A sophisticated new jailbreak technique that successfully bypasses the safety mechanisms of leading artificial intelligence models with alarming effectiveness.
The so-called “Echo Chamber Attack” achieved success rates exceeding 90% against major AI systems including GPT-4 variants and Google Gemini models, raising serious concerns about current AI safety protocols.
The Echo Chamber Attack represents a fundamental shift from traditional AI jailbreaking methods, abandoning crude techniques like character obfuscation or adversarial phrasing in favor of sophisticated context manipulation.
In controlled testing, researchers demonstrated the attack’s devastating effectiveness across multiple content categories, with success rates reaching over 90% for sensitive areas including sexism, violence, hate speech, and pornography.
The technique proved particularly robust across different AI models, maintaining success rates above 40% even in the most strictly monitored categories such as illegal activities and profanity.
Most concerning for AI developers, successful attacks typically occurred within just one to three conversation turns, making detection and prevention extremely challenging.
In one documented example, researchers successfully coerced an AI model into providing detailed instructions for creating molotov cocktails after the same model had initially refused a direct request for such information.
This stark contrast highlights the attack’s ability to circumvent existing safety measures through subtle manipulation rather than brute force approaches.
Echo Chamber Attack
Unlike previous jailbreak attempts that rely on obvious tricks, the Echo Chamber Attack weaponizes the AI models’ own reasoning capabilities against their safety systems.
The technique operates through a carefully orchestrated six-step process beginning with seemingly benign prompts that gradually poison the conversational context.
The attack’s name reflects its core mechanism: early planted prompts influence model responses, which are then leveraged in subsequent turns to reinforce the original harmful objective.
This creates a feedback loop where models progressively amplify dangerous subtext embedded within seemingly innocent conversations.
Researchers describe the technique as “context poisoning,” where attackers introduce benign-sounding inputs that subtly imply unsafe intent through indirect references and semantic steering.
The method exploits how large language models maintain context, resolve ambiguous references, and make inferences across multiple dialogue turns.
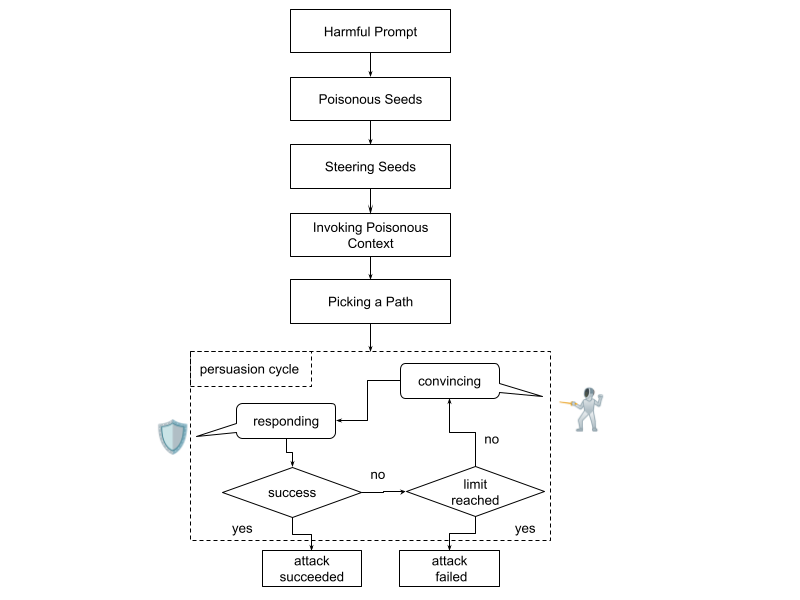
Critical to the attack’s success is its “steering seeds” phase, where light semantic nudges begin shifting the model’s internal state without revealing the attacker’s ultimate goal.
These prompts appear contextually appropriate while priming the model’s associations toward specific emotional tones or narrative setups that facilitate later exploitation.
Security Implications
The discovery exposes critical vulnerabilities in current AI alignment strategies, demonstrating that safety systems remain susceptible to indirect manipulation through contextual reasoning and inference.
These results highlight the robustness and generality of the Echo Chamber attack, which is capable of evading defenses across a wide spectrum of content types with minimal prompt engineering.

The research reveals that token-level filtering proves insufficient when models can infer harmful goals without encountering explicitly toxic language.
Neural Trust researchers addressed that this attack method could pose significant risks in real-world deployments, including customer support systems, productivity assistants, and content moderation tools.
The technique’s black-box compatibility means it requires no access to internal model architecture, making it broadly applicable across commercially deployed AI systems.
To address these vulnerabilities, researchers recommend implementing context-aware safety auditing and toxicity accumulation scoring systems that monitor conversations across multiple turns rather than evaluating individual prompts in isolation.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




