A serious remote code execution vulnerability has been discovered in Microsoft SharePoint that allows attackers to execute arbitrary code through malicious XML payloads embedded within Web Part components.
The vulnerability, which affects SharePoint version 15.0.5145.1000 and potentially others, exploits the deserialization process of WebPart properties to bypass security controls and achieve code execution.
While the specific CVE identifier remains unknown and the vulnerability has reportedly been patched, security researchers have demonstrated how the vulnerability can be weaponized using carefully crafted XML content that triggers unsafe deserialization operations within SharePoint’s Web Part infrastructure.
The vulnerability originates in SharePoint’s Web Part control parsing process, specifically within the Microsoft.SharePoint.WebPartPages.WebPart.AddParsedSubObject() method.
When a Web Part contains HTML content or strings as LiteralControl elements, SharePoint automatically processes this content through its XML parsing mechanism.
The attack begins when an attacker embeds malicious content within a Web Part control structure, such as <WebPartPages:XmlWebPart ID="SPWebPartManager" runat="Server"><sometag>some content</sometag></WebPartPages:XmlWebPart>.
The parsing process follows a specific execution path through multiple SharePoint components, ultimately leading to the Microsoft.SharePoint.WebPartPages.Utility.DeserializeStringToObject() method.
This method utilizes SharePoint’s SPObjectStateFormatter, a customized version of the standard ObjectStateFormatter that employs BinaryFormatter for deserialization operations.

The critical vulnerability lies in the SPSerializationBinder component, which is designed to restrict deserialization to safe types but contains a significant security gap.
SharePoint RCE Vulnerability
The SPSerializationBinder.IsAllowedType() method contains the core vulnerability by permitting binary deserialization of any class listed in SharePoint’s SafeControls configuration.
This design vulnerability allows attackers to exploit legitimate SharePoint classes that were never intended for deserialization attacks.
Security researchers identified Microsoft.SharePoint.ApplicationPages.SPThemes as a particularly exploitable class within the SafeControls whitelist.
The SPThemes class inherits from DataSet and implements a serialization constructor, making it suitable for deserialization attacks.
Attackers can leverage existing tools like ysoserial.net, modifying the DataSetMarshal payload to target Microsoft.SharePoint.ApplicationPages.SPThemes instead of the standard DataSet class.
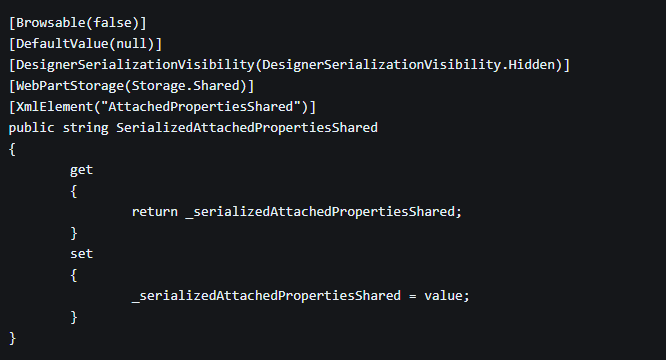
The malicious payload is embedded within the AttachedPropertiesShared XML element, which SharePoint automatically processes during Web Part deserialization.
Security Implications
While Microsoft has reportedly addressed this vulnerability in newer versions, organizations running affected SharePoint installations should prioritize updates and implement additional security monitoring for Web Part-related activities.
The vulnerability can be exploited through multiple attack vectors, including direct Web Part manipulation on SharePoint pages or through SharePoint’s Web Part Pages web service.
The most concerning aspect is that the attack can be delivered via a simple HTTP POST request to the /_vti_bin/webpartpages.asmx endpoint using the ConvertWebPartFormat SOAP action.
This allows remote attackers to execute arbitrary code without requiring authenticated access to SharePoint’s administrative interface.
The attack payload consists of a base64-encoded serialized object embedded within the AttachedPropertiesShared element of a Web Part XML structure.
When SharePoint processes this XML content, it automatically deserializes the malicious payload, leading to code execution within the context of the SharePoint application.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




