A critical unauthenticated remote code execution vulnerability in Broadcom’s Symantec Endpoint Management Suite, tracked as CVE-2025-5333 with a CVSS score of 9.5.
The vulnerability affects versions 8.6.x, 8.7.x, and 8.8 of the enterprise management platform, potentially allowing attackers to execute arbitrary code on targeted systems without authentication.
Broadcom has issued mitigation guidance following coordinated disclosure, emphasizing firewall configuration changes to prevent exploitation.
The vulnerability stems from an exposed legacy .NET Remoting endpoint in the Symantec Altiris Inventory Rule Management (IRM) component, accessible at tcp://<host>:4011/IRM/HostedService.
LRQA researchers discovered this vulnerability during a Red Team assessment while performing reconnaissance on a compromised workstation running Symantec Endpoint Management.
Using PowerShell enumeration techniques, the researchers identified port 4011 bound to 0.0.0.0, indicating global network accessibility.
Subsequent analysis using DnSpy, a .NET debugger and assembly editor, revealed the application’s use of RemotingConfiguration.RegisterWellKnownServiceType, confirming legacy .NET Remoting implementation.

The core issue lies in the application’s configuration of BinaryServerFormatterSinkProvider with TypeFilterLevel set to Full, an inherently unsafe setup that enables unrestricted object deserialization. This configuration allows attackers to send crafted .
NET objects to the server, which are automatically deserialized and can lead to arbitrary method execution.
The vulnerability class builds upon research originally conducted by James Forshaw in 2014, demonstrating how legacy .NET Remoting can be exploited for unauthenticated remote code execution.
Exploitation and Proof of Concept
LRQA researchers successfully demonstrated unauthenticated remote code execution using James Forshaw’s ExploitRemotingService tool.
The proof of concept involved executing the command ExploitRemotingService.exe --uselease tcp://<target>:4011/IRM/HostedService ls C:\ against a test environment, which triggered remote method invocation and returned the contents of the target system’s C:\ directory.
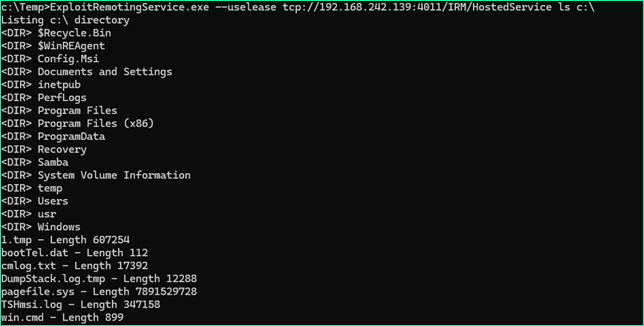
This demonstration confirms that the vulnerability allows complete system compromise without requiring authentication credentials or user interaction.
The attack vector operates over the network, making it particularly dangerous for organizations with exposed Symantec Endpoint Management infrastructure.
Mitigations
Broadcom’s response to the coordinated disclosure was swift and professional, with the vendor confirming the issue and providing immediate mitigation guidance.
The primary mitigation involves reviewing firewall settings on the Notification Server to ensure port 4011 remains closed, as official product documentation does not require this port to be opened.
For additional security, administrators can implement an optional configuration change through the Notification Server Console by adding a new Core Setting named IRM_HostedServiceUrl with an empty value, followed by restarting the “Altiris Inventory Rule Management Service.”
Broadcom has confirmed that future product releases and patches will limit and secure .NET Remoting for IRM/HostedService to localhost only, preventing remote connections entirely.
The vulnerability disclosure timeline began in May 2025 with the initial report to Broadcom PSIRT, followed by vendor confirmation, CVE assignment in June 2025, and coordinated public disclosure in July 2025.
Organizations using affected Symantec Endpoint Management Suite versions should immediately implement the recommended firewall configurations and monitor for any suspicious network activity targeting port 4011.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




