Cybersecurity researchers have released Zig Strike, a sophisticated offensive toolkit designed to test organizational defenses by bypassing modern security solutions including antivirus (AV), next-generation antivirus (NGAV), and Endpoint Detection and Response (XDR/EDR) systems.
The toolkit, developed over six months, represents a significant evolution in red teaming capabilities, transitioning from traditional programming languages to the modern Zig programming language for enhanced evasion techniques.
The release comes as cybersecurity threats continue to evolve, requiring constant innovation in defensive testing methodologies.
Zig Strike specifically targets advanced security solutions, with demonstrated success in bypassing Microsoft Defender for Endpoint (MDE), showcasing realistic attack scenarios from initial compromise to data exfiltration.
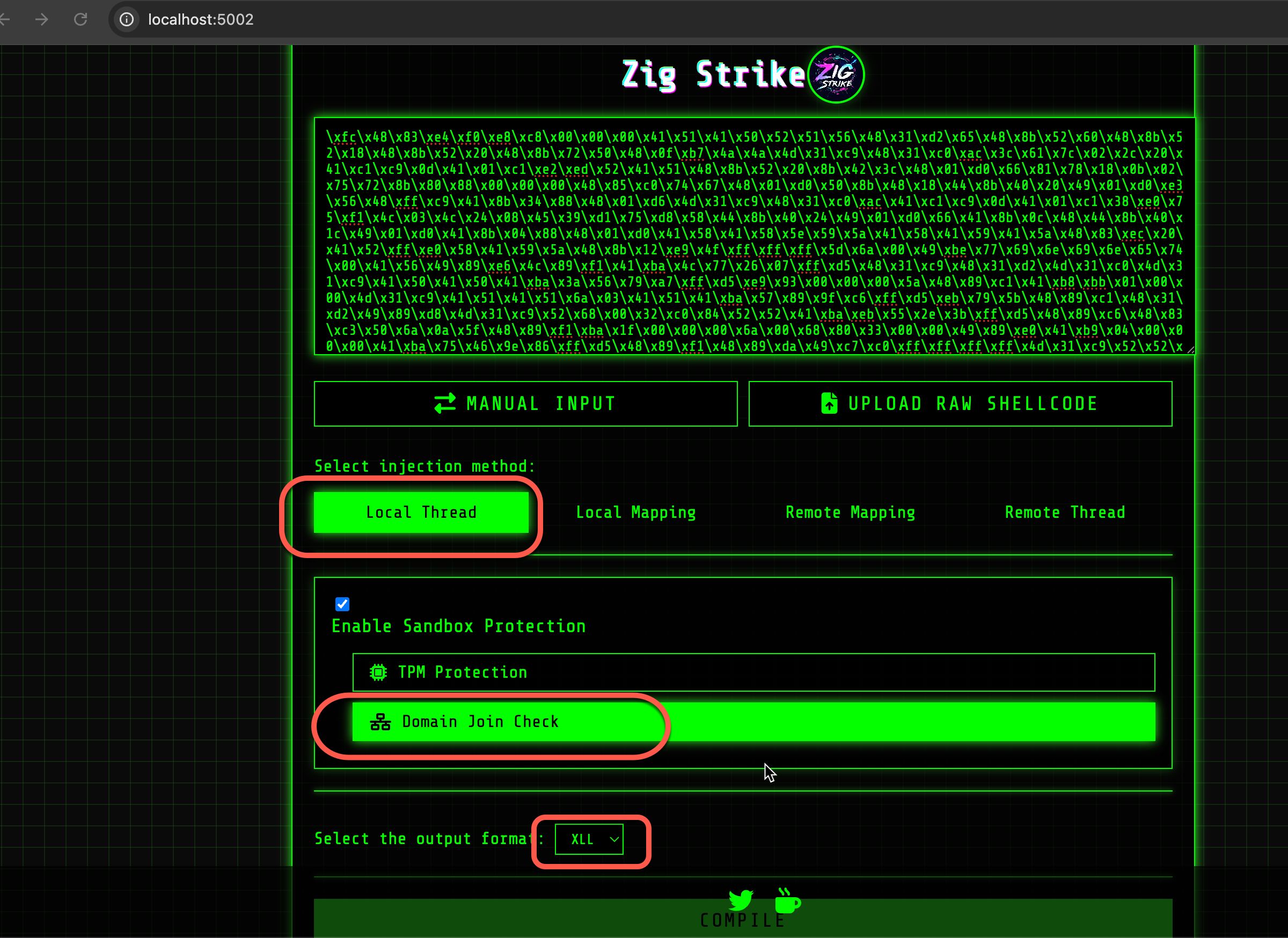
Zig Strike incorporates four distinct injection techniques tailored for different attack scenarios.
The toolkit features local thread injection, which hijacks created threads and redirects payload execution through dummy function callbacks, performing function stomping by loading specific Windows APIs and overwriting their function addresses.
Remote thread hijacking elevates the approach by targeting existing threads in remote processes, manipulating execution flow through direct thread context modification using GetThreadContext and SetThreadContext APIs to redirect the instruction pointer to shellcode.
The toolkit also implements local and remote mapping techniques that leverage Windows file mapping APIs, including CreateFileMappingW, MapViewOfFile, and MapViewOfFileNuma2, to allocate executable memory while reducing suspicious memory patterns typically flagged by EDR solutions.

The web-based interface allows security professionals to upload RAW or C-based shellcode, select specific injection methods, and customize options before the backend Zig compiler processes inputs and generates ready-to-test payloads.
Innovative Evasion Methods
The toolkit employs entropy reduction techniques using Zig’s comptime functionality to embed shellcode within Portable Executable files.
Shellcode is divided into smaller segments and declared as wide-string variables during compilation, storing them in the PE file’s .rdata section as ordinary static data.
By utilizing UTF16 wide strings instead of standard ANSI strings, the toolkit creates unusual representations that help evade detection, as antivirus engines are less likely to treat Base64-encoded UTF16 data as suspicious.
The system performs comptime operations on 15 shellcode segments by default, though this can be increased to further reduce static detection.
Anti-sandbox mechanisms prevent dynamic malware analysis through TPM (Trusted Platform Module) checks and domain-joined verification, as sandboxes typically operate in isolated environments without these characteristics.
Successful Bypass Demonstrations
According to Report, testing in realistic environments with Microsoft Defender for Endpoint and Attack Surface Reduction rules enabled demonstrated Zig Strike’s effectiveness.
The toolkit successfully generated Excel Add-in (XLL) payloads that bypass ASR rules by embedding shellcode within Excel add-ins, which load into Excel’s process space.
Practical demonstrations showed successful Cobalt Strike beacon reception after payload execution, confirming the toolkit’s ability to circumvent advanced endpoint protection.
The toolkit supports both DLL and XLL output formats, providing flexibility for different attack scenarios and deployment methods.
Future development plans include direct and indirect syscalls, additional injection techniques, and sleep obfuscation capabilities.
As an open-source project, Zig Strike serves as a call to action for organizations to enhance defensive technologies and avoid relying solely on single cybersecurity solutions.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




