A critical security vulnerability in the popular “Alone” WordPress theme has been actively exploited by cybercriminals to gain complete control of vulnerable websites.
The vulnerability, which affects a theme with over 9,000 sales, allows unauthenticated attackers to upload malicious files and execute remote code, leading to full site compromise.
The vulnerability was first submitted to security researchers on May 30, 2025, affecting the “Alone – Charity Multipurpose Non-profit WordPress Theme,” a widely-used template designed for non-profit organizations, churches, and political campaigns.
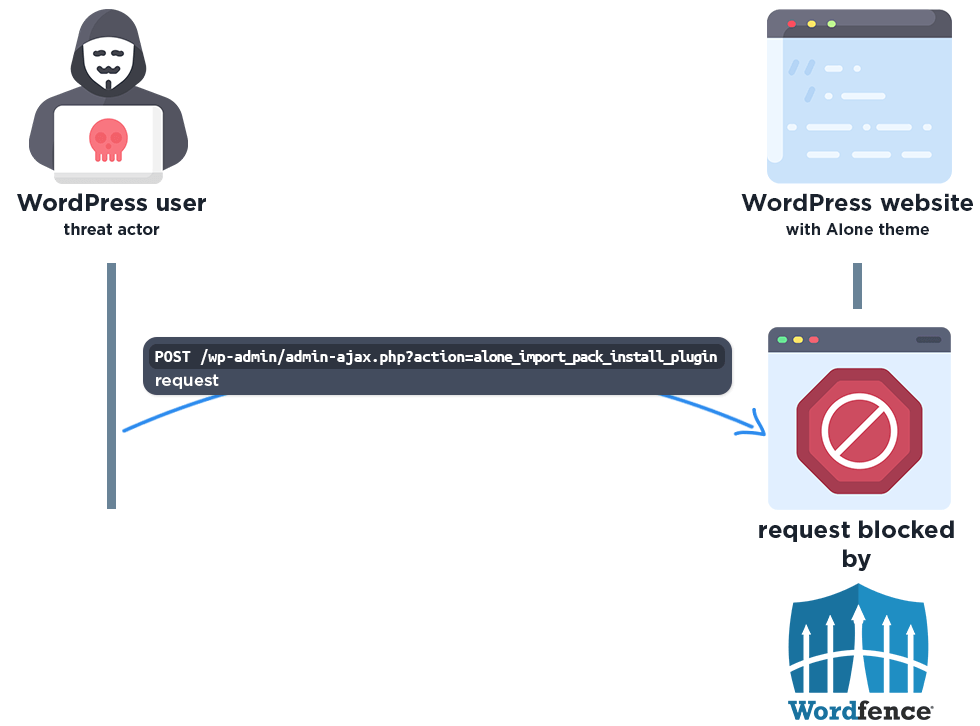
Free version users received protection after the standard 30-day delay on June 29, 2025. The firewall effectively blocks malicious requests by detecting the suspicious AJAX action and verifying that requests originate from authorized administrators.
The security vulnerability, assigned CVE-2025-5394 with a critical CVSS rating of 9.8, represents one of the most severe types of vulnerabilities that can affect WordPress sites.
The theme’s popularity among charitable organizations and religious institutions makes this vulnerability particularly concerning, as these sites often handle sensitive donor information and personal data.
The timeline of events reveals a troubling pattern common in modern cybersecurity incidents.
While the vendor released a patched version on June 16, 2025, updating the theme to version 7.8.5, attackers began exploiting the vulnerability on July 12, 2025 – two days before the public disclosure on July 14, 2025.
WordPress Theme RCE Vulnerability
The technical details of the vulnerability reveal a fundamental security oversight in the theme’s code. The vulnerability exists in the alone_import_pack_install_plugin() function, which lacks proper capability checks and nonce verification.
This function is accessible to unauthenticated users through the WordPress AJAX system, specifically via the ‘wp_ajax_nopriv_alone_import_pack_install_plugin’ action.
The vulnerability allows attackers to install plugins not only from the WordPress repository but also from remote sources by manipulating the ‘plugin_source’ parameter.
Attackers exploit this vulnerability by sending specially crafted POST requests to the vulnerable WordPress installation’s admin-ajax.php endpoint.
Security researchers have documented over 120,900 blocked exploit attempts since the vulnerability became known to attackers, highlighting the severity and widespread targeting of this security issue.
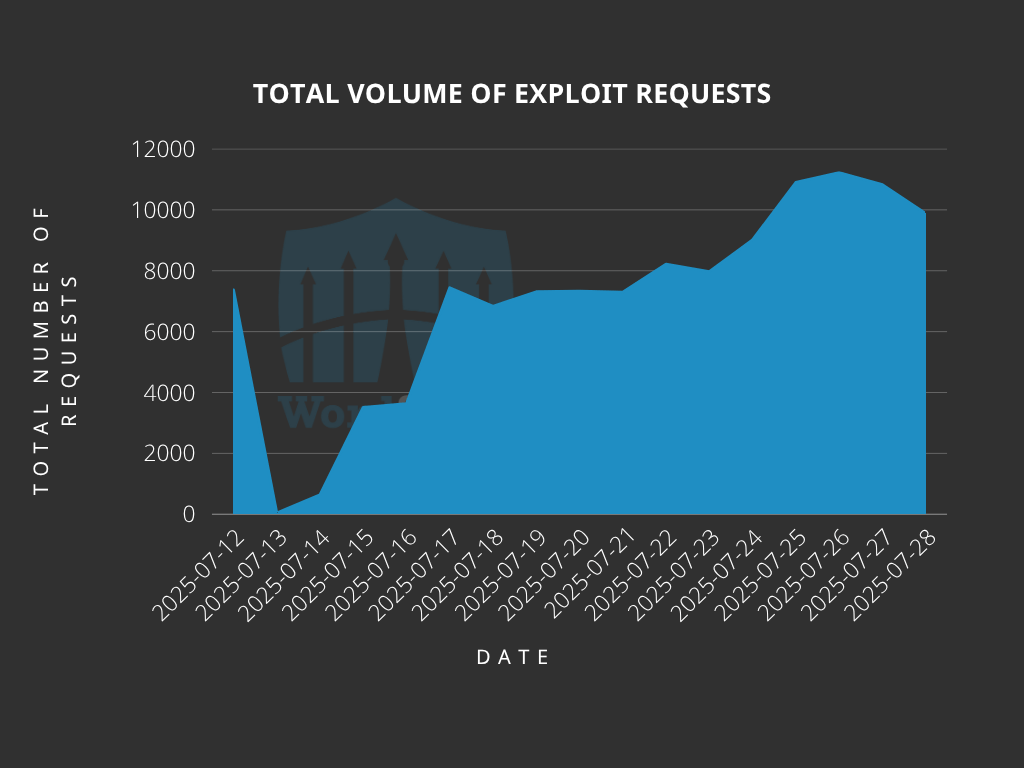
This indicates that malicious actors are actively monitoring software changesets and security patches to identify and exploit newly discovered vulnerabilities before widespread awareness can drive adoption of fixes.
The malicious requests include parameters that trick the theme into downloading and installing ZIP files containing webshells disguised as legitimate plugins.
Once installed, these webshells provide attackers with persistent access to the compromised website, enabling them to steal data, modify content, inject malicious code, or use the site for further attacks.
The researcher Thái An, who discovered this vulnerability, was awarded a $501 bounty for the responsible disclosure.
Massive Attack Campaign Blocked
Security data reveals the scale and sophistication of the ongoing attack campaign targeting this vulnerability.
Wordfence Premium, Care, and Response users received immediate protection through firewall rules deployed on May 30, 2025, the same day the vulnerability was reported.
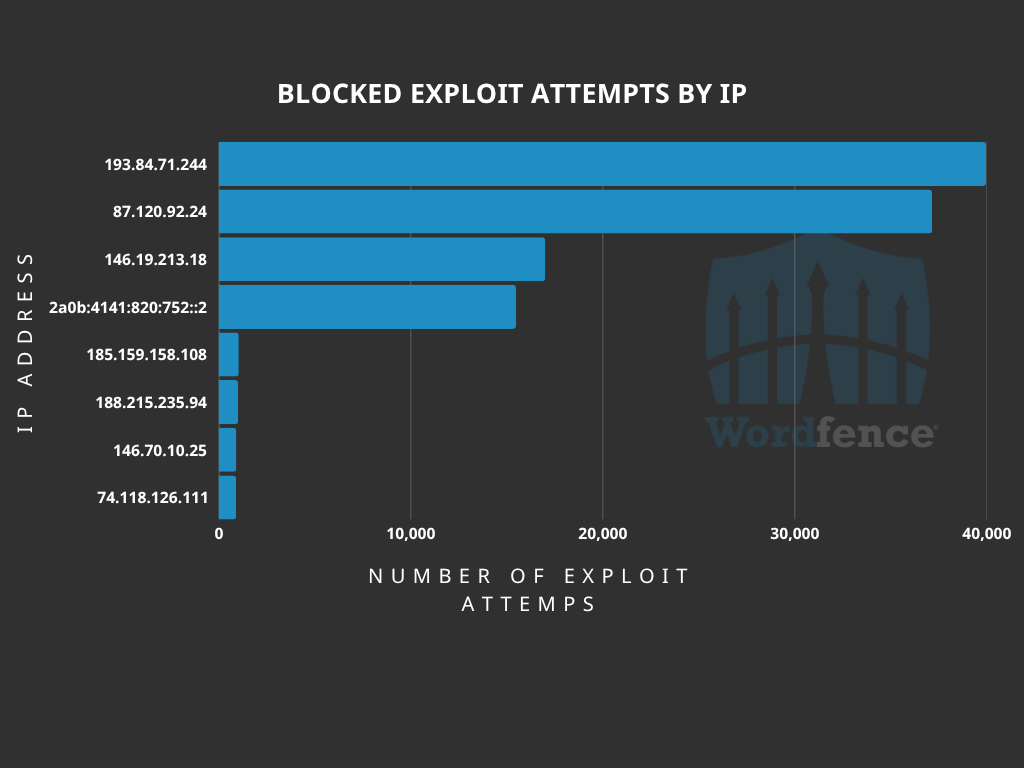
The Wordfence security platform has documented exploit attempts from numerous IP addresses, with the most active sources generating tens of thousands of malicious requests.
The top attacking IP address, 193.84.71.244, has been responsible for over 39,900 blocked requests, while 87.120.92.24 generated more than 37,100 attempts, demonstrating the automated and persistent nature of these attacks.
Security experts strongly urge all users of the Alone theme to immediately update to version 7.8.5 or later, as the vulnerability remains under active exploitation and represents a critical threat to website security and data integrity.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




