A sprawling network of AsyncRAT variants that have significantly expanded the malware’s capabilities, with new discoveries revealing exotic plugins ranging from jump-scare mechanisms to sophisticated USB-based malware spreaders.
The open-source remote access trojan, originally released in 2019, has evolved into a complex ecosystem of forks that pose escalating threats to global cybersecurity.
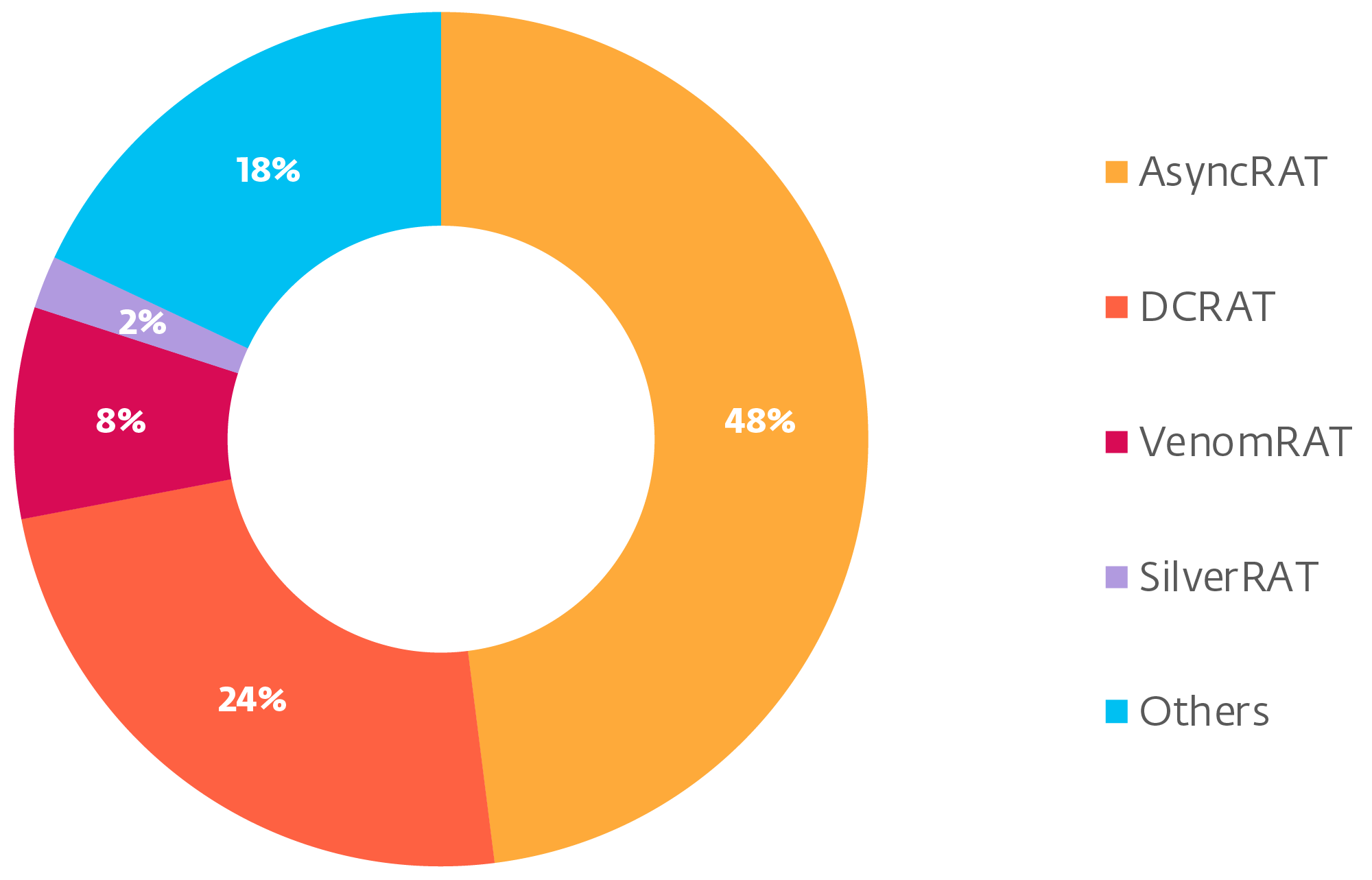
Recent analysis reveals that DcRat and VenomRAT have emerged as the most widely deployed AsyncRAT variants, together accounting for a significant portion of malware campaigns observed in Q2 2024.
These sophisticated forks have introduced substantial improvements over the original AsyncRAT framework, including enhanced evasion techniques such as AMSI and ETW patching, which disable security features that detect and log malicious behavior.
DcRat notably implements MessagePack for more efficient binary data serialization and features an antiprocess system that automatically terminates security tools including Task Manager, Process Hacker, and Windows Defender processes.
The variant has expanded its plugin arsenal to include webcam access, microphone recording, Discord token theft, and a collection of disruptive capabilities dubbed “fun stuff” that can manipulate victim systems in various ways.
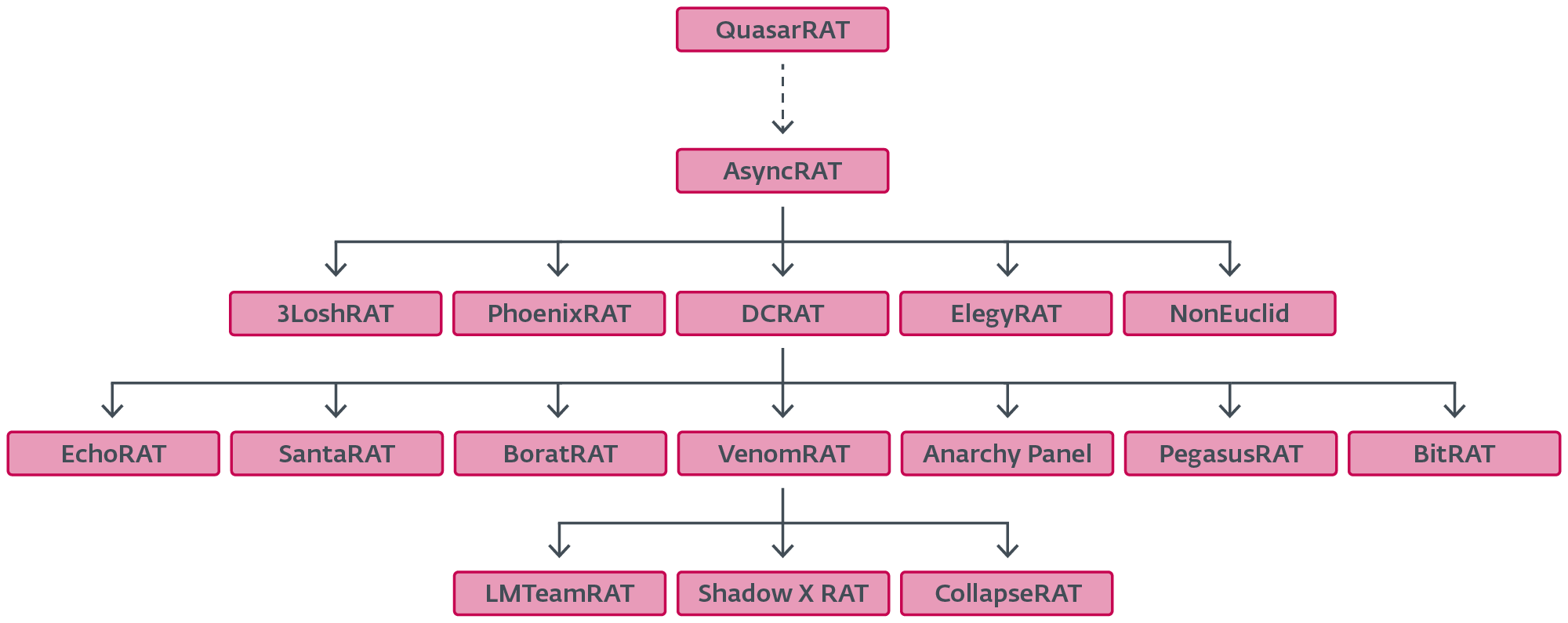
VenomRAT, likely inspired by DcRat’s architecture, has grown so feature-rich that security researchers consider it a separate threat entirely.
Despite their enhanced capabilities, both variants maintain the core AsyncRAT client structure, allowing for easier detection and analysis by security professionals.
Creative Malware Development
Among the lesser-known variants, NonEuclid RAT stands out for its unusual plugin collection that extends far beyond traditional RAT functionality depicts the distribution of the most prevalent forks according to our telemetry.
The variant includes a “Screamer.dll” plugin that delivers jump-scare attacks using five pre-bundled images combined with WAV audio files, demonstrating how threat actors are exploring psychological manipulation techniques.
More concerning is the WormUsb.dll plugin, which functions as a sophisticated malware spreader targeting PE files across multiple locations.
The plugin can compromise individual executables, target files in personal folders, or spread to all drives excluding the primary C drive.
When executed, infected files decrypt and run both the malicious payload and the original program, maintaining stealth while propagating the infection.
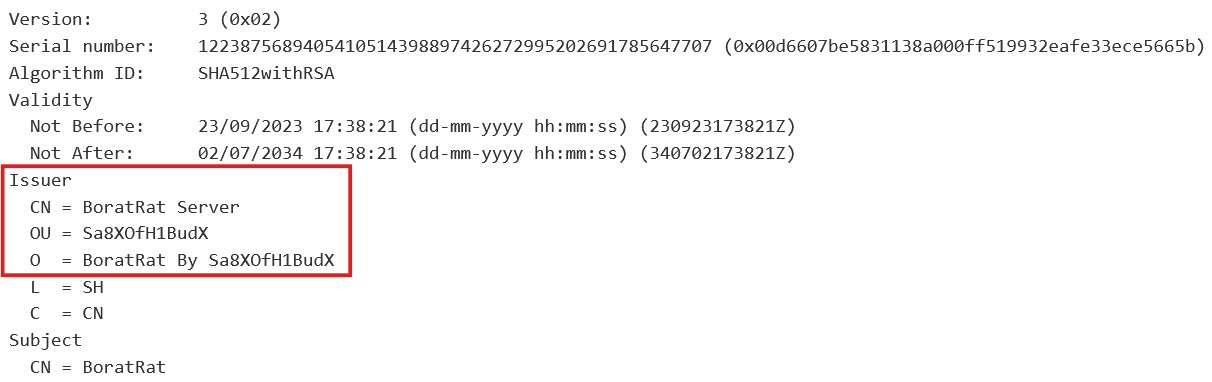
Other notable plugins include a cryptocurrency clipboard replacer (cliper.dll), an SSH and FTP brute forcer (Brute.dll), and a rudimentary signature-based file deletion tool deceptively named “Signature Antivirus.dll” DER-encoded certificate that reveals the BoratRAT fork, after extraction and decoding.
These specialized tools demonstrate the modular approach that makes AsyncRAT variants particularly dangerous and adaptable.
Rising Threat Complexity
According to Report, proliferation of AsyncRAT forks represents a significant evolution in the malware landscape, with researchers identifying variants like JasonRAT featuring satanic-themed variable naming.
Extended Morse code obfuscation, and XieBroRAT incorporating Chinese localization with browser credential stealing capabilities.
The widespread availability of open-source malware frameworks has dramatically lowered barriers to entry for cybercriminals, enabling even novices to deploy sophisticated attack tools with minimal technical expertise.
This democratization of malware development, combined with the rising popularity of AI language models, threatens to accelerate the creation and customization of malicious tools further.
Security experts emphasize that the evolving AsyncRAT ecosystem underscores the critical importance of proactive detection strategies and behavioral analysis to address these emerging threats effectively in an increasingly complex cybersecurity landscape.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




