to the victim’s system during this process, creating additional security risks beyond credential theft.
New 0-Click NTLM Credential Leak
The impact of CVE-2025-50154 extends beyond simple credential theft, posing substantial risks to enterprise security.
NTLM hashes captured through this method can be subjected to offline brute-force attacks or used in relay attacks, where stolen credentials are passed to other network services to impersonate legitimate users.
The vulnerability becomes particularly dangerous when targeting accounts with elevated privileges, as successful exploitation can lead to privilege escalation and lateral movement across corporate networks.
The zero-click nature of the attack significantly increases the attack surface, as users remain unaware that their credentials have been compromised.
Additionally, the automatic download of remote binaries creates opportunities for attackers to stage malicious payloads on target systems.
When looking at desktop shortcuts to programs like Chrome, for example, the icon is rendered even if no IconLocation is configured.

While these files aren’t immediately executed, their presence establishes a foothold for future attacks, including malware deployment, ransomware, and credential harvesting operations.
Responsible Disclosure
Cymulate researchers followed responsible disclosure practices by reporting their findings to the Microsoft Security Response Center (MSRC), which has officially recognized the vulnerability with the CVE-2025-50154 identifier.
Even without instant execution, the ability to stage a malicious binary in this way poses a serious risk, as it sets the groundwork for more advanced and damaging attacks.The file is retrieved, as shown in Wireshark exports
Microsoft is expected to release a comprehensive security update to address the bypass technique.
The discovery underscores the challenges of creating complete security patches and highlights the importance of thorough vulnerability testing.
Even after vendor patches are applied, organizations should implement defense-in-depth strategies and continuous security monitoring to protect against potential bypass techniques.
Security experts recommend that organizations maintain vigilance even for patched vulnerabilities and consider additional protective measures such as network segmentation, privileged access management, and regular security assessments to mitigate risks from both known and unknown attack vectors.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




