A sophisticated attack targeting a U.S. chemicals company, where threat actors exploited a critical SAP NetWeaver vulnerability to deploy the elusive Auto-Color backdoor malware.
The April 2025 incident represents the first documented case linking CVE-2025-31324 exploitation with Auto-Color deployment, highlighting the evolving threat landscape facing enterprise systems.
The attack centered around CVE-2025-31324, a critical vulnerability disclosed by SAP SE on April 24, 2025, affecting SAP NetWeaver applications.
This security vulnerabilityenables malicious actors to upload files to application servers, potentially achieving remote code execution and complete system compromise.
Despite urgent disclosure, the vulnerability has already been exploited across multiple systems worldwide.
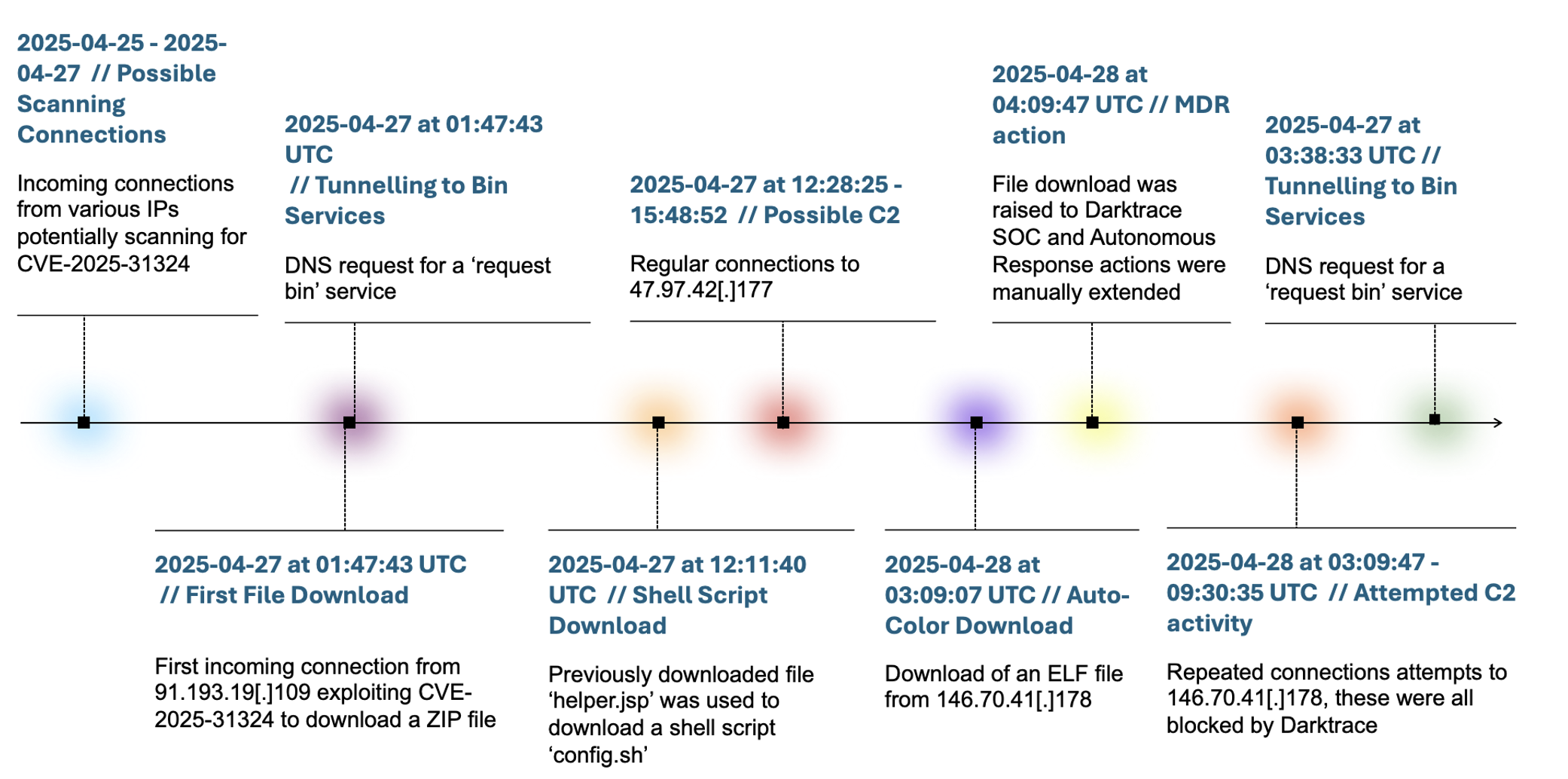
Darktrace’s investigation revealed the attack began on April 27, when threat actors initiated connections from the malicious IP address 91.193.19.109.
The exploitation was identified by the telltale URI pattern ‘/developmentserver/metadatauploader?CONTENTTYPE=MODEL&CLIENT=1’, accompanied by suspicious ZIP file downloads.
The compromised device immediately began making DNS requests to Out-of-Band Application Security Testing (OAST) domains, suggesting data exfiltration attempts through DNS tunneling.
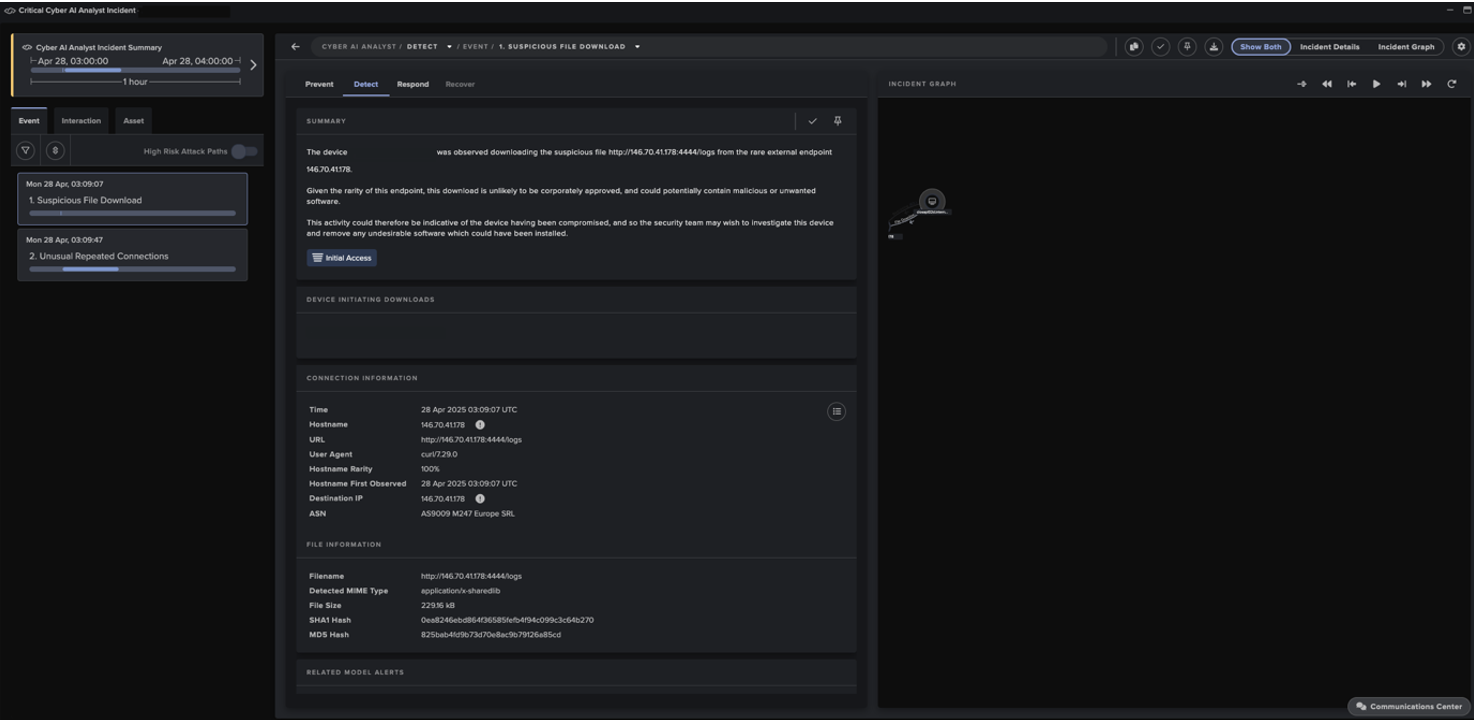
Less than 12 hours later, and just 24 hours after the initial exploit, the attacker downloaded an ELF file from http://146.70.41.178:4444/logs, which marked the delivery of the Auto-Color malware.
Over three days, attackers downloaded seven malicious files and established connections to multiple command-and-control infrastructure endpoints, including systems linked to Supershell, a C2 platform associated with China-affiliated threat groups.
SAP NetWeaver Vulnerability
Auto-Color, first observed in November 2024, represents a highly sophisticated Remote Access Trojan targeting Linux systems.
Named for its distinctive file path “/var/log/cross/auto-color”, the malware has primarily focused on universities and government institutions across the United States and Asia.
The malware’s most notable characteristic is its adaptive behavior based on execution privileges. When running without root access, Auto-Color operates with limited functionality to avoid detection.
However, with root privileges, it performs invasive installation procedures, deploying a malicious shared object library “libcext.so.2” that masquerades as legitimate system components.
Auto-Color achieves persistence through manipulation of the Linux /etc/ld.so.preload mechanism, inserting references to its malicious library.
This technique ensures the malware loads before legitimate libraries, enabling it to hijack standard system functions across virtually all applications.
Most significantly, Auto-Color employs suppression tactics when unable to establish command-and-control communication.
If the C2 server is unreachable, the malware remains largely dormant, appearing benign to security analysts and preventing reverse engineering efforts from uncovering its full capabilities.
Response Prevents Escalation
Darktrace’s Security Operations Centre addressed the initial compromise within hours, triggering multiple alerts that prompted immediate investigation.
The company’s Autonomous Response capability quickly intervened, enforcing “pattern of life” restrictions on the compromised device while maintaining normal business operations.
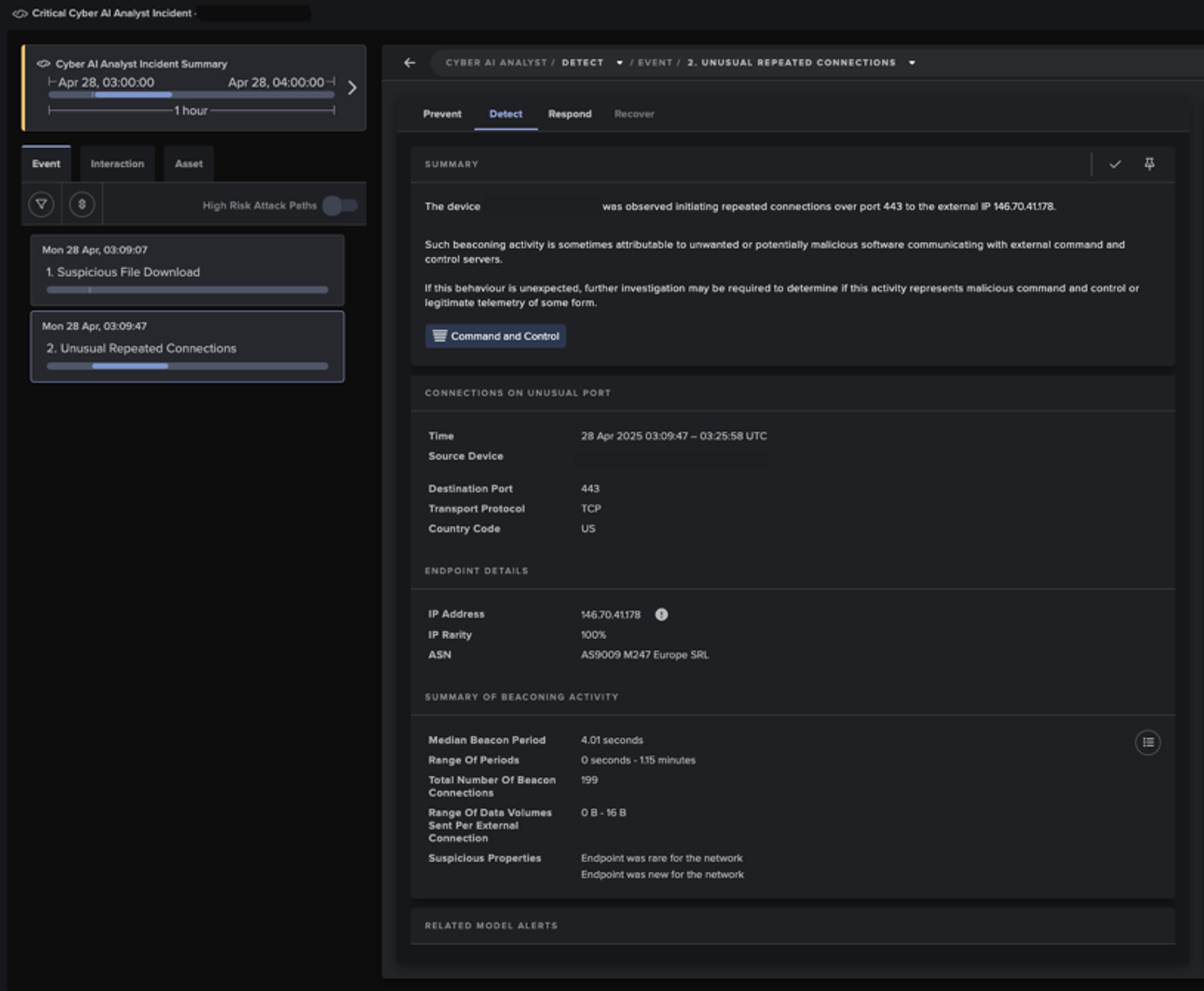
Throughout the attack, Darktrace detected numerous connection attempts to the C2 endpoint 146.70.41.178 over port 443.
The security system’s automated blocking prevented successful C2 establishment, effectively neutralizing the threat before it could fully execute its payload.
Analysis revealed Auto-Color’s modular C2 protocol supports various functions including reverse shell initiation, file manipulation, system proxy configuration, and even includes a kill switch for self-removal.
However, the malware’s dependence on live operator control through C2 communication became its weakness when blocked by automated defenses.
This incident underscores the critical importance of rapidly addressing high-severity vulnerabilities, as they can quickly escalate into persistent, damaging threats within organizational networks.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




