Cybersecurity researchers have uncovered a sophisticated attack campaign targeting government agencies across Southeast Asia, featuring a previously undocumented Windows backdoor that exploits Amazon Web Services (AWS) Lambda URLs for command and control operations.
The threat, tracked as CL-STA-1020 by Unit 42 researchers, represents a novel approach to hiding malicious activities within legitimate cloud traffic.
Since late 2024, the attackers have been systematically collecting sensitive government information, including data related to recent trade disputes and tariff measures.
The campaign’s primary weapon is a newly discovered backdoor dubbed HazyBeacon, which leverages AWS Lambda URLs.
This feature allows direct invocation of serverless functions over HTTPS to establish covert communication channels.
Novel Cloud-Based Command and Control
The attackers deployed HazyBeacon through DLL sideloading, placing a malicious DLL file C:\Windows\assembly\mscorsvc.dll alongside the legitimate Windows executable mscorsvw.exe.
When the legitimate executable runs through its registered Windows service, it inadvertently loads the malicious replacement DLL instead of the authentic Microsoft library.
This technique provides several tactical advantages for threat actors. By utilizing AWS Lambda URLs, the malware can blend its command and control traffic with legitimate AWS communications, making detection significantly more challenging.
The serverless architecture allows attackers to operate a dynamic C2 server that receives beaconing requests from compromised systems while appearing as routine cloud service usage.
To maintain persistence, the attackers created a Windows service named “msdnetsvc,” ensuring the HazyBeacon DLL would reload even after system reboots.
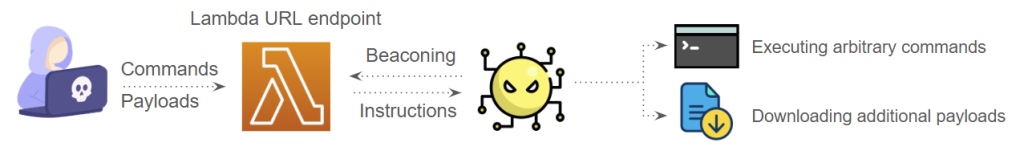
Once established, the backdoor communicated with an actor-controlled Lambda URL endpoint in the Asia-Pacific Southeast region.
Data Collection and Exfiltration Tactics
The campaign involved systematic data collection through a custom file collector tool (igfx.exe) that created ZIP archives containing targeted files based on specified time ranges and file extensions.
The attackers demonstrated particular interest in documents related to ongoing trade disputes, conducting searches for specific communications such as “letter to US President on Tariffs measures.”
For exfiltration, the threat actors employed multiple legitimate cloud services, including Google Drive and Dropbox, to blend their malicious activities with regular network traffic.
They used custom-built uploaders for both platforms, attempting to transfer collected data through these trusted services.
The 7-Zip utility was employed to split extensive archives into manageable 200 MB chunks for easier exfiltration.
This campaign highlights the evolving threat landscape where attackers increasingly exploit legitimate cloud services to evade traditional security measures.
Organizations should enhance monitoring of cloud resource usage and develop detection strategies capable of identifying suspicious communication patterns with trusted cloud services to better defend against such sophisticated attacks.
Indicators of Compromise
- SHA256 hashes for the Lambda-URL backdoor (C:\Windows\assembly\mscorsvc.dll)
- 4931df8650521cfd686782919bda0f376475f9fc5f1fee9d7cf3a4e0d9c73e30
- SHA256 hashes for the Google Drive file uploader (C:\ProgramData\google.exe)
- d20b536c88ecd326f79d7a9180f41a2e47a40fcf2cc6a2b02d68a081c89eaeaa
.jpg?w=696&resize=696,0&ssl=1)





