A previously obscure ransomware group has rapidly emerged as one of the most dangerous threats on the global cybersecurity landscape in Q1 2025.
SafePay ransomware has quietly built momentum, striking over 200 victims worldwide, including managed service providers (MSPs) and small to mid-sized businesses (SMBs) across various industries.
The group’s sophisticated approach and centralized operations have set it apart from traditional ransomware-as-a-service (RaaS) models, making it a significant concern for cybersecurity professionals.
Unlike many ransomware groups that rely on affiliate networks, SafePay appears to operate with centralized control, managing its own operations, infrastructure, and negotiations.
The group’s most high-profile attack recently disrupted Ingram Micro, a global distributor serving thousands of partners and MSPs, demonstrating the far-reaching impact of their operations.
Technical Arsenal and LockBit Connection
Analysis by the Acronis Threat Research Unit (TRU) reveals that SafePay shares striking similarities with the LockBit ransomware family, suggesting it may be a sophisticated spinoff utilizing leaked LockBit 3.0 builder source code from 2022.
The SafePay sample analyzed is a PE32 DLL file with multiple characteristics that mirror LockBit’s architecture, including the requirement for a password for complete execution, encoded strings, and runtime WinAPI address resolution.
The malware employs a complex string decryption routine using triple XOR operations with different keys, including the current index value, the first symbol from ‘kernel32.dll’ (always ‘M’), and a constant value unique to each encrypted string.
This sophisticated obfuscation technique makes detection significantly more challenging before execution.
SafePay demonstrates advanced evasion capabilities by checking system language IDs to avoid execution in specific regions, including those using Russian, Ukrainian, Belarusian, Tajik, Armenian, Azerbaijani, and Georgian languages.
The malware also creates threads with the ‘ThreadHideFromDebugger’ flag to prevent analysis and abuses the CMSTPLUA COM interface for privilege escalation.
Attack Methodology and Double Extortion
The group’s attack methodology combines classic but highly effective techniques. SafePay operators gain initial access through RDP and VPN-based intrusions, followed by credential theft and privilege escalation.
They utilize living-off-the-land binaries to move laterally through victim networks while maintaining stealth.
Before encryption, attackers execute reconnaissance using the ‘ShareFinder.ps1’ script to identify network shares, then employ WinRAR for file compression and FileZilla for data exfiltration to command-and-control servers.
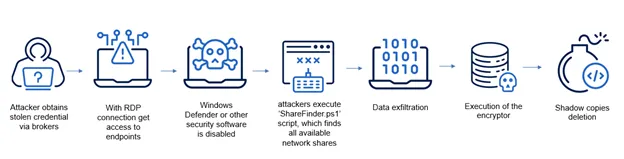
The malware systematically terminates critical processes and services, including database applications, backup services, and security solutions like Sophos and Veeam.
SafePay employs double extortion tactics, first exfiltrating sensitive data before encrypting files using a robust combination of AES and RSA encryption algorithms.
The malware generates 32 random bytes for each file as an AES key, which is then encrypted using RSA, ensuring strong cryptographic protection that makes unauthorized decryption virtually impossible.
.jpg?w=696&resize=696,0&ssl=1)





