Since early 2025, cybersecurity professionals have observed a sharp rise in malware campaigns leveraging the very security mechanisms designed to protect users: digitally signed executable files.
At the center of this disturbing trend is ConnectWise, a widely trusted remote access tool, now being weaponized by threat actors through the abuse of legitimate software features and signing practices.
Dubbed “EvilConwi” by researchers, this wave of attacks highlights a dangerous intersection of bad security practices and clever cybercriminal innovation.
Attack Methodology and Technical Details
Attackers capitalize on “Authenticode stuffing” a technique that allows manipulation of a binary’s attributes, such as the Windows Authenticode signature, without breaking the file’s digital signature.
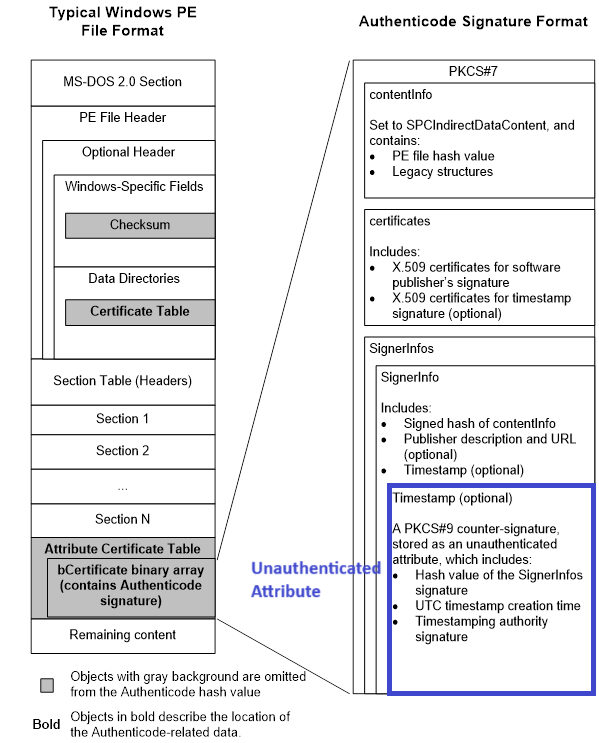
In ConnectWise’s case, unauthenticated attributes within the certificate table serve as a vector for malware customization, enabling remote connection parameters, icons, and even fake messages to be embedded and executed without detection by most antivirus products.
By modifying critical settings in configuration files like app.config and system.config—both XML-based and typically stored within or alongside the application—attackers can hide indicators of their presence, disable warning messages, and fake legitimate software branding (such as Google Chrome or a Windows Update dialog).
Binary analysis, conducted using tools like PortexAnalyzer and Meld, reveals that while the main executable sections remain unchanged, critical parts of the certificate table differ between benign and malicious samples.
Threat actors use scripts often shared or sold within underground forums to extract and manipulate these settings before redistributing the tainted executable.
One analyzed sample, for example, embedded a fake Windows Update image and Chrome icon, instructing users not to shut down their systems while remote attackers assumed control.
Detection and Vendor Response
Despite the ingenuity behind these attacks, security vendors have been slow to respond. As of May 2025, many leading antivirus solutions failed to flag suspiciously configured ConnectWise executables as malicious.
This detection gap is partly due to the abuse of signed, trusted certificates and the subtle nature of configuration-based malware—settings like ShowSystemTrayIcon, ShowBalloonOnConnect, and HideWallpaperOnConnect set to “false” are red flags but are often overlooked during routine scans.
To counter this threat, researchers recommend monitoring for suspicious configuration values and applying Yara rules such as:
textrule SilentConwi : Riskware PUP
{
meta:
author = "Karsten Hahn @ G DATA CyberDefense"
description = "Settings from app.config that hide the connection of the client. These settings are potentially unwanted"
strings:
$rex_01 = /<setting name="(Access|Support)?ShowBalloonOnConnect"[^>]*>\s*<value>false<\/value>/
$rex_02 = /<setting name="(Access|Support)?HideWallpaperOnConnect"[^>]*>\s*<value>false<\/value>/
$rex_03 = /<setting name="(Access|Support)?ShowBalloonOnHide"[^>]*>\s*<value>false<\/value>/
$rex_04 = /<setting name="(Access|Support)?ShowSystemTrayIcon"[^>]*>\s*<value>false<\/value>/
condition:
all of them
}
Looking Ahead: Remediation and Industry Impact
ConnectWise acknowledged the issue by revoking the abused signing certificate in mid-June 2025.
However, the underlying problem of configuration abuse via Authenticode stuffing remains unresolved and will require ongoing vigilance from both software vendors and security teams.
This incident serves as a cautionary tale that even trusted, signed software is not immune to exploitation when poor security practices persist.
Organizations are advised to carefully review any ConnectWise-based remote access requests, particularly those with suspicious branding, unexpected update prompts, or missing system tray icons.
As threat actors continue to evolve, the need for robust security practices, both in code signing and configuration management, has never been greater.
Until such improvements are made, the risk of signed malware masquerading as legitimate software remains a persistent threat to organizations worldwide.






