A critical vulnerability in macOS that allows attackers to escalate privileges and gain root access through a vulnerability in the system’s service management mechanism.
The exploit, dubbed “Daemon Ex Plist,” targets Apple’s launch daemon configuration files and has been found to affect numerous popular applications, particularly VPN services.
These services are managed through property list (plist) files that contain configuration details including executable paths, launch conditions, and user privileges.
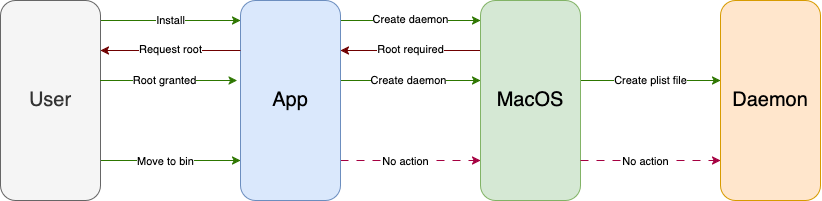
The critical vulnerability occurs when developers specify executable paths in directories that regular users can access, particularly within the /Applications folder.
When applications are uninstalled but leave their plist files behind in the privileged /Library/LaunchDaemons directory, attackers can exploit this oversight by creating malicious executables at the specified paths.
“If the developer specifies a path to the service that a standard user can access, then any program with user privileges can create an executable file at that path,” the researchers explained.
This allows attackers who have already compromised a user account to replace legitimate service binaries with malicious code that will execute with root privileges.
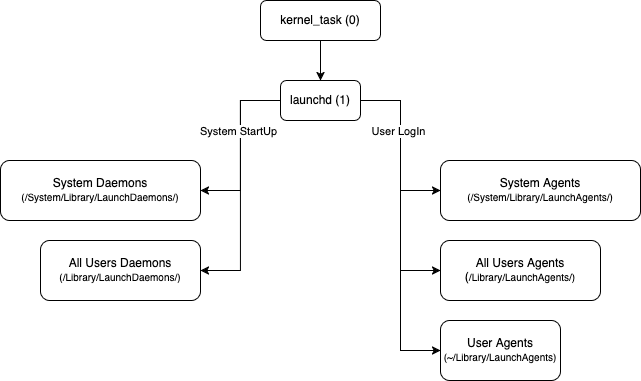
The vulnerability stems from improper configuration of macOS Agents and Daemons, specialized services that automatically launch during system startup or user login.
The exploitation process involves two main scenarios. In the most common case, services configured with the “RunAtLoad” parameter automatically execute during system boot, giving attackers immediate root access after a restart.
A second variant targets MachServices, which remain dormant until explicitly invoked through Inter-Process Communication (IPC) mechanisms.
VPN and Software Applications
The research team conducted extensive testing and discovered vulnerabilities in multiple high-profile applications. VPN services proved particularly susceptible due to their need for system-level network configuration changes.
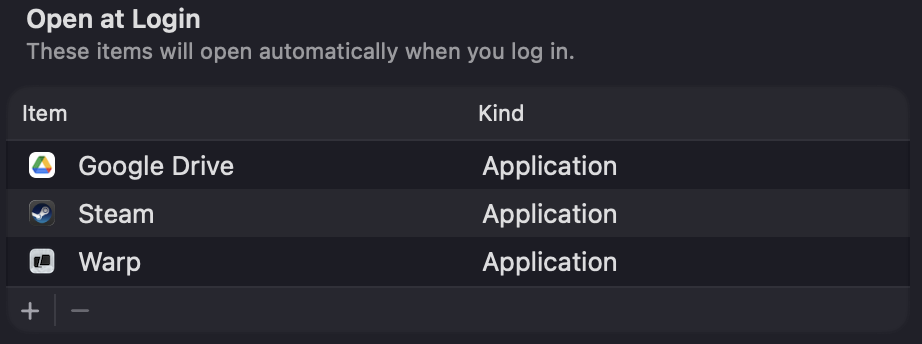
Affected products include Mozilla VPN, Tunnelblick, Pritunl, Cloudflare Warp, Private Internet Access, ExpressVPN, Amnezia VPN, Mullvad VPN, and Red Shield VPN.
Beyond VPN applications, the vulnerability also impacts other software categories, including Microsoft OneDrive and Logitech G Hub.
The researchers noted that “several other vendors are also vulnerable to this issue, and have not yet released a patch.”
The widespread nature of the vulnerability highlights a systemic issue in how macOS applications handle privileged service configuration.
Many developers appear unaware of the security implications of placing executable files in user-accessible directories while maintaining root-level service configurations.
Protective Measures
For immediate protection, users can audit their systems by examining services in the /Library/LaunchDaemons directory and checking executable paths for potential vulnerabilities.
The researchers provided command-line tools to help identify potentially dangerous configurations and verify file permissions.
Developers have two primary remediation options. The preferred solution involves relocating service executables to the /Library/PrivilegedHelperTools directory, which is inaccessible to regular users.
Adobe successfully implements this approach for their update services. Alternatively, developers can create cleanup services that monitor application folders and automatically remove plist files when applications are uninstalled, similar to Microsoft Defender’s implementation.
The discovery underscores the importance of secure service configuration in macOS environments and the need for developers to carefully consider privilege escalation risks when designing automated services.
Users are advised to keep applications updated and carefully review system permissions when installing new software.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




