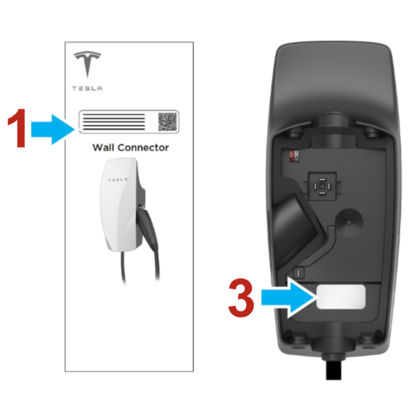
A critical vulnerability in Tesla’s Wall Connector home charging stations, proving that attackers can gain control of the devices through the charging port itself in just 18 minutes.
The attack, showcased at the Pwn2Own competition by cybersecurity firm Synacktiv, exploits a previously unknown communication protocol between Tesla vehicles and their charging infrastructure, potentially giving hackers access to home and business networks where these chargers are installed.
While analyzing Tesla vehicles for cybersecurity competitions, Synacktiv researchers uncovered an undocumented capability: Tesla cars can update Wall Connector firmware through the charging cable itself.
This discovery led them to investigate the charging infrastructure as a potential attack vector, even before Wall Connectors were officially included in hacking competitions.
The researchers found that Tesla’s charging process involves more than simple power delivery.
Beyond standard charging signals, they identified the use of Single-Wire CAN (Controller Area Network) protocol over the Control Pilot line – the same communication channel used for basic charging coordination.
This bidirectional communication channel, typically used for advanced features like Vehicle-to-Grid functionality, became the entry point for their sophisticated attack.
Firmware Vulnerability
The successful hack required building custom hardware to simulate a Tesla vehicle, including modified CAN adapters and relay-controlled circuits to mimic proper charging behavior.
Once the charger entered communication mode, the researchers exploited a critical vulnerability: the Wall Connector’s diagnostic services lacked proper security controls.
The attack involved downgrading the Wall Connector’s firmware from current versions to an older 2021 release (version 0.8.58) that contained debug features removed from newer versions.
This downgrade was possible because Tesla had not implemented anti-rollback protection at the time.
The older firmware exposed a TCP debug shell accessible through the charger’s setup Wi-Fi network, along with hardcoded authentication credentials that could be extracted using diagnostic commands.
With access to the debug interface, researchers discovered a buffer overflow Vulnerability in the command parsing system.
By sending specially crafted commands with more than 16 arguments, they could overwrite function pointers in memory, achieving arbitrary code execution on the device.
The firmware’s lack of memory protection made exploitation straightforward, allowing complete control over the charger’s operations.
Tesla Security Update
The implications extend beyond the charging device itself. Since Wall Connectors typically connect to home, hotel, or business Wi-Fi networks, successful exploitation could provide attackers with a foothold for lateral movement to other network-connected devices.
This scenario transforms a charging station into a potential gateway for broader network compromise.
Tesla has responded to the vulnerability disclosure by implementing anti-downgrade mechanisms that prevent the firmware rollback technique used in the attack.
However, the research highlights the expanding attack surface of connected vehicle infrastructure and the importance of securing communication protocols in electric vehicle charging systems.
The demonstration serves as a reminder that as vehicles become increasingly connected, every interface – including charging ports – represents a potential security risk requiring careful evaluation and protection.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




