A sophisticated global botnet campaign targeting Voice over Internet Protocol (VOIP) devices with default credentials, beginning with an unusual concentration of malicious activity in rural New Mexico.
The investigation, published on July 24, 2025, reveals how approximately 500 compromised devices worldwide are participating in coordinated Telnet-based attacks, highlighting significant vulnerabilities in internet-facing telecommunications infrastructure.
The discovery began when GreyNoise engineers noticed an anomalous cluster of malicious IP addresses originating from a sparsely populated region of New Mexico with just over 3,000 residents.
Investigation revealed that approximately 90 IP addresses were all connected to a single internet service provider, the Pueblo of Laguna Utility Authority.
Analysis of the initial IP address (137.118.82.76) revealed multiple concerning security indicators, including Telnet brute-force attempts, generic IoT default password attacks, Mirai botnet signatures, and D-Link hardcoded Telnet exploitation attempts.
The concentration of malicious activity from such a small geographic area prompted researchers to conduct a deeper investigation using AI-powered analysis tools, including their Model Context Protocol server integrated with Claude AI.
The technical analysis confirmed that the compromised systems were primarily VOIP-enabled devices, with enrichment data suggesting involvement of hardware from Cambium Networks.
Researchers noted that 100% of the traffic from this region was Telnet-based, indicating a coordinated compromise of similar network infrastructure.
VOIP Botnet Targets Routers
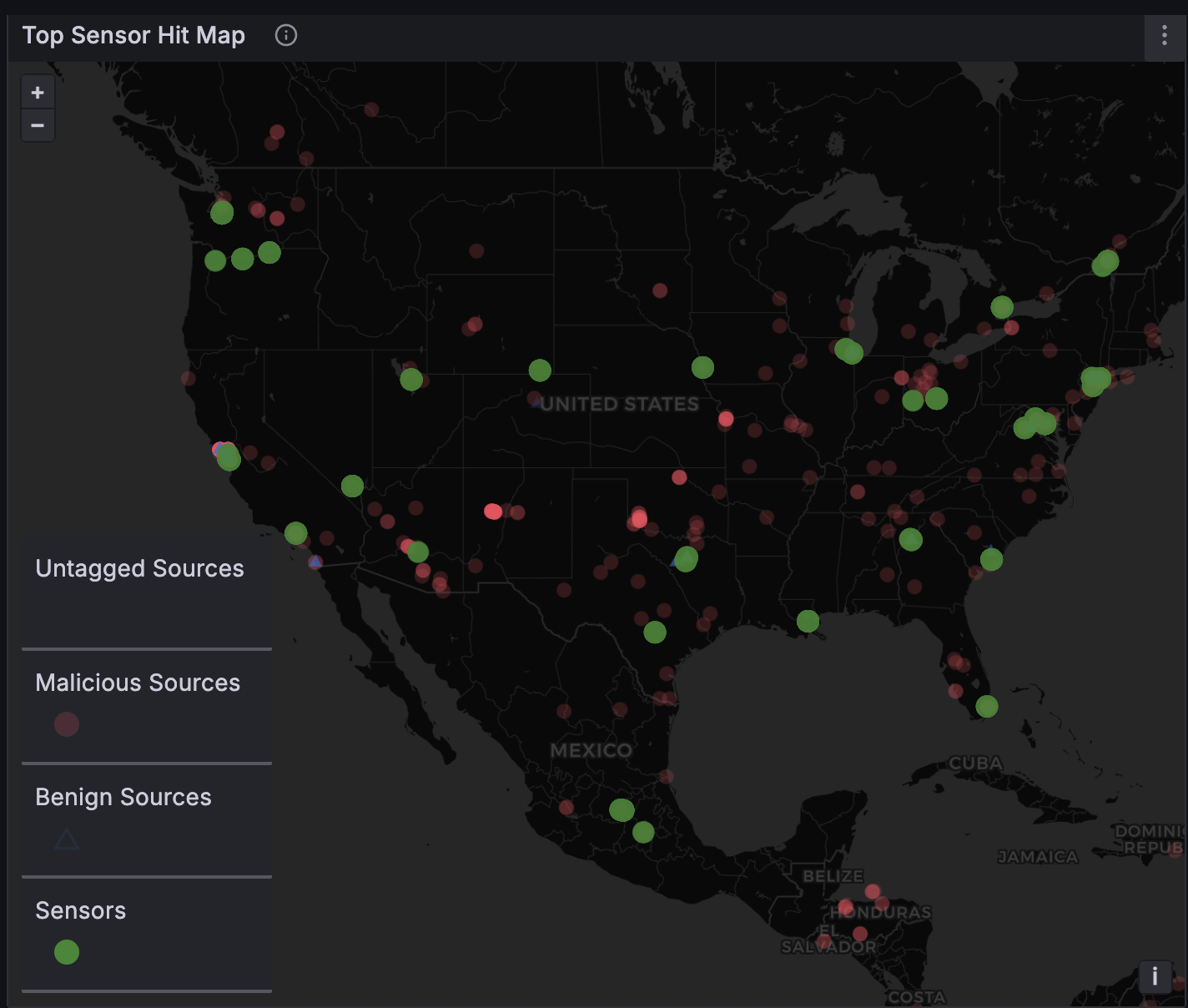
Expanding their investigation beyond New Mexico, GreyNoise researchers identified approximately 500 IP addresses globally exhibiting identical attack patterns.
The key technical indicator was a unique JA4t signature (5840_2-4-8-1-3_1460_1) that represented 90% of the malicious traffic, suggesting the compromised devices shared similar hardware and firmware configurations.
The global botnet demonstrated consistent behavioral characteristics including Telnet login attempts using weak or default credentials, high session volumes, and scanning patterns aligned with known Mirai botnet variants.
This widespread activity indicated that VOIP devices across multiple networks and geographic regions were being systematically compromised and recruited into the botnet infrastructure.
Interestingly, when GreyNoise team members mentioned the investigation on social media, the New Mexico traffic ceased completely, though global activity resumed shortly afterward.
This response pattern suggests that the botnet operators actively monitor security research and can rapidly adjust their operations when detected.
Critical Infrastructure Vulnerabilities
The investigation highlights significant security gaps in VOIP infrastructure, which researchers note often runs on outdated Linux based firmware with Telnet services exposed by default.
These devices are frequently internet-facing, receive minimal security monitoring, and are infrequently updated with security patches.
Some Cambium routers involved in the campaign may still be running firmware versions affected by a remote code execution vulnerability disclosed in 2017, demonstrating how legacy security flaws continue to provide attack vectors years after initial disclosure.
GreyNoise researchers emphasize that VOIP systems are commonly overlooked in organizational security monitoring, while small utilities and internet service providers may unknowingly contribute infrastructure to global botnets.
The company recommends immediately blocking identified malicious IP addresses, auditing Telnet exposure on VOIP systems, and rotating or disabling default credentials on edge and small office/home office devices.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




