A sophisticated phishing campaign has been detected leveraging the domain ypp-studio[.]com to deliver the notorious Rhadamanthys infostealer, marking a new escalation in phishing and malware delivery tactics.
Using advanced evasion methods and a novel ClickFix CAPTCHA delivery mechanism, this campaign poses a significant risk to individuals and organizations worldwide.
Fileless Delivery: From Phishing Domain to Infostealer
Investigators traced suspicious PowerShell activity leading back to hxxps://ypp-studio[.]com/update.txt, a resource containing obfuscated and hex-encoded scripts. These scripts, when executed, leverage the following PowerShell enhancements:
- Window hiding (
-w hidden), - Execution policy bypasses (
-ep bypass), - Profile skipping (
-nop),
enabling a stealthy, fileless attack chain. The script defines a remote URL for malware retrieval, decodes the payload, and ultimately invokes the malicious file with:msiexec.exe /i %AppData%\PTRFHDGS.msi.
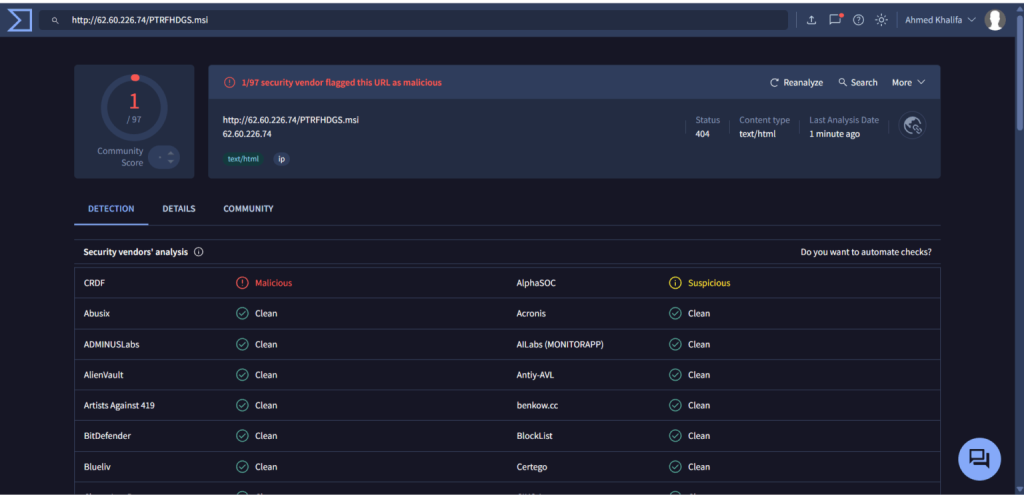
Upon visiting a related IP (hxxp://62.60.226.74/PTRFHDGS.msi), an automatic download of rh_0.9.0.exe is triggered. This executable closely matches previously documented Rhadamanthys Stealer samples.
Recent updates reveal a shift from older delivery servers to this new infrastructure, reinforcing the ongoing development and distribution of Rhadamanthys as Malware-as-a-Service (MaaS).
Advanced Evasion and Data Exfiltration
Rhadamanthys is renowned for its anti-analysis capabilities. The malware employs multiple checks to detect sandbox environments, virtual machines, and debugging tools by cross-referencing active process lists with known analysis tools such as x64dbg.exe, ProcessHacker.exe, Wireshark.exe, and others.
It uses time-based side-channel attacks, process blacklists, and direct Winsock API calls to evade network-based detection.
Once active, the infostealer’s reach is extensive. It systematically harvests:
- Credentials, cookies, and autofill data from web browsers,
- Cryptocurrency wallet files,
- Messaging app accounts (Telegram, Discord, etc.),
- Files from FTP, VPN, and email clients,
- Screenshots of user activity,
- Password manager vaults (e.g., KeePass).
Network exfiltration is executed over direct TCP sockets to hardcoded command-and-control IPs (such as 193.109.85.136), further bypassing DNS monitoring.
Evolving Social Engineering: ClickFix Captcha as Attack Vector
The use of ClickFix CAPTCHA gateways in this campaign demonstrates an evolution in social engineering.
By requiring users to “verify” themselves, attackers disguise malicious downloads as legitimate interactions, thereby bypassing security controls and luring victims into executing sophisticated fileless malware.
This campaign highlights the adaptability of Rhadamanthys operators, combining advanced delivery infrastructure, anti-analysis, and social engineering.
Organizations should bolster endpoint monitoring and educate users about phishing and suspicious PowerShell activities. Sigma detection rules targeting the infostealer’s unique behaviors are recommended for early detection and rapid response.
.jpg?w=696&resize=696,0&ssl=1)





