Hundreds of TeslaMate installations are publicly accessible on the internet without authentication, exposing sensitive Tesla vehicle data including GPS coordinates, charging patterns, and driving habits.
The findings highlight critical security oversights in how Tesla owners deploy this popular open-source data logging tool.
TeslaMate is a self-hosted data logger designed for Tesla vehicles that connects to Tesla’s official API to collect detailed vehicle information.
The application, written in Elixir and utilizing Postgres databases with Grafana visualization, has gained popularity among Tesla enthusiasts for its comprehensive tracking capabilities.
However, the tool’s default configuration lacks built-in authentication mechanisms, creating significant privacy risks when deployed on public-facing servers.
The researcher employed sophisticated scanning techniques to identify vulnerable installations across the internet.
Using Masscan to sweep the entire IPv4 address space for open port 4000, where TeslaMate typically runs, the investigation uncovered numerous exposed instances.
The methodology involved probing identified hosts with httpx to confirm TeslaMate installations by detecting the application’s default HTTP title, followed by automated data collection from accessible endpoints.
The scanning operation utilized multiple 10Gbps servers to achieve rapid, large-scale discovery across global networks.
Beyond direct IP scanning, the researcher also leveraged CommonCrawl archives to identify TeslaMate installations running behind domain names, expanding the scope of discoverable vulnerable systems.
Extensive Data Exposure
The exposed data presents serious privacy and security implications for Tesla owners. Accessible information includes exact GPS coordinates of parked vehicles, Tesla model identifications with custom nicknames, software versions and update histories, and detailed timestamps of trips and charging sessions.

In many cases, researchers could map daily routines, identify home addresses, track commute patterns, and determine frequently visited locations.
The vulnerability extends beyond the core TeslaMate application. Many installations also expose Grafana dashboards on port 3000, often configured with default or weak credentials.
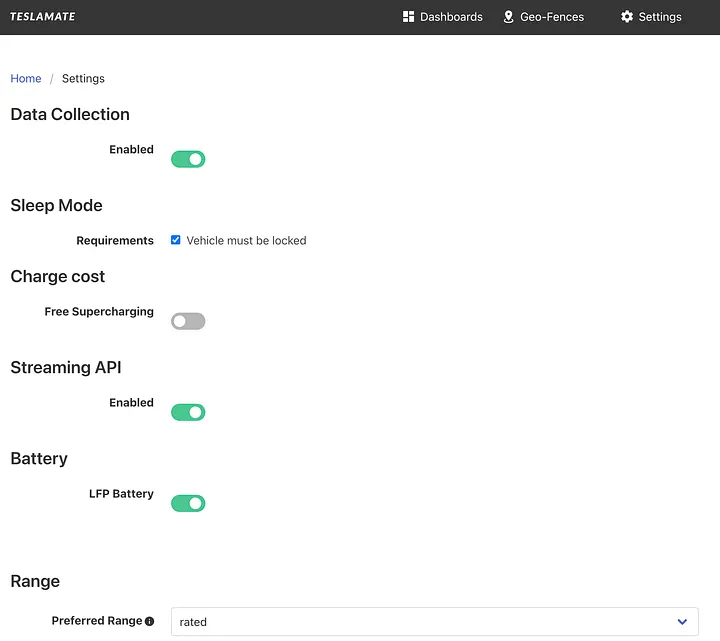
The TeslaMate settings page lacks access controls, potentially allowing unauthorized configuration changes.
This combination creates multiple attack vectors for malicious actors seeking to exploit vehicle location data or disrupt system operations.
Authentication and Security Measures
The security researcher addressed that while TeslaMate offers valuable functionality for Tesla enthusiasts, it was designed for personal use rather than internet-scale deployment.
The application’s feature set includes high-precision drive data recording, automatic address lookup, and integration with home automation systems via MQTT, making it attractive for technical users.
To address these vulnerabilities, security experts recommend implementing basic authentication mechanisms, such as username-password protection through reverse proxy configurations like Nginx.
Additional security measures include firewall restrictions limiting access to trusted IP addresses, binding services to localhost interfaces, and exposing applications only through VPN connections.
The discovery serves as a critical reminder that open-source tools require careful security configuration when deployed in public environments.
As connected vehicle technologies continue expanding, proper authentication and access control implementation becomes essential rather than optional for protecting sensitive automotive data from unauthorized access.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.
.webp?w=696&resize=696,0&ssl=1)
.webp?w=356&resize=356,220&ssl=1)




