Cybercriminals are increasingly exploiting the Domain Name System (DNS) – often called the “phonebook of the internet” – to conduct covert command-and-control operations and data exfiltration.
This sophisticated attack method leverages DNS’s trusted status within corporate networks, where traffic typically passes through firewalls with minimal inspection, creating an ideal channel for malicious activities.
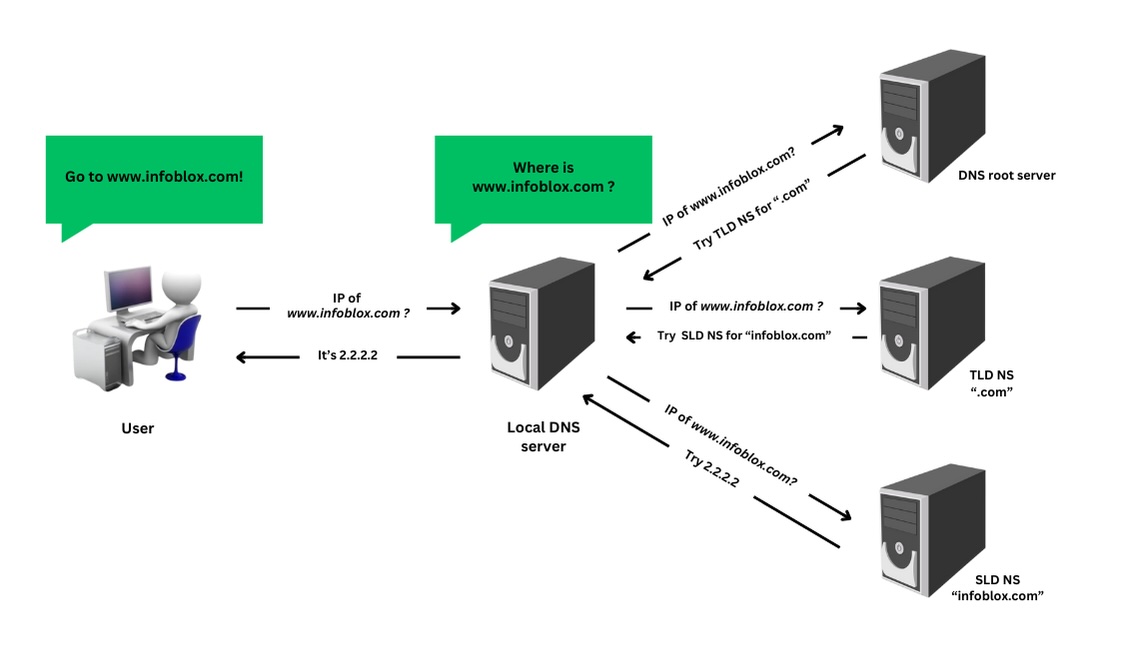
DNS tunneling involves encoding malicious data within legitimate DNS queries and responses, establishing a covert communication bridge between compromised systems and attacker-controlled servers.
The technique exploits the fundamental DNS resolution process, where attackers control a domain’s authoritative name server to communicate with malware installed on victim systems.
The attack mechanism operates through the standard DNS infrastructure without requiring direct communication between malware and command servers.
Instead, communication flows through the victim’s recursive name server, which maintains permissive rules to reach authoritative servers on the internet.
Attackers can encode sensitive information like usernames and passwords within subdomain queries, while receiving encoded commands through various DNS record types including A, AAAA, TXT, CNAME, and MX records.
DNS Exploitation
Infoblox’s Threat Insight machine learning algorithms have been specifically developed to detect and block DNS tunneling domains within minutes of activation, often before handshakes complete and malicious activities begin.
Cobalt Strike, a popular penetration testing tool frequently abused by threat actors, accounts for 26% of detected tunneling activity and uses hex-encoded queries with customizable prefixes for beaconing and data exfiltration.
DNSCat2, included in the METASPLOIT framework, represents 13% of observed tunneling traffic and creates encrypted DNS tunnels using multiple query types.
Other notable tools include DNS Exfiltrator (15%), Sliver (12%), and Iodine (24%), each with unique signatures and communication patterns. These tools demonstrate varying levels of sophistication, from simple one-directional exfiltration to complex bidirectional command-and-control frameworks.
Advanced Detection Systems
Security researchers have identified several common DNS tunneling tool families being actively used in cyberattacks.
The system has evolved from detecting threats in one to two minutes to identification in less than five seconds, limiting potential queries to fewer than 10 and preventing even small-scale data exfiltration.
The detection improvements came after researchers identified highly unique signatures in queries and responses used by different tunneling families.
These signatures were incorporated into Threat Defense Recursive DNS Resolver systems, significantly enhancing machine learning algorithm performance.
Researchers also discovered instances of competitors’ DNS tunneling tools being used against their systems, including domains mimicking well-known security companies.
One notable case involved the domain “paioaltonetworks[.]tech,” which was detected and blocked within one minute of initial queries, demonstrating the effectiveness of real-time detection systems.
The combination of DNS exfiltration with lookalike domains has become an increasingly common tactic among malicious actors throughout 2024.
This evolution highlights the critical importance of implementing advanced DNS security measures, as traditional network defenses prove inadequate against these sophisticated tunneling techniques that exploit the inherent trust placed in DNS infrastructure.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




