Singapore’s cybersecurity landscape faces an unprecedented threat from UNC3886, an advanced persistent threat (APT) group that has been systematically targeting critical infrastructure across telecommunications, government, technology, and defense sectors.
The sophisticated cyber espionage group demonstrates exceptional capabilities in rapidly exploiting zero-day vulnerabilities in enterprise network and virtualization platforms, deploying custom malware toolsets including TinyShell remote access tools and advanced Linux rootkits like Reptile and Medusa to maintain persistent, undetected access to compromised systems.
On July 18, Singapore’s Coordinating Minister for National Security K. Shanmugam publicly revealed that the nation was confronting a highly sophisticated cyber threat targeting its critical infrastructure systems.
UNC3886, first documented in 2022 but with evidence of activity dating back to late 2021, has established itself as a persistent adversary specifically focused on essential services within Singapore’s digital ecosystem.
The Cyber Security Agency (CSA) of Singapore has been actively investigating the group’s operations across multiple critical service sectors, though specific affected industries remain classified to preserve operational security.
The threat actor’s strategic targeting of Singapore represents a significant escalation in regional cyber warfare, with UNC3886 demonstrating an alarming ability to penetrate and maintain presence within systems that power the nation’s essential services.
The group’s activities have been detected across various components of Singapore’s critical information infrastructure, highlighting the severe national security implications of their operations.
Despite extensive monitoring efforts by Singaporean authorities, UNC3886’s advanced evasion techniques and persistent re-entry capabilities make complete remediation challenging.
Advanced Malware Arsenal
UNC3886’s technical sophistication is exemplified through their deployment of specialized malware designed specifically for Linux environments and enterprise infrastructure.
TinyShell, their lightweight Python-based remote access tool, provides encrypted HTTP/HTTPS communications that effectively evade network monitoring systems.
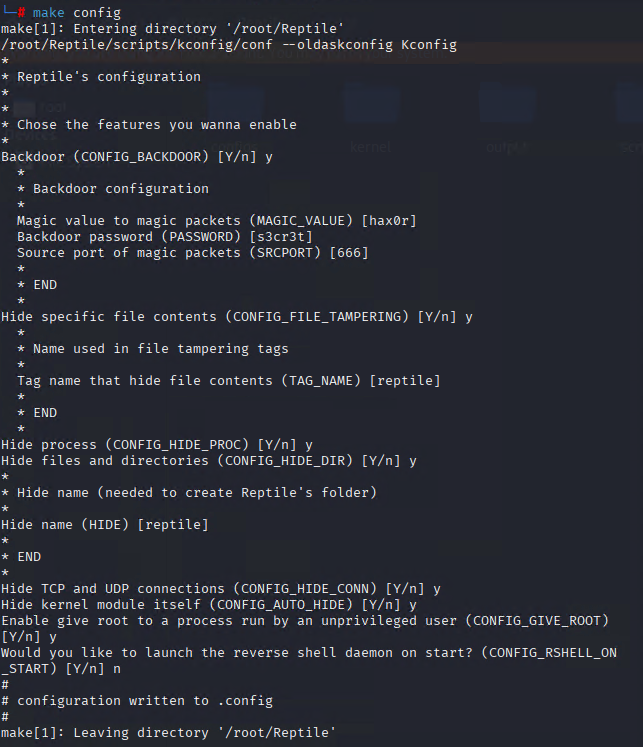
The group’s use of the Reptile Linux rootkit represents a particularly concerning capability, operating at the kernel level to hide files, processes, and network activity while providing attackers with persistent backdoor access.
The Medusa rootkit serves as another cornerstone of UNC3886’s persistence strategy, intercepting system calls and manipulating their output to cloak malicious activities from security tools and administrators.
UNC3886 has demonstrated particular expertise in targeting VMware environments, exploiting CVE-2023-34048 in vCenter Server to achieve unauthenticated remote command execution, often deploying backdoors within minutes of successful exploitation.
This kernel-level rootkit enables the group to maintain covert presence on compromised Linux servers for extended periods, facilitating ongoing espionage operations.
Additional tools in their arsenal include MopSled, a modular shellcode-based backdoor with plugin capabilities, and CastleTap, a passive backdoor specifically designed to target FortiGate firewalls by masquerading as legitimate system processes.
Organizations are strongly advised to apply vendor patches immediately and implement comprehensive monitoring for the specific indicators of compromise associated with UNC3886’s operations.
Zero-Day Vulnerability Exploitation
The group’s technical prowess is most evident in their systematic exploitation of high-impact vulnerabilities across widely deployed enterprise platforms.
Their attacks on Fortinet systems leverage CVE-2022-41328, a path traversal vulnerability in FortiOS that enables privileged attackers to read and write files on underlying Linux systems.
The threat group’s exploitation techniques extend to Juniper Networks infrastructure through CVE-2025-21590, which allows authenticated users with administrative privileges to insert malicious code leading to full system compromise.
These vulnerabilities collectively provide UNC3886 with multiple vectors for initial access, privilege escalation, and persistent control over critical network infrastructure.
UNC3886 represents a paradigm shift in advanced persistent threat capabilities, combining sophisticated technical skills with strategic targeting of critical infrastructure systems.
Their continued operations against Singapore underscore the evolving nature of state-sponsored cyber espionage and the urgent need for enhanced defensive measures across all critical sectors.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




