In the aftermath of Israel’s June 2025 airstrikes on Iranian military and nuclear sites, the Middle East has witnessed not only a dramatic escalation in conventional warfare but also an unprecedented wave of cyber offensives.
Over 80 hacktivist groups, primarily pro-Iranian and pro-Palestinian, have mobilized to launch coordinated cyberattacks, targeting Israel and its allies across more than 20 critical industry sectors.
Cybersecurity experts warn that the current digital onslaught is not solely the work of independent activists.
Evidence suggests that several attacks are being carried out by so-called “faketivist” groups, nation-state actors masquerading as hacktivists to obscure attribution and escalate the conflict under a veil of plausible deniability.
Technical Scope: Critical Infrastructure in the Crosshairs
The breadth of targeted sectors is staggering. Claimed attacks span government agencies, military contractors, judicial systems, energy and water infrastructure, satellite communications, ICS/OT systems, financial institutions, and media networks. Notable incidents include:
- ICS/OT Attacks: Groups like GhostSec and SYLHET GANG SG claim to have compromised over 100 Modbus PLC devices, water control units, and Siemens S7 PLCs in Tel Aviv, threatening industrial safety and public utilities.
- Energy Sector Breaches: Handala Hack and Mr Hamza report data exfiltration and service disruptions at major Israeli oil and gas companies, including Delek Group and Haifa Refinery.
- Financial and Government Systems: Inteid and Dark Storm Team have targeted Israeli banks and ministries, while DieNet and Server Killers have attacked judicial and educational web infrastructure.
- Satellite and Media Networks: Arabian Ghosts and Cyber Islamic Resistance claim takedowns of satellite networks and radio services, amplifying psychological impact.
Attacks range from DDoS and defacement to sophisticated data exfiltration, ransomware deployment, and psychological operations, with some groups hinting at the use of custom malware and zero-day exploits.
Hacktivist Alliances and State-Sponsored “Faketivism”
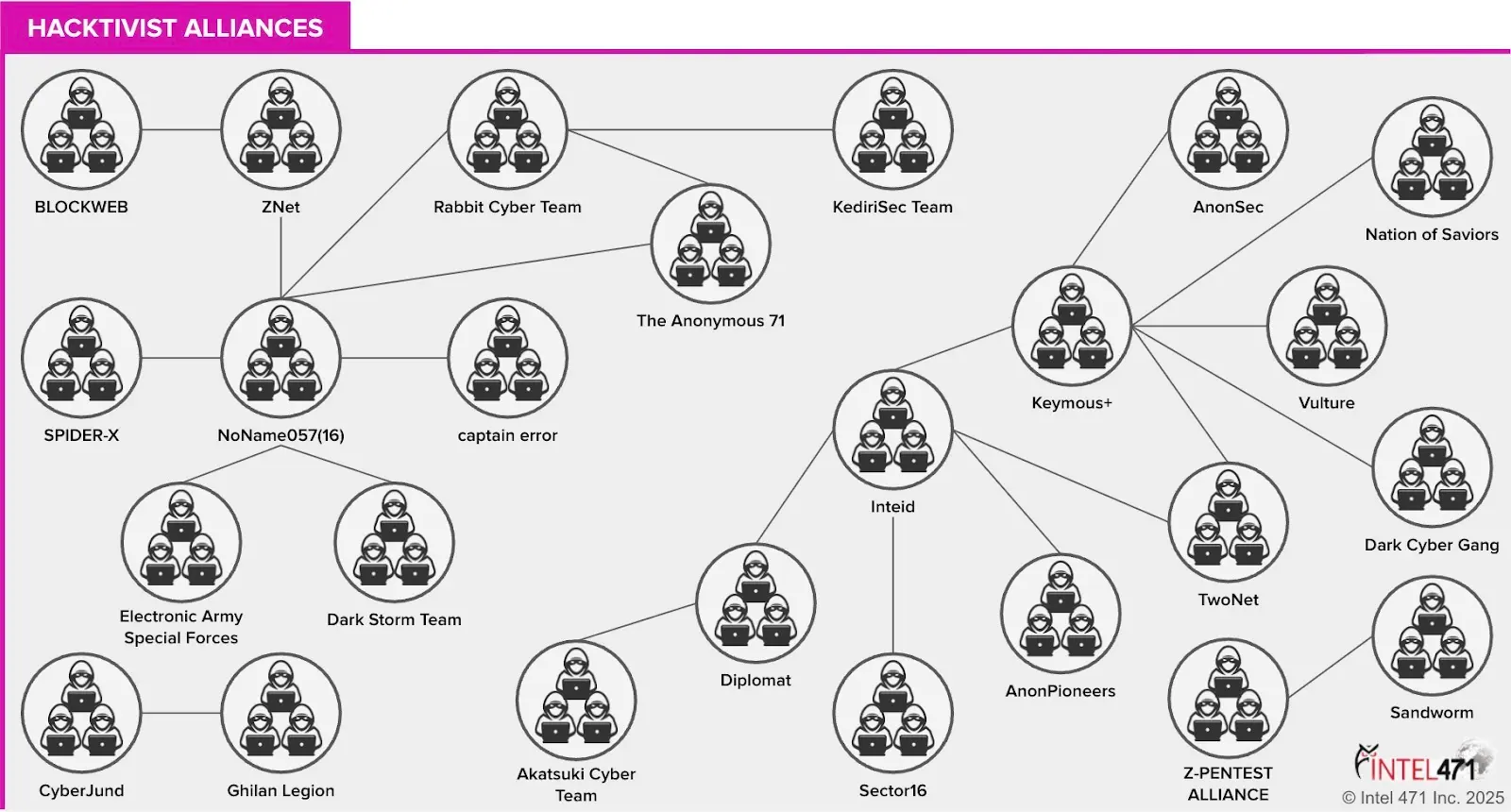
Operational alliances are a hallmark of this cyber offensive. Groups such as Mr Hamza, Mysterious Team Bangladesh, and Inteid are sharing resources, intelligence, and tools, like the Abyssal DDoS V3 botnet while coordinating attacks in real-time via Telegram and underground forums.
Analysis highlight the role of faketivist groups such as Cyber Av3ngers and Handala Hack, believed to be Iranian-controlled, and Predatory Sparrow, likely Israeli-backed.
These entities employ advanced tactics, including the development of ICS/SCADA exploits and wiper malware, blurring the line between grassroots hacktivism and state-directed cyber warfare.
Outlook: Heightened Cyber Risk and Global Implications
As geopolitical tensions remain high, the risk of further cyber escalation looms large. Experts anticipate continued DDoS campaigns, ransomware threats, and retaliatory strikes, potentially extending to Western and Arab allies of Israel.
Organizations worldwide are urged to strengthen their cyber defenses, as the digital battlefield has become a central front in modern conflict.
.webp?w=696&resize=696,0&ssl=1)





