A sophisticated new attack technique that exploits FIDO key authentication systems by tricking users into scanning malicious QR codes with their multi-factor authentication (MFA) apps.
The attack, attributed to the PoisonSeed threat group known for cryptocurrency theft campaigns, represents a significant evolution in phishing tactics that specifically targets organizations using hardware-based authentication tokens.
The attack begins with a traditional phishing email directing victims to a fraudulent login page designed to mimic their organization’s authentic Okta authentication portal.
The malicious site, hosted on domains like okta[.]login-request[.]com, captures user credentials when victims enter their username and password.
However, the attack’s sophistication becomes apparent when dealing with FIDO key-protected accounts.
Rather than being blocked by the hardware token requirement, the phishing site automatically forwards the stolen credentials to the legitimate login portal while simultaneously requesting the cross-device sign-in feature.
This legitimate FIDO functionality is designed to help users authenticate from unregistered devices by utilizing their mobile MFA apps.
The authentic login portal then generates a QR code, which the phishing site immediately captures and displays to the victim.
When users scan this QR code with their MFA authenticator apps, they unknowingly complete the authentication process for the attackers.
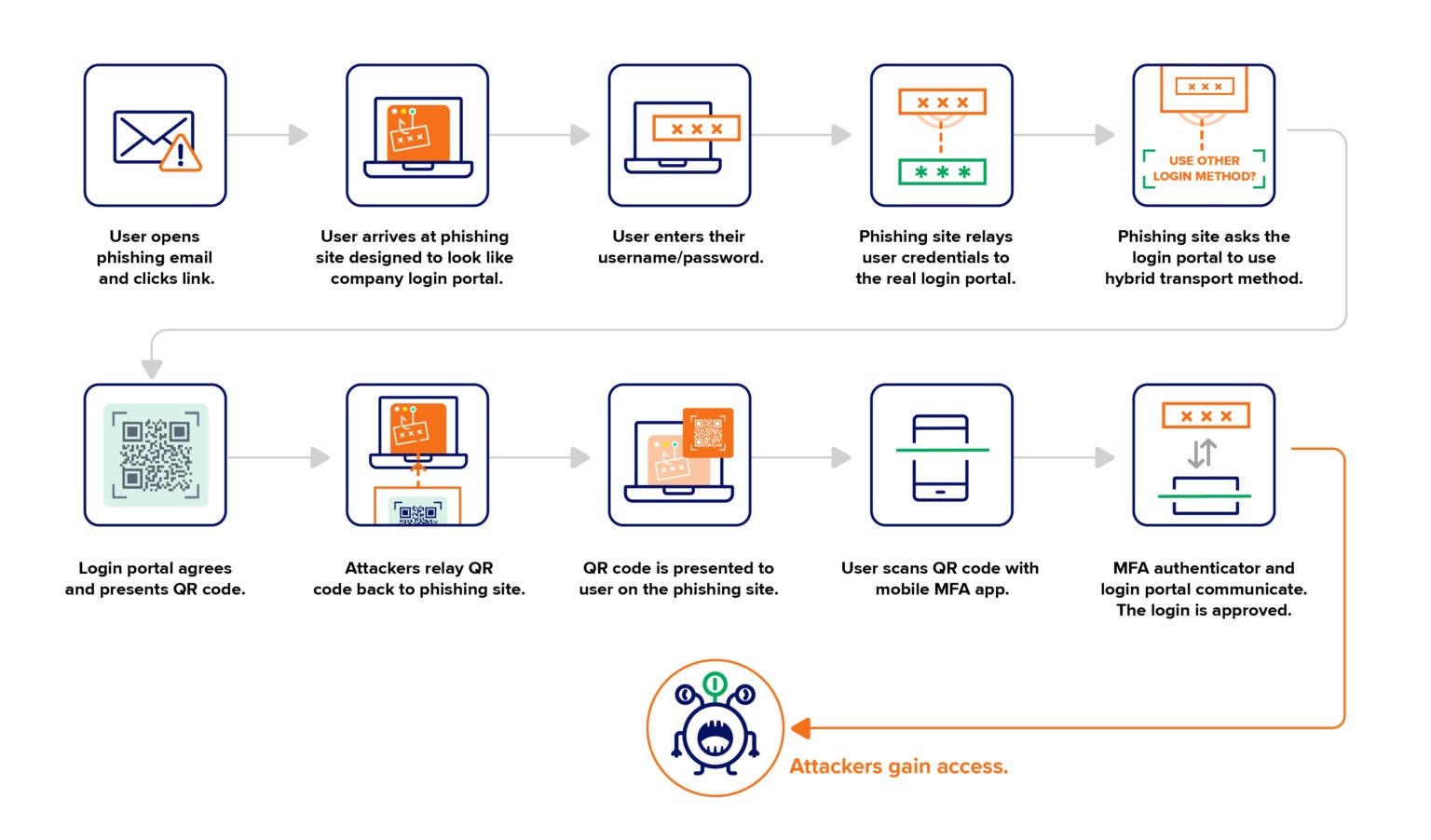
The communication between the legitimate login portal and the victim’s MFA app grants the threat actors full access to the compromised account, effectively bypassing the FIDO key’s security protections entirely.
Enterprise Security Posture
This attack technique represents a concerning development in the cybersecurity landscape, where identity-based attacks already account for approximately 66% of security incidents.
The method exploits a fundamental assumption in cross-device authentication: that the person scanning the QR code is the legitimate user attempting to access their own account from a trusted location.
The attack’s effectiveness stems from its abuse of legitimate security features rather than exploiting actual vulnerabilities in FIDO key technology.
By leveraging adversary-in-the-middle (AitM) techniques combined with social engineering, attackers can circumvent what many consider the gold standard of MFA protection.
The technique grants attackers access to sensitive applications, documents, and administrative tools associated with the compromised accounts.
Security researchers have also addressed related incidents where attackers, after gaining initial access through similar methods, proceed to reset passwords and enroll their own FIDO keys in compromised accounts.
Monitoring Recommendations
Organizations can implement several defensive measures to detect and prevent these attacks.
Authentication log analysis should focus on identifying cross-device sign-in requests originating from unusual geographic locations, unexpected FIDO key registrations, and multiple keys being registered in quick succession for individual users.
A critical technical safeguard involves enabling Bluetooth communication requirements between mobile MFA devices and the systems being accessed.
This proximity requirement ensures users must be physically present at the login location when scanning QR codes, effectively reducing the attack success rate to near zero.
Security teams should also monitor for unfamiliar or non-standard FIDO key brands being registered, particularly if organizations maintain standardized hardware token policies.
Regular audits of registered authentication devices and immediate session termination following suspected compromise remain essential incident response practices.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




