Cybersecurity researchers at AhnLab Security Intelligence Center (ASEC) have uncovered a significant evolution in the distribution tactics of RokRAT malware, with threat actors now leveraging weaponized Hangul Word Processor (.hwp) documents instead of their traditional shortcut file methods.
This shift represents a concerning adaptation in the malware’s delivery mechanism, targeting users through seemingly legitimate document files related to North Korean grain distribution operations.
Sophisticated Social Engineering Through Document Weaponization
The attack campaign employs carefully crafted HWP documents with names designed to appear legitimate, including “250615_Operation status of grain store.hwp, “Recent major portal site.hwpx,” and “[Notice] Q1 VAT Return Filing Deadline (Final).”
The primary document contains content about North Korea’s grain distribution points, maintaining thematic consistency with its filename to avoid raising suspicions among potential victims.
The malicious payload is activated through a hyperlink embedded at the bottom of the document, disguised as “[Appendix] Reference Materials.docx.” When clicked, this hyperlink triggers a warning dialog asking users to execute ShellRunas.exe from the %TEMP% directory.
Crucially, this executable is not downloaded from external command-and-control servers but is embedded within the document as an OLE (Object Linking and Embedding) object, automatically extracted by the Hangul process when the document is accessed.
Advanced DLL Side-Loading Attack Chain
The attack employs a sophisticated DLL side-loading technique using legitimate, Microsoft-signed executables.
ShellRunas.exe serves as the primary loader, which then loads the malicious credui.dll from the same directory.
ASEC researchers identified multiple legitimate programs being exploited in similar attacks, including accessenum.exe (which loads mpr.dll) and hhc.exe (which loads hha.dll), demonstrating the versatility of this attack vector.
The credui.dll component initiates the next stage by downloading a file named “Father.jpg” from Dropbox.
Despite its image file extension, this file contains embedded shellcode designed to load the final RokRAT payload directly into system memory.
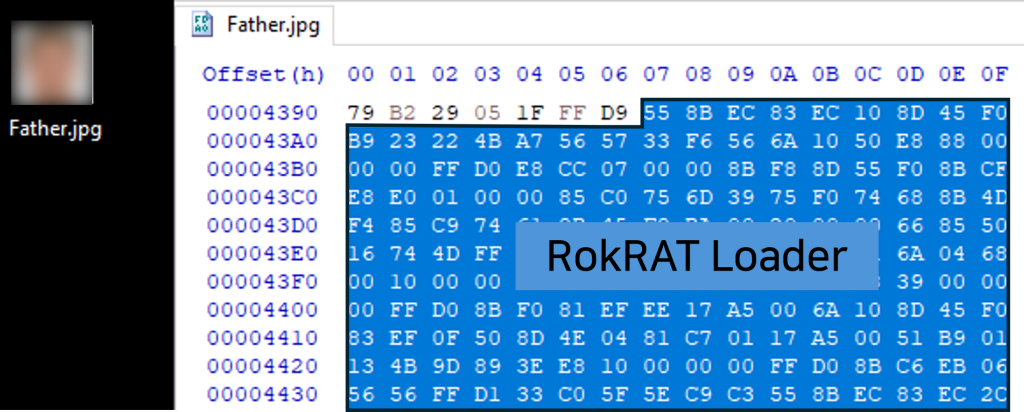
This steganographic approach enables the malware to evade traditional file-based detection systems by concealing malicious code within seemingly benign image files.
Persistent Threat Capabilities
Once fully deployed, RokRAT demonstrates extensive surveillance capabilities, including the collection of comprehensive user information and the ability to execute various malicious commands as directed by the threat actors.
The malware’s evolution to use HWP documents represents a significant concern for organizations and individuals who regularly handle Korean-language documents, particularly those dealing with sensitive governmental or business information.
Security experts recommend enhanced vigilance when handling HWP documents from unknown sources and implementing robust endpoint detection systems that can identify suspicious OLE object behavior and DLL side-loading activities.
IOC
- a2ee8d2aa9f79551eb5dd8f9610ad557
- d5fe744b9623a0cc7f0ef6464c5530da
- e13c3a38ca58fb0fa9da753e857dd3d5






