Security researchers have revealed alarming details about how attackers are exploiting recently disclosed Microsoft SharePoint vulnerabilities to steal critical IIS Machine Keys, potentially giving hackers persistent backdoor access to compromised servers.
The exploitation campaign, which began approximately 10 days ago, leverages CVE-2025-53770 and CVE-2025-53771 to execute a sophisticated attack chain that ultimately compromises the security foundation of IIS web servers.
These keys serve as critical security components in IIS and ASP.NET environments, responsible for validating and encrypting sensitive data including VIEWSTATE, cookies, and session state information.
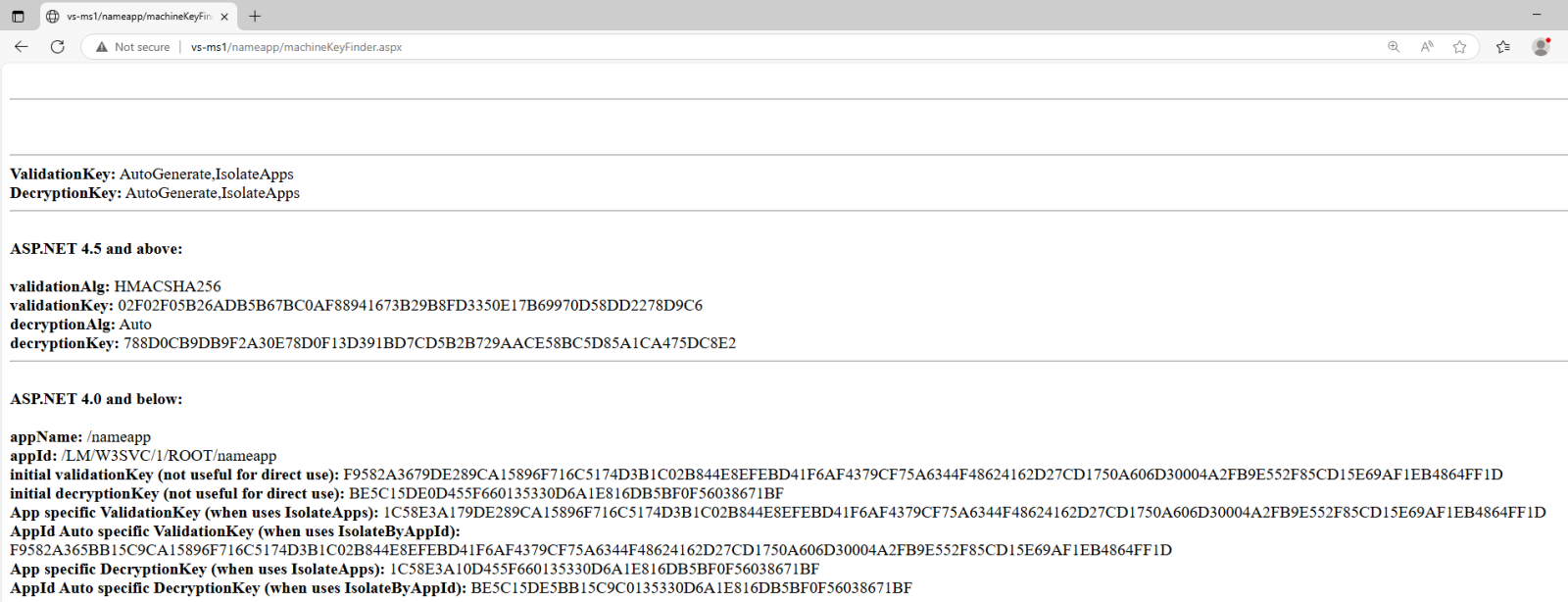
Attackers have been deploying malicious ASPX files that attempt to extract Machine Keys directly from web.config files where they are often stored in plain text.
The deployed script uses reflection to access the System.Web.Configuration.MachineKeySection class and retrieve both validation and decryption keys along with their associated algorithms.
The SharePoint deserialization vulnerabilities allow attackers to execute arbitrary commands on vulnerable servers, but researchers have discovered that most exploitation attempts follow a specific pattern focused on stealing IIS Machine Keys.
By default, IIS (even the very latest version on Windows server 2025) will enable VIEWSTATE MAC (Message Authentication Code) validation but will leave encryption on “Auto” which means that it is not used.
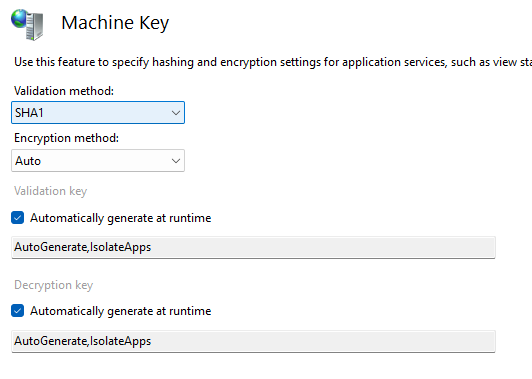
Machine Key, as you can probably guess by now, is used to perform validation – again, by default SHA1 is used.
When Machine Keys are stored in configuration files—a common practice in load-balanced server environments—this technique proves highly effective in exposing the sensitive cryptographic material to unauthorized parties.
SharePoint Deserialization Vulnerabilities
Even when Machine Keys are automatically generated by IIS and stored in the Windows Registry rather than configuration files, attackers are not deterred from their objectives.
Security researcher Soroush Dalili previously demonstrated that automatically generated Machine Keys remain accessible to attackers who achieve code execution on the target server.
Advanced ASPX scripts can systematically search through all potential Registry locations where Machine Keys might be stored, effectively bypassing the apparent security benefit of automatic key generation.
This discovery highlights a fundamental security weakness: once attackers gain any level of code execution on an IIS server, there are no technical controls preventing them from accessing Machine Keys regardless of storage location.
The persistence of these keys across system reboots further compounds the security risk, as compromised keys continue to pose threats until administrators manually regenerate them.
Persistent Backdoor Access
The theft of Machine Keys represents more than a simple data breach—it provides attackers with the capability to achieve persistent remote code execution through VIEWSTATE manipulation.
According to Report, SharePoint vulnerability, attackers retain access through any web application running on the same server.
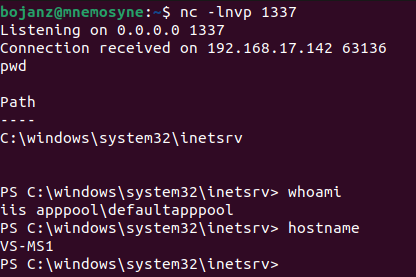
Using tools like ysoserial.net, attackers can craft malicious VIEWSTATE objects that, when processed by the server, trigger deserialization vulnerabilities leading to arbitrary code execution.
The backdoor mechanism proves particularly insidious because malicious VIEWSTATE parameters can be submitted to any ASPX application on the compromised server, not just the originally vulnerable component.
Organizations can detect ongoing exploitation attempts by monitoring Windows Application Event Code 4009, which logs VIEWSTATE verification failures.
However, prevention requires immediate Machine Key regeneration on any server suspected of compromise, as Windows does not automatically refresh these critical security components.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.
.webp?w=696&resize=696,0&ssl=1)
.webp?w=356&resize=356,220&ssl=1)




