A new Android malware campaign is causing financial havoc in Uzbekistan, as cybercriminals leverage Telegram to spread the Qwizzserial malware, an advanced SMS stealer that targets local banking systems.
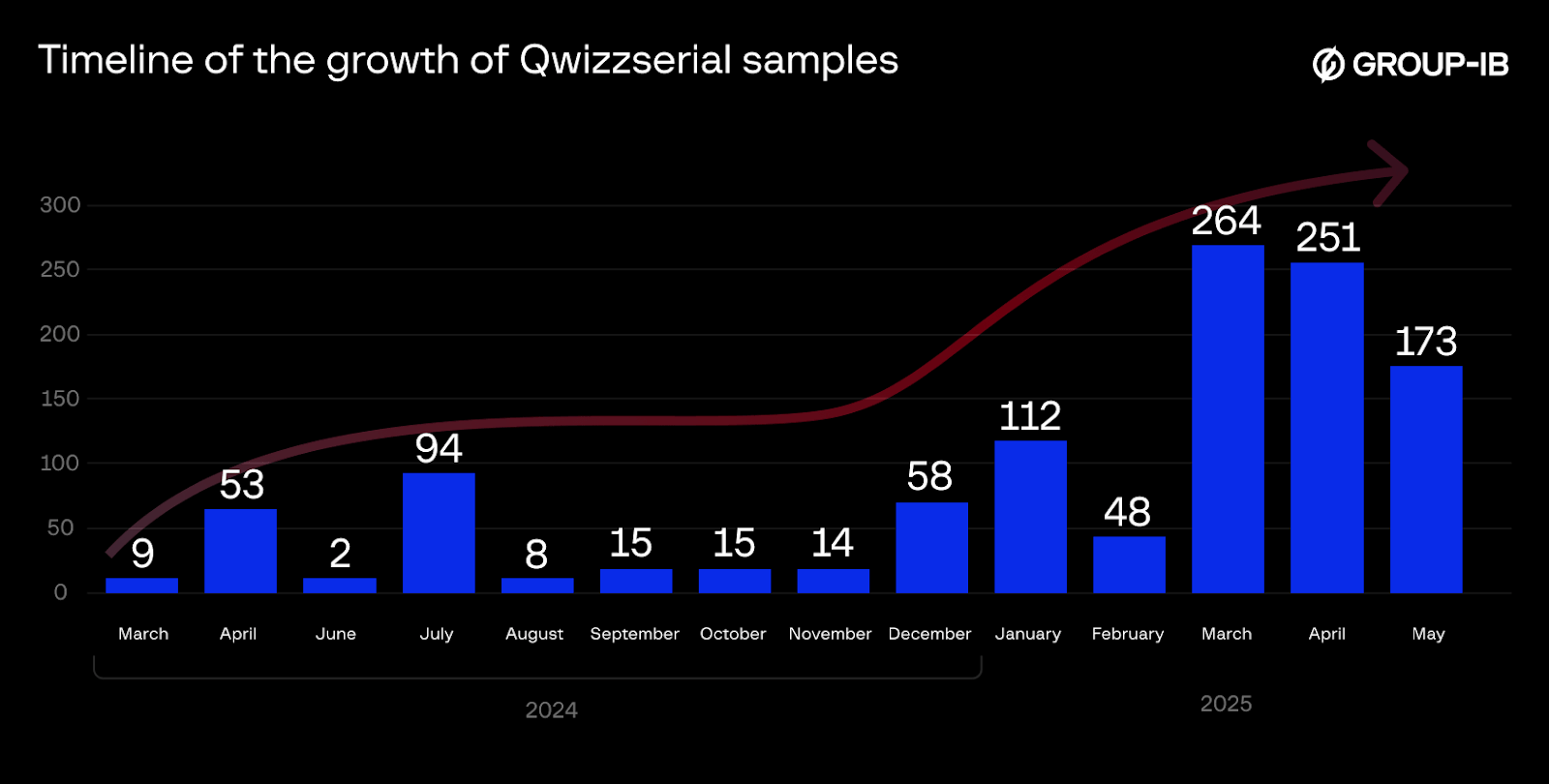
First detected by cybersecurity firm Group-IB in March 2024, Qwizzserial has rapidly infected an estimated 100,000 users, causing financial losses of at least $62,000 within just three months.
Fake Apps with Real Consequences
Qwizzserial is distributed primarily through Telegram channels, where threat actors pose as government organizations or banking authorities.
Victims are lured with promises of financial aid or essential updates, often through deceptive files named “Are these your photos?” or “Presidential Support.”
Once the victim downloads and installs the fake app, often disguised as a financial or government service, the malware requests sensitive permissions: access to SMS, phone state, and calling features.
Upon launch, early versions of Qwizzserial prompt users to enter personal and banking details, such as phone numbers and card information.
This data is surreptitiously exfiltrated using Telegram Bot APIs; more recent variants, however, send information through a dedicated command-and-control server.
Technical Analysis: Stealthy and Evolving
Qwizzserial’s technical design is notable for its adaptability and persistence. Key features include:
- SMS Interception: Once permissions are granted, Qwizzserial actively intercepts all inbound SMS messages, including two-factor authentication (2FA) codes sent by banking services. This enables attackers to bypass security measures and authorize fraudulent transactions.
- Data Exfiltration: Stolen information—including bank details, complete SMS archives, and SIM card metadata—is archived and transmitted to attackers via Telegram bots or HTTP POST to a hard-coded server (llkjllj[.]top).
- Obfuscation and Persistence: Later versions of Qwizzserial obfuscate their source code using NP Manager and Allatori Demo, display fake “preloader” screens, and prompt users to disable battery optimization, enabling the malware to run continuously in the background.
- Social Engineering: Fraudsters employ Telegram bots to customize malware builds, help distribute samples, and motivate their network by sharing profit figures in chat channels.
Local Focus, Global Lessons
Qwizzserial success is amplified by Uzbekistan’s heavy reliance on SMS-based banking authentication, with limited adoption of more secure methods, such as 3D Secure or biometrics.
This exposes users to significant risk, as cybercriminals can leverage intercepted codes and credentials to transfer funds, add cards to fraudulent accounts, and empty victims’ bank balances.
Protection advice: Users are advised never to install applications shared via messengers, always scrutinize permission requests, and rely solely on trusted app stores. Businesses and banks are advised to monitor account activity for suspicious logins and educate customers about phishing tactics.
.webp?w=696&resize=696,0&ssl=1)





