RapidFire Tools’ Network Detective, a widely used network assessment and reporting utility, has been found to expose critical credentials through two distinct vulnerabilities that undermine the confidentiality and integrity of client infrastructures.
Security researchers have assigned CVE-2025-32353 and CVE-2025-32874 to these flaws, which respectively involve the storage of plaintext passwords in local temporary files and the use of a deterministic, reversible encryption routine embedded in the application binary.
Together, these weaknesses enable local attackers or malicious insiders to harvest administrator-level usernames and passwords often used for services like VMware ESXi without needing special decryption tools or elevated privileges beyond read access to the host’s file system.
Plaintext Password Storage
During the routine execution of network scans, Network Detective writes usernames and passwords directly into a series of temporary files under the directory. %PROGRAMFILES%\NetworkDetective\DataCollector\bin\tmp\ndc.
Among these files are collection.txt, ndfRun.log, and run. ndp. All of these contain sensitive credentials in cleartext.
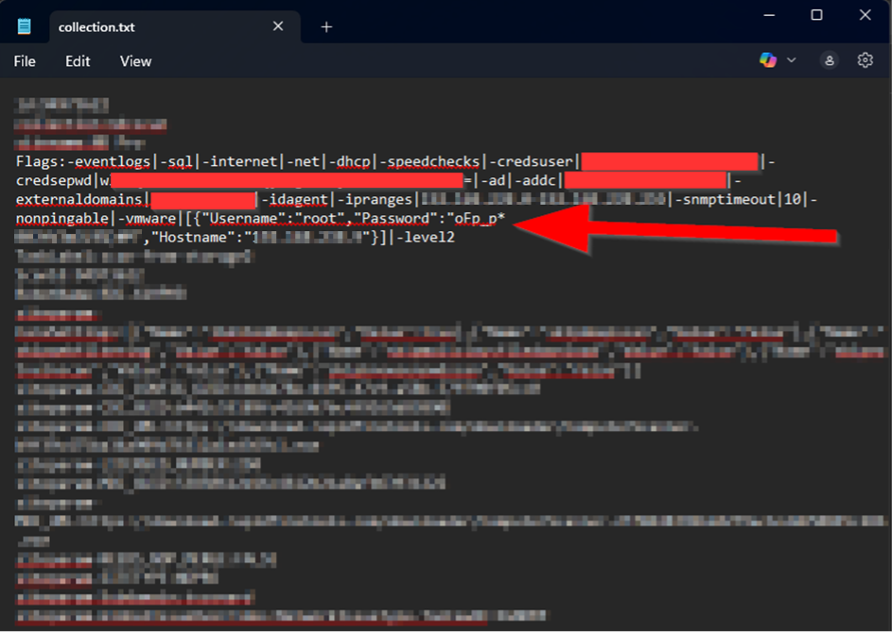
When the tool packages scan results into an archive named ndscan-########.ndf, it includes these duplicate files, effectively preserving unprotected passwords long after the scan completes.
Because these files are neither encrypted nor access-controlled, any process or user with read permissions to the application’s installation path can recover administrative credentials.
In practice, this means that an attacker who gains physical or remote access, even via a low-privilege account, can escalate privileges quickly and move laterally across the environment by reusing these exposed credentials.
Beyond the immediate risk of credential leakage, the presence of plaintext passwords also contravenes industry best practices such as those outlined in the CWE-312 and CWE-532 vulnerability classifications, which call for secure handling and obfuscation of sensitive information.
The absence of warnings or documentation indicating that stored scan credentials are insecure further compounds the problem, leading many administrators to assume that a trusted vendor tool would not undermine their own security posture.
Flawed Encryption Mechanisms
In addition to cleartext storage, Network Detective employs a homegrown encryption scheme for protecting certain data elements that is fundamentally broken.
Analysis of the RemoteDataCollectorSetup.exe binary reveals two nearly identical encryption routines, one labeled “FIPS” and the other “non-FIPS,” both of which derive keys and initialization vectors (IVs) from hardcoded static values and a constant salt string, “Ivan Medvedev.”
Because the key derivation function produces the same key/IV pair for any given input every time, ciphertexts are predictable and reversible.
An attacker in possession of the binary or its log files can extract the static salt and built-in key material, then run a simple decryption routine to recover any “encrypted” passwords embedded in logs.
This flaw falls squarely under CWE-326 and CWE-329, reflecting inadequate encryption strength and the failure to use a random IV in CBC mode.
The combination of these two vulnerabilities grants a powerful attack vector: cleartext passwords can be complemented by reversing any additional encrypted values, providing a comprehensive view of credentials used during scanning.
Organizations that rely on Network Detective for vulnerability assessments thus face an urgent need to remediate.
Mitigation and Recommendations
RapidFire Tools has released an updated version of Network Detective that addresses both issues by eliminating plaintext credential dumps and replacing the deterministic encryption algorithm with an industry-standard authenticated encryption mode.
Administrators are strongly advised to upgrade immediately, verify the removal of files in the temporary collection directory, and rotate all credentials previously scanned by the tool.
Only through these coordinated steps can the confidentiality and integrity of sensitive network credentials be restored.
.jpg?w=696&resize=696,0&ssl=1)





