A sophisticated exploitation of the Retbleed vulnerability, showcasing how attackers can read arbitrary physical memory from sandboxed processes and virtual machines at unprecedented speeds.
This development represents a significant escalation in the real-world impact of speculative execution vulnerabilities affecting modern AMD and Intel processors.
This represents roughly a 3x performance improvement over previous implementations, making the attack practically viable for extracting sensitive information including cryptographic keys, process lists, and virtual machine data from host systems.
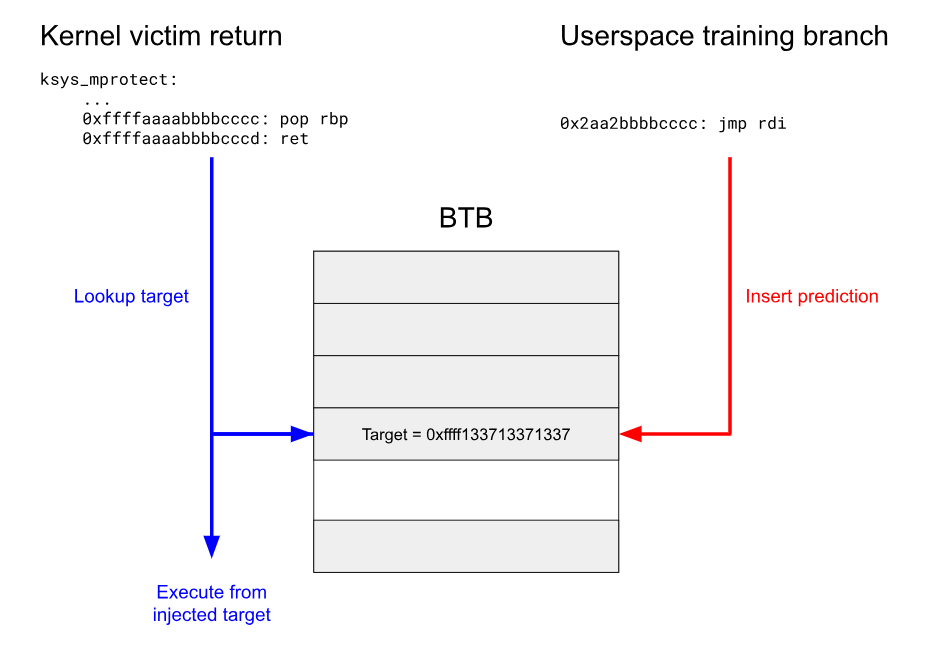
The enhanced exploit works by manipulating CPU speculative execution through return instruction hijacking, forcing processors to execute disclosure gadgets that encode secret data into cache channels.
Unlike the original proof-of-concept, this implementation operates effectively within restrictive sandbox environments, requiring access to only three common system calls: mmap, mprotect, and sched_yield.
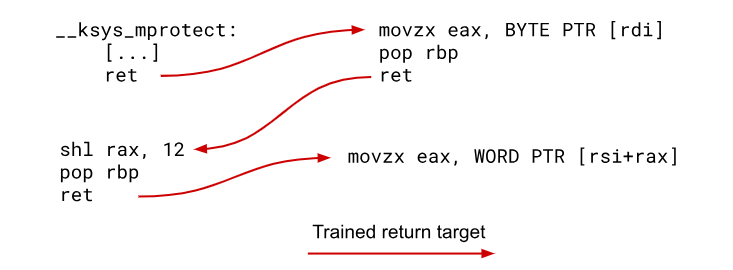
The researchers developed speculative Return Oriented Programming (ROP) techniques to create ideal disclosure gadgets, chaining multiple ROP gadgets to achieve byte-level precision without requiring knowledge of adjacent memory values.
On x86 we can use the clflush instruction to flush a cache line from the cache and the rdtsc instruction to time the execution of a memory access.

This approach significantly improves reliability compared to previous methods that relied on 16-bit loads with cascading failure potential.
The research team has dramatically improved upon the original Retbleed exploit published in 2022, achieving data leakage rates of approximately 13 KB/s with high accuracy.
Retbleed Vulnerability
The exploit successfully bypasses multiple modern security mechanisms, including Kernel Address Space Layout Randomization (KASLR) using prefetch side channels rather than the less reliable Prime+Probe methods.
The attack defeats Supervisor Mode Execution Prevention (SMEP) and Supervisor Mode Access Prevention (SMAP) by accessing kernel mappings through the physmap region.
The collisions are generated by XORing a virtual address with a constant documented. Executing the colliding branch in userspace once is enough to train the kernel return.
Crucially, the researchers demonstrated the exploit works from within Chrome renderer sandboxes and other restrictive environments that typically allow JIT compilation or FFI libraries.
The attack leverages the sandbox’s permission to map executable memory at specific addresses, which is commonly required for JavaScript engines and native code integration.
The exploit extends beyond local privilege escalation to cross-VM attacks in cloud environments.
Using AMD’s Secure Virtual Machine (SVM) technology, attackers can leak host machine memory from within a compromised virtual machine, potentially accessing data from other VMs running on the same physical hardware.
Even though it contains 2 returns the gadget executes quickly enough to leak data in the short speculation window and lets us read any data without knowing the byte that comes before it.
This capability poses significant risks for cloud computing providers where tenant isolation is critical.
Modern Computing Infrastructure
Retbleed affects a broad range of processors, including AMD Zen 1, Zen 1+, and Zen 2, as well as Intel Core 6th through 8th generation CPUs.
The vulnerability undermines retpoline mitigations that were specifically designed to prevent Spectre v2 attacks, as return instructions can be forced to behave like indirect branches under specific microarchitectural conditions.
Available mitigations carry substantial performance penalties, with AMD patches imposing 14% overhead and Intel mitigations resulting in up to 39% performance degradation.
More comprehensive branch predictor flushing approaches can impose performance penalties exceeding 200%.
The researchers have released a 4KB shellcode implementation (2.3KB compressed) that can be easily injected into compromised targets.
This compact footprint, combined with the exploit’s reliance on commonly-allowed system calls, makes it highly deployable across various attack scenarios.
While newer processors like AMD Zen 3 and Intel Alder Lake are not vulnerable to this specific variant, the research demonstrates how speculative execution vulnerabilities continue to pose fundamental challenges to modern computing security, particularly in multi-tenant cloud environments where hardware resources are shared among untrusted parties.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




