Cybersecurity researchers have uncovered a sophisticated credential-stealing malware known as Octalyn, publicly hosted on GitHub under the guise of a “forensic research tool.”
Despite its educational facade, the malware functions as a full-fledged data thief capable of extracting browser passwords, VPN configurations, cryptocurrency wallet data, and Discord tokens through a highly organized file structure that streamlines data theft operations.
Sophisticated Multi-Stage Attack Process
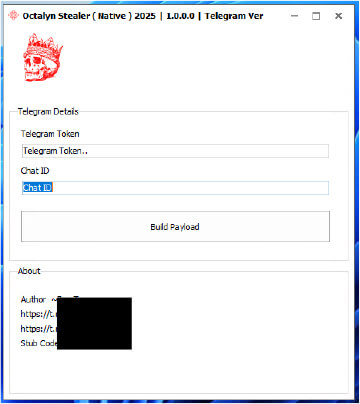
The Octalyn toolkit employs a dual-language architecture combining C++ payload modules with a Delphi-based builder interface, making it accessible to low-skilled threat actors.
The malware’s execution begins with Build.exe, which acts as a dropper with an entropy score above 7, indicating heavy obfuscation designed to evade security analysis.
Upon execution, the dropper extracts three embedded executables —TelegramBuild.exe, rvn.exe, and assembly.exe—into the system’s temporary directory using Windows API functions such as GetTempPathA and ShellExecuteA.
The primary malicious component, TelegramBuild.exe, creates a working directory named “0ctalyn” within the system’s TEMP folder, establishing organized subdirectories including “Cryptowallets,” “Extension,” “Games,” “Socials,” and “VPN.”
This systematic approach enables the malware to categorize stolen data efficiently, with individual files, such as cookies.txt, passwords.txt, and autofill.txt, providing structured access to the harvested information.
Technical analysis reveals that the malware targets Chromium-based browsers, including Google Chrome, Microsoft Edge, and Opera, extracting cookies through Chrome’s local encryption keys.
The cryptocurrency wallet targeting capability is particularly concerning, as it creates individual folders for Bitcoin, Ethereum, Litecoin, and Monero, harvesting private keys, seed phrases, and wallet.dat files.
Telegram-Based Data Exfiltration and Persistence Mechanisms
The malware establishes persistence through multiple mechanisms, copying rvn.exe to the user’s Startup folder and modifying Windows Registry Run keys under HKCU\Software\Microsoft\Windows\CurrentVersion\Run.
This dual-layer approach ensures continuous operation across system restarts.
Data exfiltration occurs through encrypted TLS connections to Telegram API endpoints (api.telegram.org), requiring only a Telegram bot token and chat ID for configuration.
The malware transmits uniquely identified ZIP files incorporating the victim’s username, typically formatted as “OctalynRetrieved.zip,” allowing threat actors to track multiple infections efficiently.
Additionally, the malware utilizes Base64-encoded PowerShell commands to download secondary payloads from GitHub repositories; however, the specific payload was unavailable during analysis.
The infrastructure remains active, indicating ongoing control by the threat actor.
Security researchers have identified specific file hashes, including 8bd9925f7b7663ca2fcb305870248bd5de0c684342c364c24ef24bffbcdecd8b, for the primary executable and provided YARA rules for detection.
Organizations should monitor registry modifications, PowerShell usage with Base64 encoding, and restrict access to Telegram API domains to prevent successful infections.
.jpg?w=696&resize=696,0&ssl=1)





