The release of RIFT (Rust Identification and Function Tagging), an open-source tool designed to help malware analysts identify attacker-written code within Rust binaries.
The tool addresses growing cybersecurity challenges as threat actors increasingly adopt Rust programming language for malware development, taking advantage of its efficiency, type safety, and memory safety features to create more sophisticated and harder-to-analyze malicious software.
The announcement comes as cybersecurity professionals face mounting difficulties in reverse engineering Rust-based malware, which has become significantly more complex than traditional malware written in languages like C++.
Microsoft’s research demonstrates this complexity through a simple comparison: while a basic downloader program compiled in C++ contains fewer than 100 functions and occupies less than 20 KB, the same program compiled in Rust packs almost 10,000 functions and exceeds 3 MB in size.
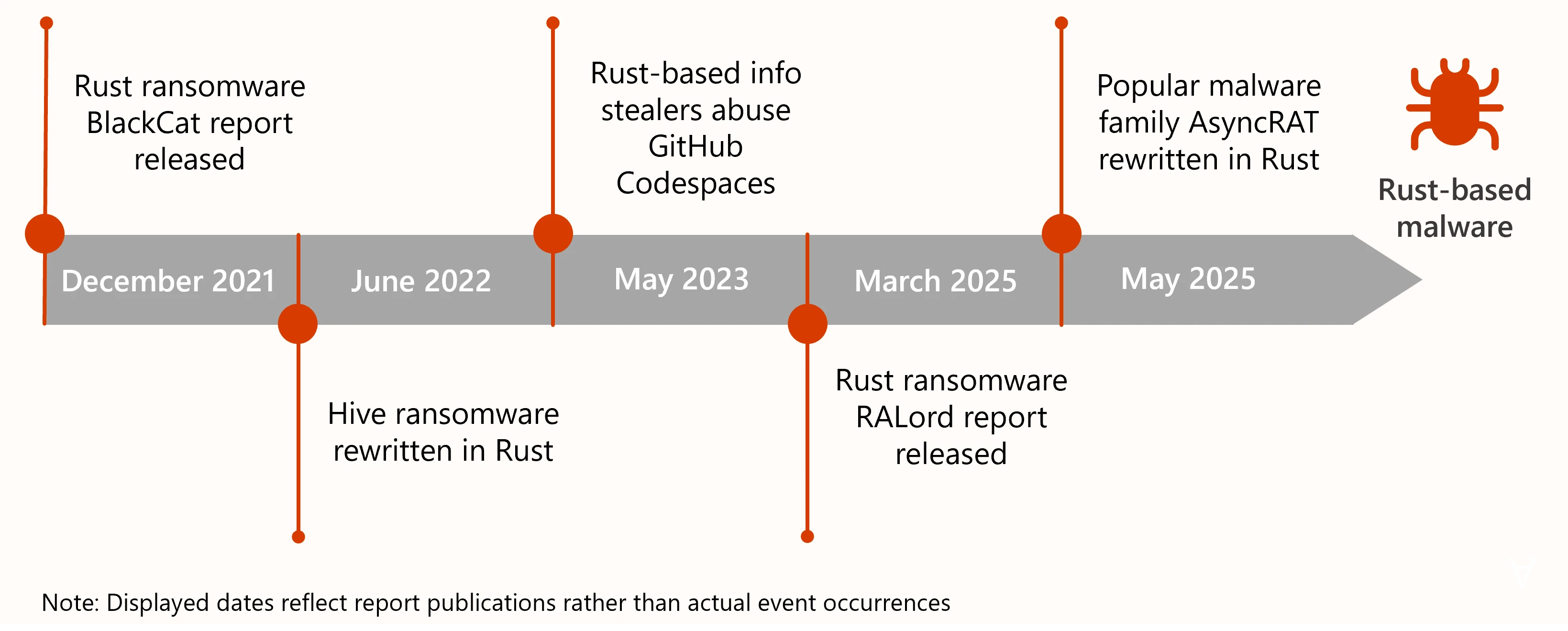
Over the past five years, Microsoft has observed a concerning trend of financially motivated groups and nation-state entities increasingly adopting Rust for malware development.
The timeline of this adoption began in December 2021 with the notorious BlackCat ransomware, followed by the Hive ransomware being rewritten in Rust in June 2022.
The trend accelerated in 2023 with Rust-based information stealers abusing GitHub Codespace, and continued into 2025 with reports of RALord ransomware and the popular AsyncRAT malware family being rewritten in Rust.
This shift presents unique challenges for cybersecurity professionals. Rust’s layers of abstraction, added through features like memory safety and concurrency handling, make it significantly more difficult to identify malicious behavior and intent.
The primary obstacle lies in distinguishing between attacker-written code and standard library code within the complex, statically-linked Rust binaries that embed all dependencies directly into the executable.
RIFT Transforms Malware Analysis
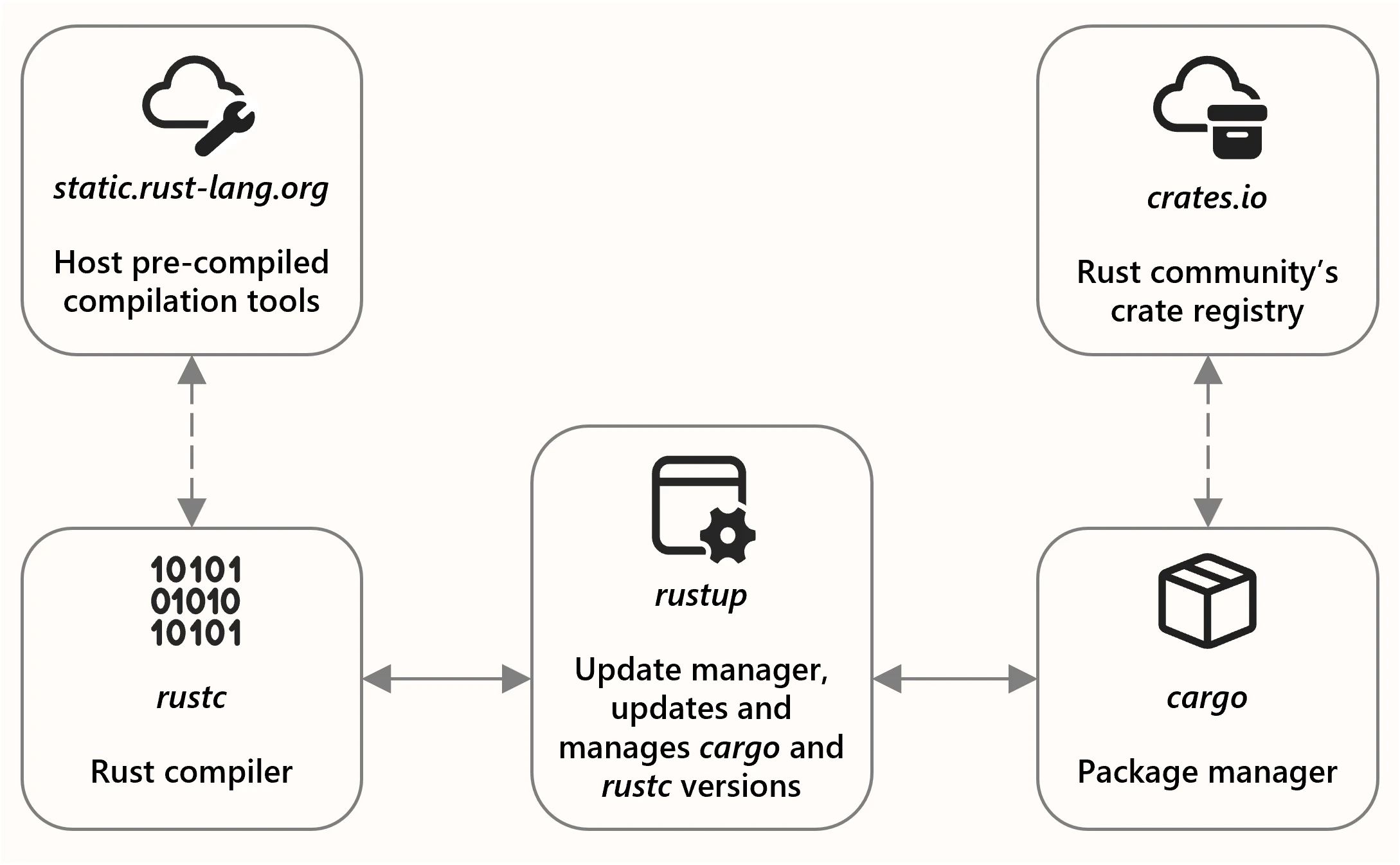
RIFT consists of three integrated components designed to streamline the analysis process.
The RIFT Static Analyzer serves as an IDA Pro plugin (supporting versions 9.0 and above) that extracts Rust compiler commit hashes and embedded dependencies from binarie.
The RIFT Generator functions as a Python program that automates Rust compiler identification, FLIRT signature generation, and binary diffing processes.
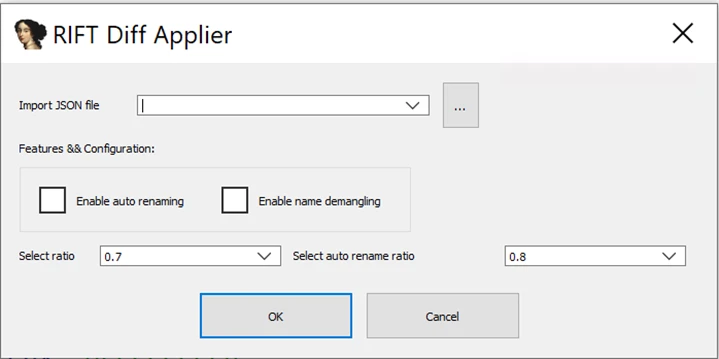
Finally, the RIFT Diff Applier operates as an IDA Pro plugin that applies binary diffing information generated by the RIFT Generator.
The tool employs two sophisticated pattern-matching techniques: FLIRT (Fast Library Identification and Recognition Technology) signatures and binary diffing.
FLIRT signatures provide highly reliable annotation with low false positive rates, enabling rapid identification of standard library functions.
The binary diffing approach offers broader coverage with higher sensitivity, filling gaps where FLIRT signatures may fail due to their strict criteria.
RIFT automates several critical processes, including compilation management through Cargo (Rust package manager), FLIRT signature generation using Hexray’s FLAIR tools, and binary analysis through Hexray’s text interface version of IDA.
The tool also leverages the open-source Diaphora project for automated binary diffing capabilities.
Real-World Impact
Microsoft has successfully demonstrated RIFT’s effectiveness against real-world threats, including RALord ransomware and SPICA backdoor.
In practical applications, RIFT dramatically reduces analysis time by automatically identifying and annotating library code, allowing reverse engineers to focus exclusively on threat actor-authored logic rather than spending valuable time distinguishing between malicious code and standard library functions.
The tool’s binary diffing approach proves particularly valuable for deep-dive analyses where FLIRT signatures alone may be insufficient.
This complementary analysis method provides additional information to improve library code recognition and can assist in detection engineering by helping identify or filter out potential library functions when writing signatures for code segments.
By open-sourcing RIFT, Microsoft aims to foster collaboration and innovation within the cybersecurity community to combat the rising threat of Rust-based malware.
The initiative represents a significant step forward in equipping security professionals with specialized tools necessary to defend against increasingly sophisticated cyber threats that leverage modern programming languages to evade detection and complicate analysis efforts.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.
.webp?w=356&resize=356,220&ssl=1)




