A critical security vulnerability in the popular Post SMTP WordPress plugin has left over 400,000 websites exposed to potential account takeover attacks, allowing even the lowest-privileged users to gain administrator access and achieve full site control.
The vulnerability, tracked as CVE-2025-24000, stems from broken authentication mechanisms in the plugin’s REST API endpoints and has been patched in version 3.3.0 following responsible disclosure through Patchstack’s bug bounty program.
The vulnerability affects Post SMTP versions 3.2.0 and below, exploiting inadequate access control mechanisms that only verify user login status rather than appropriate privilege levels.
This fundamental security oversight enables any registered user, including subscriber-level accounts with minimal permissions, to perform administrative functions typically reserved for site administrators.
The most dangerous capability exposed through this vulnerability is the ability to view detailed email logs containing complete email bodies and headers.
This access allows attackers to intercept password reset emails sent to administrator accounts, providing them with the credentials needed to compromise high-privilege accounts.
Once an attacker gains administrator access, they can achieve complete site takeover, including the ability to install malicious plugins, modify content, and access sensitive user data.
Post SMTP, developed by WPExperts’ Saad Iqbal, serves as an email delivery solution that enables WordPress site owners to configure custom mailer services with features including email logging, DNS validation, and OAuth support.

The plugin’s widespread adoption across more than 400,000 installations amplifies the potential impact of this security vulnerability.
WordPress Post SMTP Plugin Vulnerability
Security researchers identified the root cause in the plugin’s get_logs_permission function, which performs insufficient validation of user capabilities.
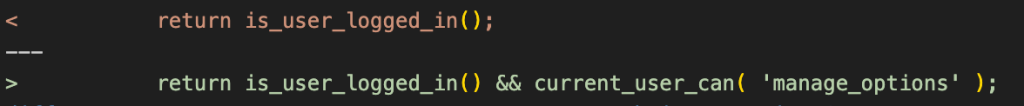
The vulnerable code only checks whether a user is logged in using the is_user_logged_in() function, without verifying whether the user possesses the necessary administrative privileges to access sensitive functionality.
Multiple REST API endpoints rely exclusively on this flawed permission check, including routes for viewing email statistics, resending emails, and accessing detailed email logs.
The /get-details endpoint, in particular, allows unauthorized users to retrieve complete email transcripts and session information that should remain restricted to administrators.
The vulnerability was discovered and reported by Denver Jackson, a member of the Patchstack Alliance community, through Patchstack’s Zero Day bug bounty program for WordPress.
This responsible disclosure process enabled developers to address the security vulnerability before public exploitation could occur.
Security Experts Urge Immediate Updates
Version 3.3.0 addresses the vulnerability by implementing proper capability checks within the get_logs_permission function.
Website administrators using Post SMTP are strongly advised to update immediately to version 3.3.0 or later to protect against potential exploitation.
The updated code now validates that users possess the manage_options capability, effectively restricting access to administrator-level accounts and resolving the broken access control issues.
Security experts emphasize that this incident highlights broader security considerations for WordPress plugin development.
The assumption that any logged-in user should have access to administrative functionality represents a fundamental misunderstanding of WordPress’s permission model, particularly given the variety of user roles available on typical WordPress installations.
Organizations should also review their user management practices and conduct security audits to identify similar vulnerabilities across their WordPress installations.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.
.webp?w=696&resize=696,0&ssl=1)
.webp?w=356&resize=356,220&ssl=1)




