A sophisticated phishing campaign targeting the open-source Node.js ecosystem has rocked the developer community, exposing millions to risk by hijacking widely used npm packages.
The attack, first observed with a typosquatted phishing domain (npnjs[.]com) and spoofed support@npmjs.org emails, now includes a direct compromise of the massively popular “is” package, downloaded nearly 2.8 million times every week.
How the Phishing Campaign Unfolded
The attack began with carefully crafted phishing emails impersonating the legitimate npm registry.
By leveraging a convincingly similar domain and sending requests for credentials, threat actors managed to harvest maintainer logins, an issue made worse by lax email authentication (missing DMARC and SPF records on the real npmjs.org domain).
Once inside, attackers could publish rogue versions of trusted packages through stolen npm tokens.
Developers who clicked through the fake login page unknowingly granted access to packages that collectively received tens of millions of weekly downloads.
In the days that followed, maintainers lost control of several high-profile libraries, including. eslint-config-prettier, eslint-plugin-prettier, and, critically, the utility package is.
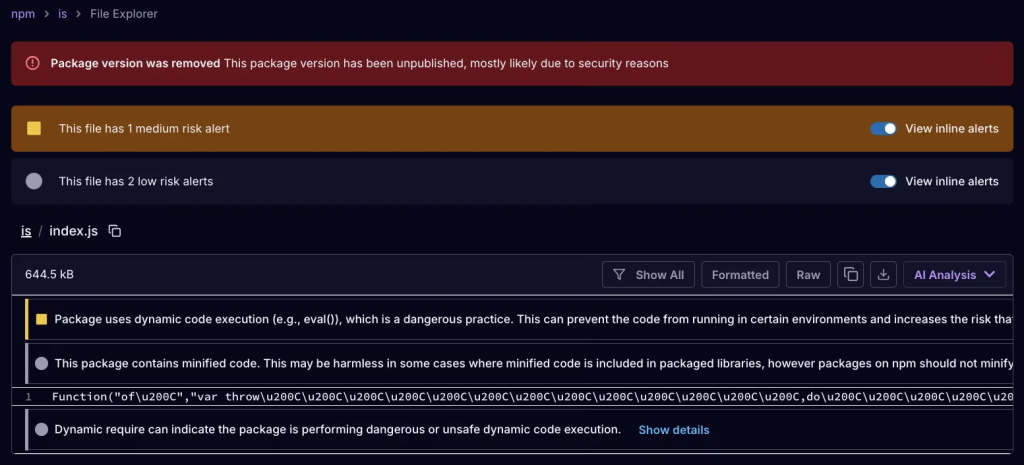
Malicious Payloads Hidden in Plain Sight
While previous incidents have involved shell scripts or lightweight malware, this campaign raised the stakes. Malicious versions of affected packages shipped varying payloads designed for different platforms.
- Windows Systems: In
eslint-config-prettier, attackers embedded a Windows-only DLL (node-gyp.dll) carrying “Scavenger”—a sophisticated infostealer. Scavenger deploys anti-analysis tricks, encrypted C2 communications, and targets browser credentials, session data, and configuration secrets such as.npmrc.netrc. - Cross-Platform Threats: The compromised
ispackage (versions 3.3.1 and 5.0.0) included a heavily obfuscated JavaScript loader. Without dropping files, it reconstructs malware in memory, fingerprints the host system, and sends environment details, including access tokens, over a WebSocket connection to a remote server. Critically, any code sent to the infected system is executed instantly, creating a live remote shell for attackers.
Both types of malware allow attackers to persist on machines and exfiltrate sensitive data. On Windows, post-infection symptoms included Chrome security warnings and suspected SSH key compromise, sometimes forcing developers to wipe entire drives to recover.
Widespread Impact and Defenses
The campaign quickly widened: other libraries such as got-fetch, synckit, and @pkgr/core were compromised via stolen accounts.
With the npm ecosystem’s “install-once, update-forever” culture, the infected packages spread rapidly across continuous integration systems and local builds worldwide.
Indicators of Compromise:
Developers and security teams are advised to check for the following malicious package versions:
eslint-config-prettier(8.10.1, 9.1.1, 10.1.6, 10.1.7)eslint-plugin-prettier(4.2.2, 4.2.3)is(3.3.1, 5.0.0)got-fetch(5.1.11, 5.1.12)synckit@0.11.9@pkgr/core@0.2.8napi-postinstall@0.3.1
This incident demonstrates once more that a single compromised account or package can swiftly compromise the entire supply chain. Developers are advised to rotate credentials, diligently audit installed package versions, and avoid blind dependency updates.
Security tools, such as real-time dependency scanners and multi-factor authentication, are no longer optional; they’re vital for defending the future of open-source development.






