Security researchers from FortiGuard have uncovered a sophisticated web shell script, “UpdateChecker.aspx,” that grants attackers comprehensive remote control over compromised Microsoft IIS servers.
The discovery is part of an ongoing investigation into cyber intrusions targeting critical national infrastructure in the Middle East.
Advanced Obfuscation Techniques Mask Malicious Code
The web shell employs extensive obfuscation methods to evade detection and analysis.
The ASPX webpage file contains heavily obfuscated C# code, where readable elements, such as method names, variable names, and class names, are randomly generated and encoded in Unicode.
All constant values, including strings and numbers, are either encrypted or encoded to conceal the script’s proper functionality.
The malicious code executes exclusively on the server side through the Page_Load() function, which serves as the entry point when attackers send remote commands to the compromised webpage.
Traffic analysis reveals that control commands must be transmitted through HTTP POST requests with specific content type requirements, returning error pages if these conditions aren’t met.
Encrypted JSON Commands Enable Full System Control
The web shell’s communication protocol employs a sophisticated encryption scheme, where command data is first encrypted and then encoded in Base64 before transmission.
The first 16 bytes contain an encrypted key using hardcoded values, which decrypts to reveal a 15-byte key for decrypting subsequent command data.
Both commands and results are formatted in JSON before encryption, requiring specific keys including ProtocolVersion, ModuleName, and RequestName.
The script’s functionality is organized into three distinct modules. The Base module collects server information, including software details, IP addresses, and system specifications.
The CommandShell module allows execution of Windows commands with IIS privileges.
Most comprehensively, the FileManager module provides extensive file and directory operations, including creation, deletion, moving, copying, content searching, and manipulation capabilities.
Demonstration Reveals Extensive Remote Capabilities
Researchers successfully simulated attacker interactions using a custom Python script, demonstrating the web shell’s full range of capabilities.
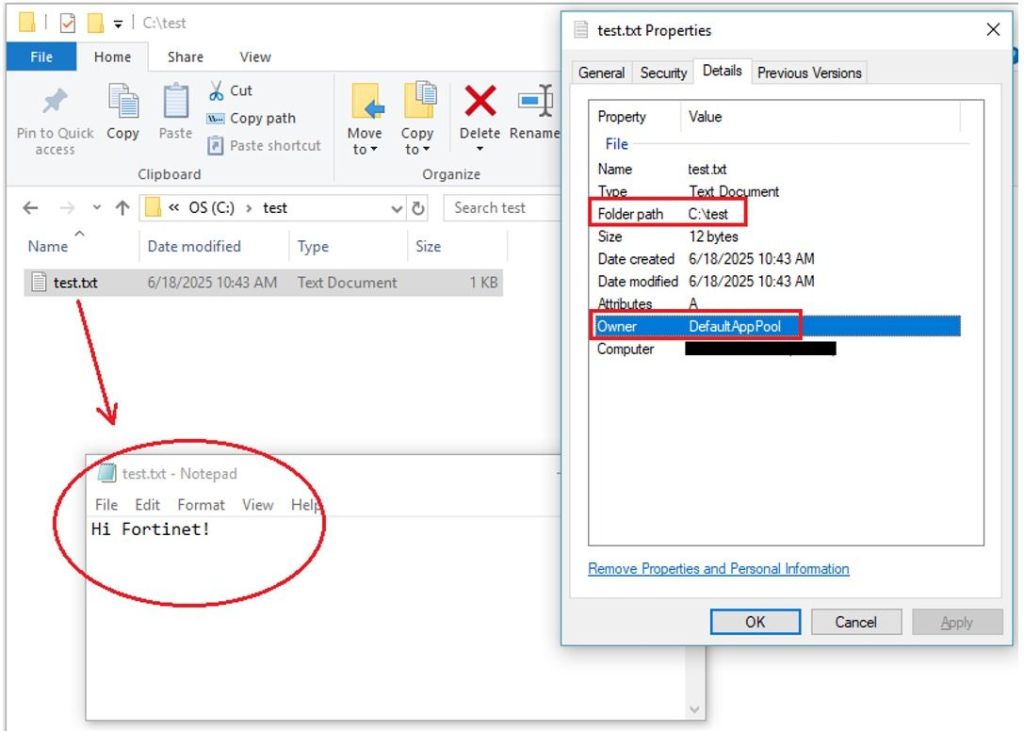
Tests demonstrated the ability to gather server information, execute system commands such as “whoami,” and perform complex file operations, including creating directories, writing content to files, and retrieving data remotely.
Files created through the web shell showed ownership by DefaultAppPool, confirming execution under the IIS service identity.
Fortinet customers receive protection through the FortiGuard Antivirus service, which detects the threat as ASP/WebShell. 32BC!tr.
The company recommends organizations contact their Global FortiGuard Incident Response Team if they suspect compromise from this or similar cybersecurity threats.
IOCs
Relevant Sample SHA-256:
[UpdateChecker.aspx]
A841C8179AC48BDC2EBF1E646D4F552D9CD02FC79207FDC2FC783889049F32BC






