The largest distributed denial-of-service (DDoS) attack ever recorded in mid-May 2025, reaching an unprecedented 7.3 terabits per second (Tbps) and delivering 37.4 terabytes of data in just 45 seconds.
This record-breaking cyber assault targeted a hosting provider customer using Cloudflare’s Magic Transit service and represents a 12% increase over the previous record, surpassing recent attacks by Tbps.
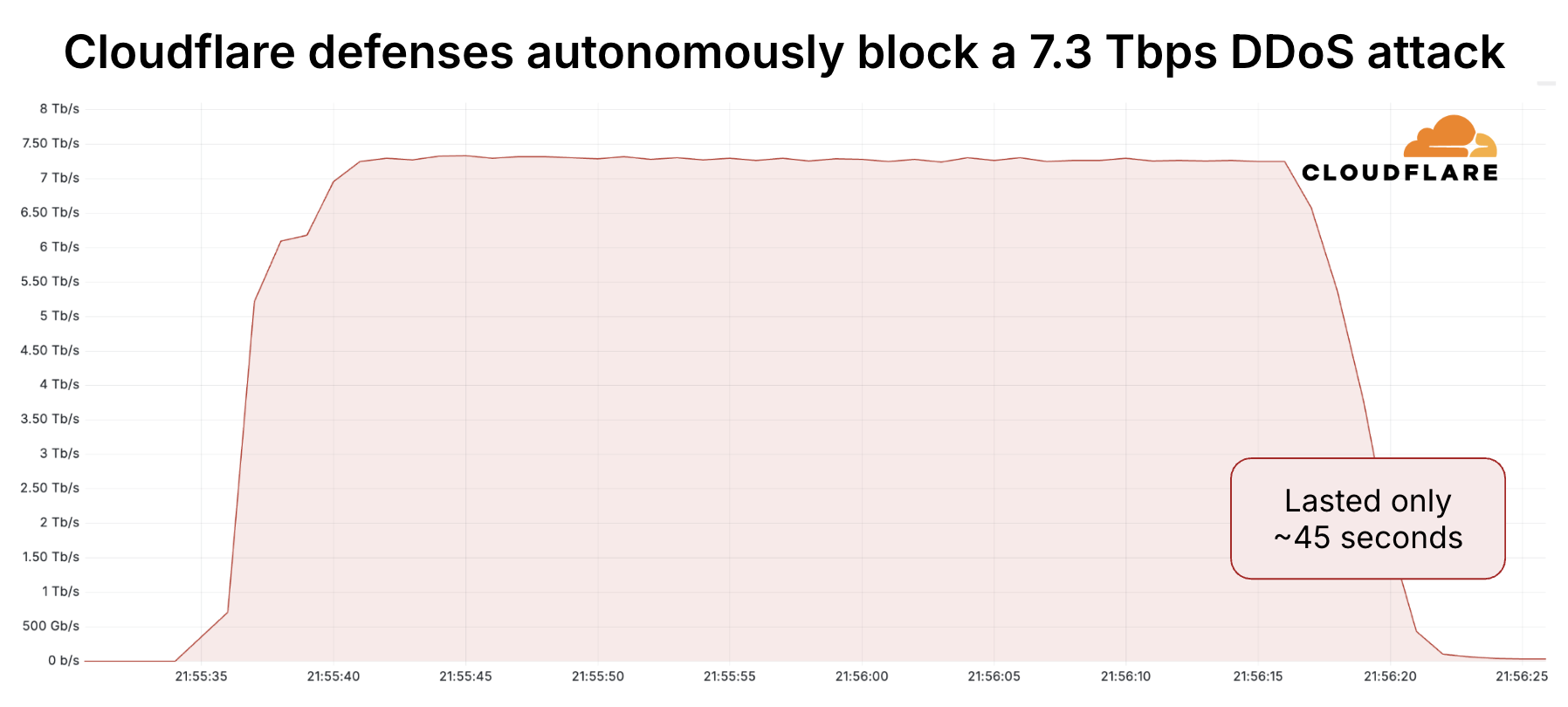
The attack was autonomously detected and mitigated across 477 data centers in 293 locations worldwide without human intervention, demonstrating the evolving scale and sophistication of modern DDoS threats against critical internet infrastructure.
The 7.3 Tbps attack delivered an staggering volume of data equivalent to flooding a network with over 9,350 full-length HD movies or streaming 7,480 hours of high-definition video in just 45 seconds.
To put this in perspective, the attack volume represents enough data to download 9.35 million songs in under a minute, providing enough music for 57 years of continuous listening.
The attack specifically targeted a single IP address owned by Cloudflare hosting provider customer, carpet-bombing an average of 21,925 destination ports with peaks reaching 34,517 destination ports per second.
The assault originated from a distributed network of over 122,145 source IP addresses spanning 5,433 Autonomous Systems across 161 countries, with Brazil and Vietnam accounting for approximately half of the attack traffic.
Among the top contributing networks, Telefonica Brazil accounted for 10.5% of the total attack traffic, followed closely by Viettel Group with 9.8%.
Other significant contributors included China Unicom, Chunghwa Telecom, and China Telecom, collectively representing substantial portions of the global attack infrastructure.
Technical Analysis and Attack Vectors
The attack employed multiple vectors, with 99.996% consisting of UDP floods while the remaining 0.004% utilized various reflection and amplification techniques.
The detection system employs real-time fingerprinting technology that samples packets directly from the Linux kernel using eXpress Data Path (XDP) and extended Berkeley Packet Filter (eBPF) programs.
These secondary attack methods included QOTD reflection attacks, Echo reflection attacks, NTP reflection attacks, Mirai UDP flood attacks, Portmap floods, and RIPv1 amplification attacks.
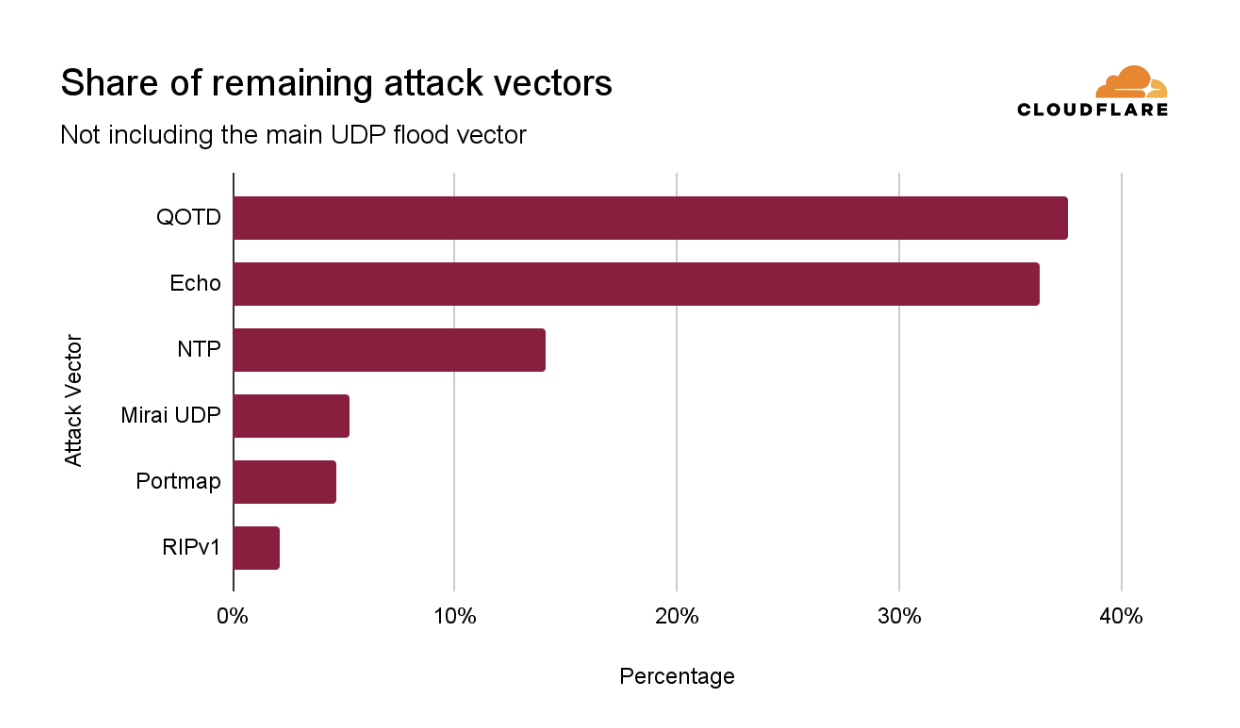
The diversity of attack vectors demonstrates the sophisticated nature of modern DDoS campaigns, combining high-volume flooding techniques with protocol-specific exploitation methods.
The use of reflection and amplification attacks allows attackers to multiply their effective attack power by abusing legitimate internet services and protocols.
Mitigations
According to Report, Cloudflare’s autonomous detection and mitigation systems successfully blocked the attack without triggering alerts or causing incidents.
The company’s global anycast network distributed the attack traffic across multiple data centers, using the attack’s distributed nature against itself to enable mitigation close to botnet nodes.
This sophisticated analysis identifies suspicious patterns through Cloudflare’s proprietary heuristic engine called “dosd” (denial of service daemon).
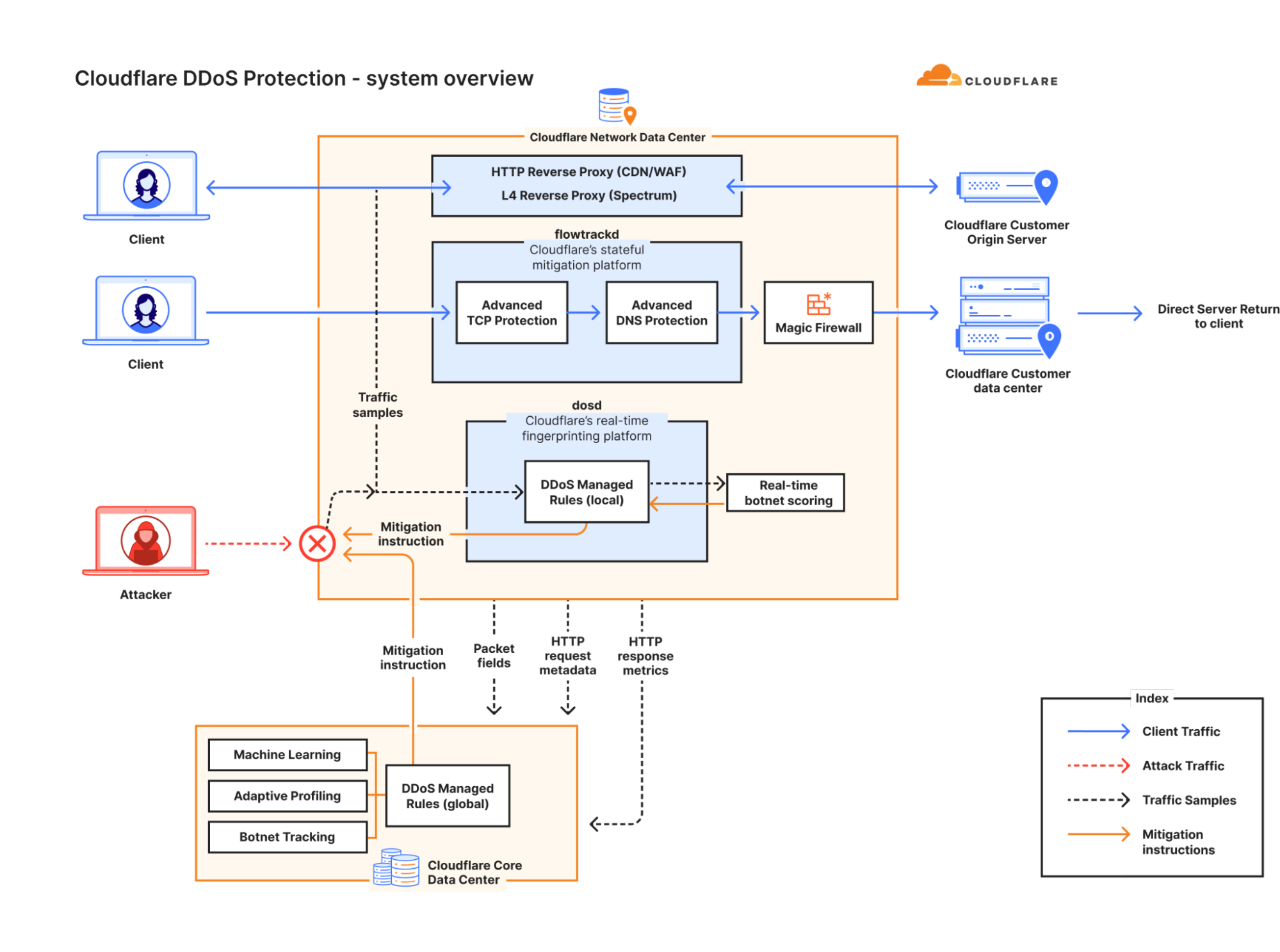
The system generates multiple fingerprint permutations to achieve the highest mitigation efficacy while avoiding impact to legitimate traffic.
When activation thresholds are exceeded, mitigation rules are compiled as eBPF programs to drop matching attack packets, with rules automatically timing out when attacks end.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.
.webp?w=696&resize=696,0&ssl=1)
.webp?w=356&resize=356,220&ssl=1)




