In a rapidly evolving cybercrime landscape, a new information-stealing malware dubbed Raven Stealer has emerged, directly targeting Windows users and leveraging Telegram for real-time data exfiltration.
First identified in July 2025 and actively distributed via GitHub and dedicated Telegram channels, this sophisticated Delphi/C++ malware lowers the barrier for even novice attackers to launch widespread credential theft campaigns.
Stealthy Operation and Modular Architecture
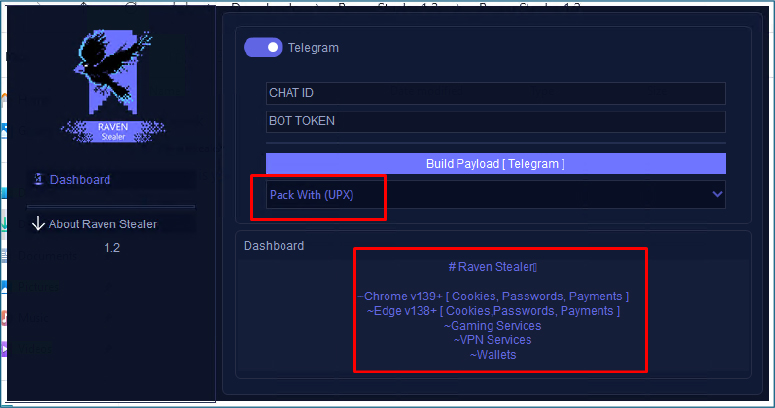
Raven Stealer stands out because of its modular architecture and streamlined deployment process.
The builder tool, written in Delphi, enables users to generate a customized payload, often packed with UPX for evasion, and directly embeds operational details, such as Telegram bot tokens and chat IDs.
The compact, UPX-packed binary executes completely hidden from view: operating with no user interface, console, or system tray icon, effectively bypassing scrutiny and lowering the risk of discovery.
Technically, Raven Stealer targets Chromium-based browsers (such as Google Chrome, Edge, and Brave), harvesting passwords, cookies, autofill data, and even payment information stored inside these browsers.
By leveraging sophisticated techniques like in-memory DLL injection and reflective process hollowing, Raven launches the browser in a suspended ‘headless’ state, disables built-in sandboxes, and injects its payload without touching disk.
The malware decrypts browser databases using stolen security contexts, allowing it to access sensitive information undetected.
Telegram-Powered Exfiltration and Organized Data Theft
All stolen data, spanning browser credentials, cookies, crypto wallets, VPN details, and system screenshots, is systematically organized in the user’s AppData directory before being archived into a ZIP file.
For exfiltration, Raven leverages curl.exe to send this ZIP archive directly to the attacker’s Telegram bot, utilizing the /sendDocument API method.
The use of embedded bot tokens and chat IDs enables instantaneous, encrypted delivery, while Telegram’s privacy and API flexibility make it a preferred C2 alternative for threat actors.
Each archive is uniquely named with the victim’s username, streamlining tracking and exploitation.
Raven Stealer also includes robust anti-analysis features, such as UPX packing to evade static detection, process stealth techniques (using ShowWindow SW_HIDE and WS_EX_TOOLWINDOW to remain invisible), and obfuscated in-memory resources.
Mitigation: Detection, Hardening, and Vigilance
Security experts recommend multiple layers of defense, including advanced EDR and heuristic antivirus tools to identify suspicious ZIP archives and network connections to api.telegram.org, application whitelisting to block unknown binaries in user folders, and regular YARA rule-based hunts using known IoCs and detection strings specific to Raven Stealer.
Users should avoid storing passwords in browsers, disable saving of payment and autofill data, and exercise caution when downloading applications from GitHub or engaging with Telegram-promoted tools.
Ultimately, Raven Stealer exemplifies the threat of modern, easily deployable malware-as-a-service, underscoring the importance of proactive detection, education, and rapid incident response in today’s digital ecosystem.
INDICATORS OF COMPROMISE
| S. N | indicators | type | context |
| 1. | 2e0b41913cac0828faeba29aebbf9e1b36f24e975cc7d8fa7f49212e867a3b38 | EXE | RavenStealer.exe |
| 2 | 28d6fbbdb99e6aa51769bde016c61228ca1a3d8c8340299e6c78a1e004209e55 | EXE | v8Axs07p.3mf.exe |
| 3. | 252fb240726d9590e55402cebbb19417b9085f08fc24c3846fc4d088e79c9da9 | DLL | PAYLOAD_ |






