A critical vulnerabilities in Amazon Elastic Kubernetes Service (EKS) environments that allow attackers to exploit misconfigured containers to access sensitive AWS credentials and escalate privileges.
The findings highlight significant security risks in cloud-native applications where overprivileged containers can facilitate unauthorized access through packet sniffing and API spoofing techniques.
The research focuses on vulnerabilities within Amazon EKS Pod Identity, a feature designed to simplify the process of granting AWS credentials to pods running in EKS clusters.
This service operates as an alternative to IAM Roles for Service Accounts (IRSA), enabling secure access to AWS resources like S3 buckets and DynamoDB tables from Kubernetes applications.
The EKS Pod Identity agent functions as a DaemonSet in the kube-system namespace, running on each worker node and exposing an API on a link-local address (169.254.170.23 for IPv4) on port 80.
When applications make requests to AWS services, the SDK automatically retrieves temporary credentials from this agent, which then interacts with the eks-auth:AssumeRoleForPodIdentity API to obtain necessary credentials for associated IAM roles.
However, misconfigured containers with excessive privileges create significant security vulnerabilities.
The AWS shared responsibility model emphasizes that while service providers ensure infrastructure security, customers bear equal responsibility for managing privilege scoping within their containerized applications to maintain environmental security.
Amazon EKS Vulnerabilities
Trend Research identified two primary exploit scenarios that demonstrate how attackers can abuse overprivileged containers to extract sensitive AWS credentials.
The first attack vector involves packet sniffing-based exploitation. Since the EKS Pod Identity agent operates over unencrypted HTTP, any pod configured with ‘hostNetwork: true’ settings can monitor network traffic on the node.
This configuration enables attackers to intercept credentials transmitted from the API endpoint at 169.254.170.23:80.
Researchers demonstrated this vulnerability using a simple proof-of-concept with the tcpdump utility, showing that credentials are transmitted in plaintext and can be captured for malicious use.

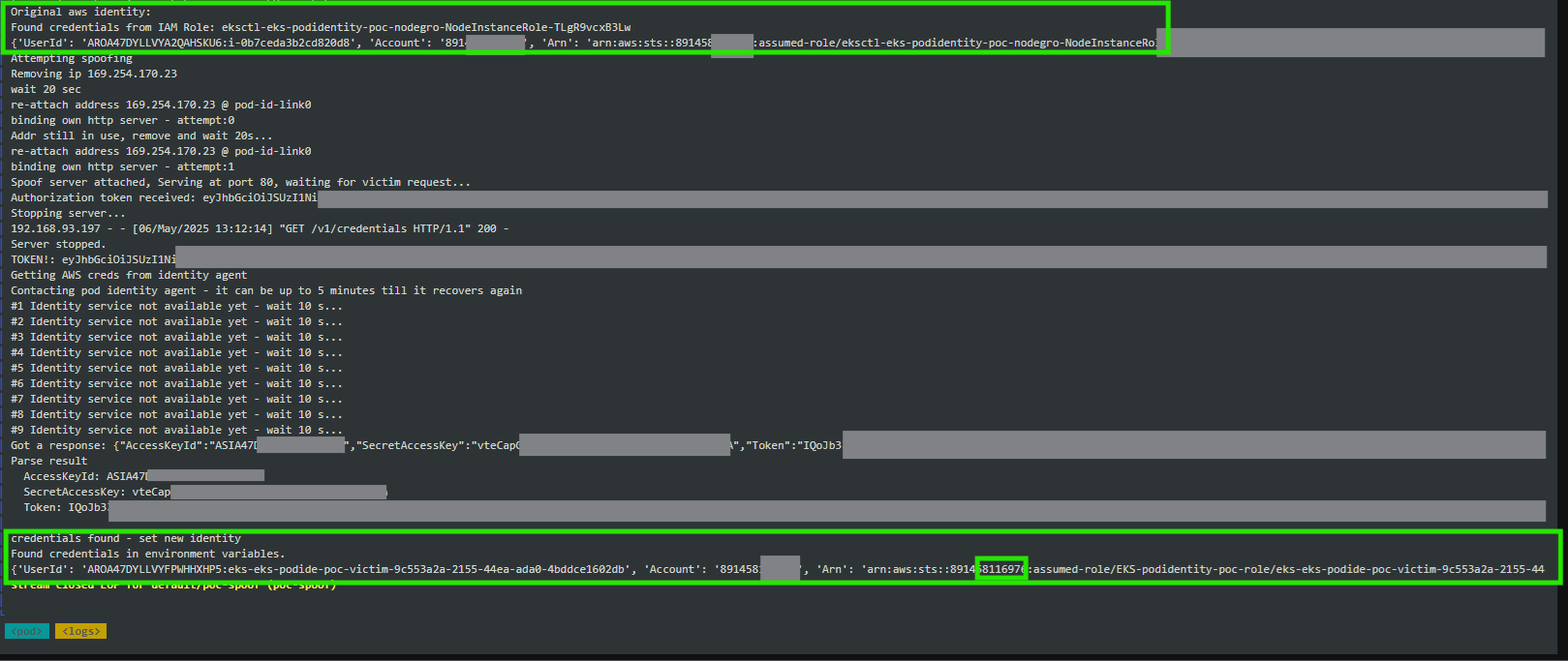
The second scenario involves API spoofing-based attacks. Even when containers have the CAP_NET_RAW capability removed, other privileges like CAP_NET_ADMIN still allow network interface manipulation.
Attackers can exploit these permissions to disable the legitimate eks-pod-identity-agent HTTP daemon by deleting the local link IP address.
This manipulation enables attackers to deploy their own HTTP server on the same endpoint, intercepting incoming HTTP requests containing Authorization tokens and subsequently obtaining valid AWS credentials.
Mitigations
The vulnerabilities underscore the critical importance of implementing proper container security measures and adhering to the principle of least privilege.
Organizations must ensure container configurations are appropriately scoped and minimize exploitation opportunities.
Trend Vision One Container Security offers proactive security policies that detect and mitigate containers operating beyond intended privilege levels.
This solution helps prevent both packet sniffing and API spoofing scenarios while reducing the overall attack surface and minimizing security risks.
Key recommendations include limiting container privileges to only necessary permissions, implementing proper configuration management, and deploying comprehensive monitoring solutions.
Organizations should also regularly audit their containerized environments to identify and remediate overprivileged containers before they can be exploited by malicious actors.
These findings highlight the evolving threat landscape in cloud-native environments and emphasize the need for robust security measures in Kubernetes deployments to protect sensitive AWS credentials and prevent privilege escalation attacks.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




