Cybercriminals are leveraging a sophisticated malware campaign dubbed Shadow Vector, which has been uncovered by the Acronis Threat Research Unit (TRU).
This operation targets users in Colombia by distributing what appear to be urgent court notifications via email.
The malicious emails carry SVG (Scalable Vector Graphics) file attachments a file format known for rendering cleanly in web browsers and often evading traditional email security filters.
SVG smuggling, a technique recently formalized under the MITRE ATT&CK framework, is central to the operation.
The phishing emails mimic correspondence from Colombia’s labor court, using urgency and official branding to pressure victims into interacting with the attachment.
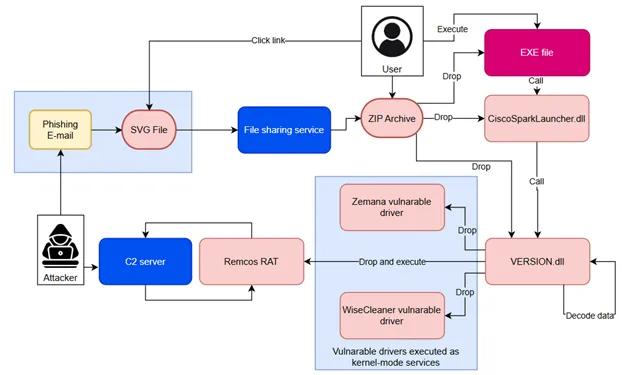
The SVG files contain embedded links leading to password-protected ZIP archives hosted on public file-sharing platforms, including Bitbucket, Dropbox, Discord CDN, and YDRAY.
This method enables attackers to blend malicious payloads with legitimate traffic, thereby bypassing basic detection systems.
Once victims open the SVG and download the ZIP, they are prompted to extract an executable and several DLLs, one of which is malicious and exploits DLL side-loading to inject malware.
The infection chain typically delivers AsyncRAT and RemcosRAT, both notorious remote access trojans (RATs) favored for data theft.
The legitimate-looking executable (often named something like vcredist.exe) loads a malicious DLL, which starts the infection.
Attackers manipulate file structures by inserting extra bytes at the PE header to disrupt automated analysis and evade detection.
The payload creates a suspended legitimate process and performs process hollowing, using functions like NtAllocateVirtualMemory, Wow64SetThreadContext, and NtResumeThread to inject and execute malicious code under the guise of a trusted process.
Advanced Evasion and Data Exfiltration
Shadow Vector utilizes multiple evasion tactics. During execution, it checks the environment for indicators of analysis such as virtual machines, debuggers, and sandbox environments and terminates if such indicators are detected.
The malware configuration, often encrypted using AES and embedded within the payload, contains command-and-control (C2) server details, installation flags, and other runtime settings, all of which are decrypted at execution.
The payload establishes persistence by copying itself to a new location and creating scheduled tasks or registry keys to auto-start on login, sometimes using string reversal techniques for added obfuscation.
Malicious behaviors include keylogging, capturing screenshots, and scanning for cryptocurrency wallets and browser extensions across multiple browsers.
Once connected to the C2 server, the malware transmits sensitive data, including hardware IDs, usernames, OS details, and wallet presence.
In later variants, the Shadow Vector campaign has expanded its tactics, deploying modular loaders and using PowerShell and JavaScript stagers for in-memory execution, which reduces disk artifacts and makes detection and analysis even more challenging.
Some loader samples feature Portuguese-language strings, suggesting possible code reuse or collaboration with Brazilian-based cybercriminals.
Mitigation and Response
The Colombian judiciary has issued advisories warning users about these attacks and urging caution when handling emails that prompt document downloads.
To protect against such threats, organizations should implement robust email filtering, educate users about the risks of opening attachments from unknown sources, and utilize advanced endpoint detection and response (EDR) solutions that can detect process hollowing and in-memory attacks.
Indicators of compromise
SVG
64e971f0fed4da9d71cd742db56f73b6f7da8fec3b8aebd17306e8e0d4f1d29d
4d292a785ec35530bac5f4674a97c0dffa2a2396bd8b0cc6f8b478ba13d73611
d713793b0b6dd1fe7c2432a28069745bc4bf97c098f1217de0731c7ed7c1d70a
1920d23a395aa729cc7658b8471939ef871108a94e93456793d1322dcbe9750b
fab0b6945c1ee0057349254760469b7d5a502819517b31049efc51a71b25c46d
52d2b4ac1a84449c72226e1deed8d33ebbe8fd00d4853e026adef679d7fa273d
f9b6c8f6f6a2f69286b298dd6375ebc25a07eb2012e226af1dfafd861b9edb3e
e50f96eb8fd7ca90df3db47368b413ffb875d5cd3685b9d601bb884ebe980ef9
.webp?w=696&resize=696,0&ssl=1)





