A sophisticated new SS7 bypass attack that enables surveillance companies to circumvent mobile network security defenses and illegally track user locations.
The attack exploits a little-known encoding technique in the SS7 protocol’s TCAP layer, effectively hiding subscriber identity information from security systems designed to block unauthorized location tracking requests.
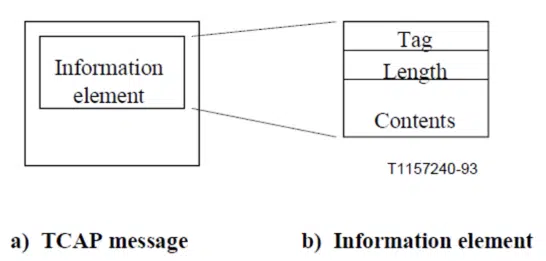
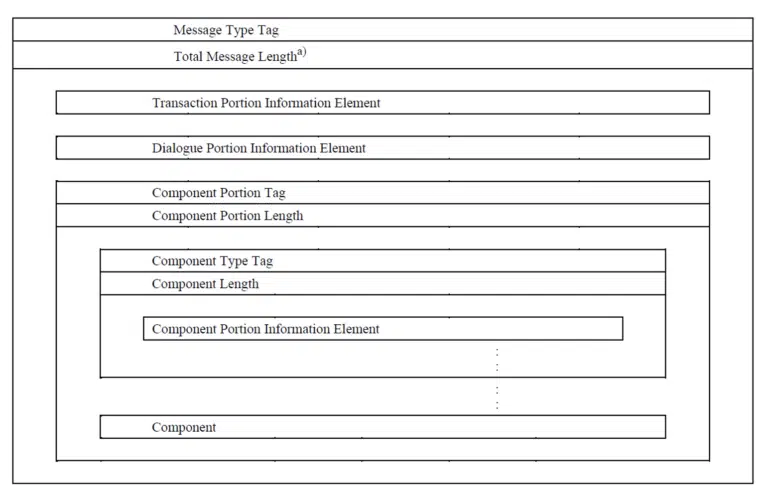
The attack targets the Transaction Capabilities Application Part (TCAP) layer of the SS7 protocol stack, which carries application data between network nodes using ASN.1 Basic Encoding Rules (BER).
Attackers manipulate the encoding of Information Elements containing International Mobile Subscriber Identity (IMSI) fields within ProvideSubscriberInfo (PSI) commands – legitimate network operations used for location tracking.
The technique involves extending TCAP tag codes using a rarely-implemented specification feature.
While normal IMSI fields use a standard tag code structure (30 12 80 08), attackers employ an extended tag sequence (30 13 9f 00 08) that adds an additional octet to the message.
This extension mechanism, defined in ITU Q.773 specifications for tag codes exceeding 30 decimal, has remained largely unused in over 40 years of SS7 operations.
The attack succeeds because many SS7 software stacks lack implementation logic for extended TCAP codes, having never encountered this encoding method in normal network operations.
When security systems cannot decode the extended tag structure, they fail to extract the IMSI information needed to determine whether the location request should be blocked.
Surveillance Firm Exploits SS7 Vulnerabilities
Enea’s Threat Intelligence Unit detected the attack being actively used by a surveillance company they have monitored for several years.
Analysis reveals the technique has been deployed since at least Q4 2024 as part of a broader attack suite designed to bypass signaling security defenses across targeted mobile operators.
The attack specifically targets PSI commands sent from external sources requesting location information about home network subscribers.
Mobile operators typically block such requests by checking if the source is external while the IMSI belongs to their home network.
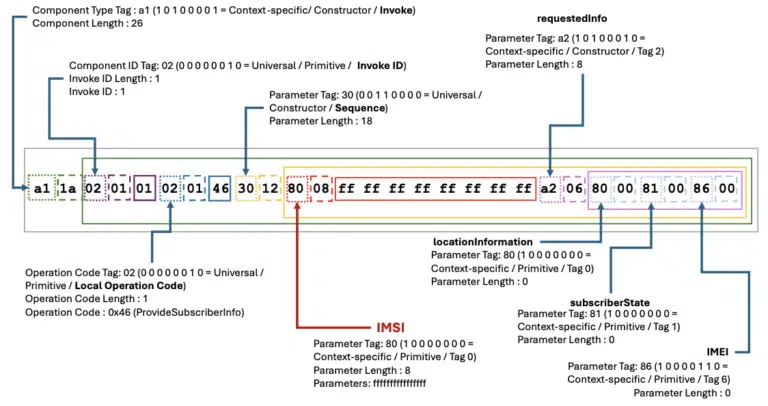
However, the extended tag encoding effectively “hides” the IMSI from security checks, allowing unauthorized location tracking to proceed.
Researchers confirmed successful attacks where PSI responses containing subscriber location data were transmitted back to the surveillance company, demonstrating the technique’s effectiveness against vulnerable network infrastructures.
The attack’s success varies depending on specific vendor implementations and software configurations rather than representing a universal protocol vulnerability.
Mitigations
Following the discovery, Enea collaborated with signaling security customers to implement protective measures and disclosed attack details to the GSMA community.
The company recommends blocking all malformed PDU structures not known to be benign, or blocking MAP PDUs where IMSI fields are expected but cannot be decoded from the PDU structure.
This attack represents the latest evolution in SS7 bypass techniques, joining previous methods including global opcode manipulation, extended application contexts, and missing CdPA SSNs that have emerged since 2017.
The TCAP layer’s combination of protocol complexity and encoding flexibility continues to provide opportunities for sophisticated attackers seeking to evade network security measures.
Security experts expect further attack evolution, particularly targeting the TCAP layer where ASN.1 protocol flexibility enables message disguise and evasion techniques across various signaling protocols beyond SS7.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




