A zero-day vulnerabilities in two discontinued network devices, demonstrating the persistent security risks posed by end-of-life hardware.
The team won runner-up for “Most Innovative Exploitation Technique” at DistrictCon’s inaugural Junkyard competition in February 2025, showcasing how abandoned devices become perfect targets for attackers when manufacturers cease security updates.
The DistrictCon Junkyard competition specifically targets end-of-life devices to raise awareness about the security implications of abandoned hardware.
Trail of Bits researchers Alan Cao and Will Tan focused on two popular home network security devices: a Netgear WGR614v9 router and a BitDefender Box V1, both designed to protect home networks but left vulnerable due to years without security patches.
The researchers developed multiple exploit chains for each device, achieving remote root shell access from the local network.
Their work demonstrates how vulnerabilities in discontinued devices remain “frozen in time like fossils,” creating persistent attack vectors that will never be patched.
The team has made their complete technical analysis available on GitHub, including proof-of-concept videos demonstrating each exploitation technique.
Netgear Router Exploitation
The Netgear WGR614v9 router, running a MIPS32-based system, fell victim to a sophisticated four-vulnerability chain targeting its Universal Plug-and-Play (UPnP) daemon.
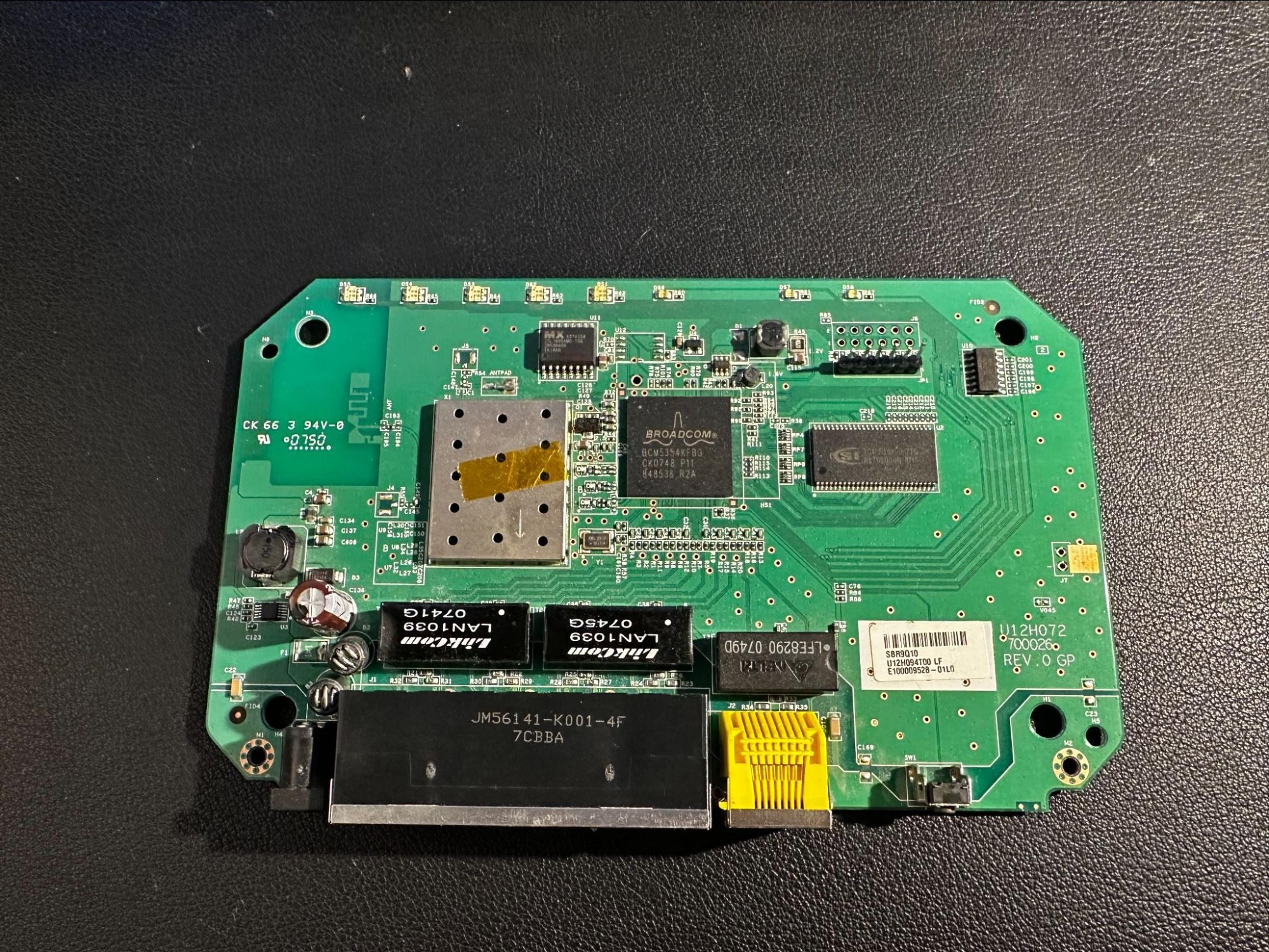
After gaining hardware access through the device’s UART interface, researchers identified critical vulnerabilities in the SOAP message handler, including an authentication bypass allowing password resets and three buffer overflow vulnerabilities affecting both BSS and stack memory regions.
The team developed three distinct exploitation techniques, including an innovative “bashsledding” approach that represents a clever variation of traditional nopsled techniques.
By spraying shell command payloads into memory-mapped NVRAM through the router’s domain-blocking feature and prepending sequences of spaces, researchers created reliable code execution regardless of exact landing position.
Their “bigfish_littlepond” exploit demonstrated how limited memory corruption bugs can be pivoted into stronger command injection attacks by modifying adjacent string pointers.
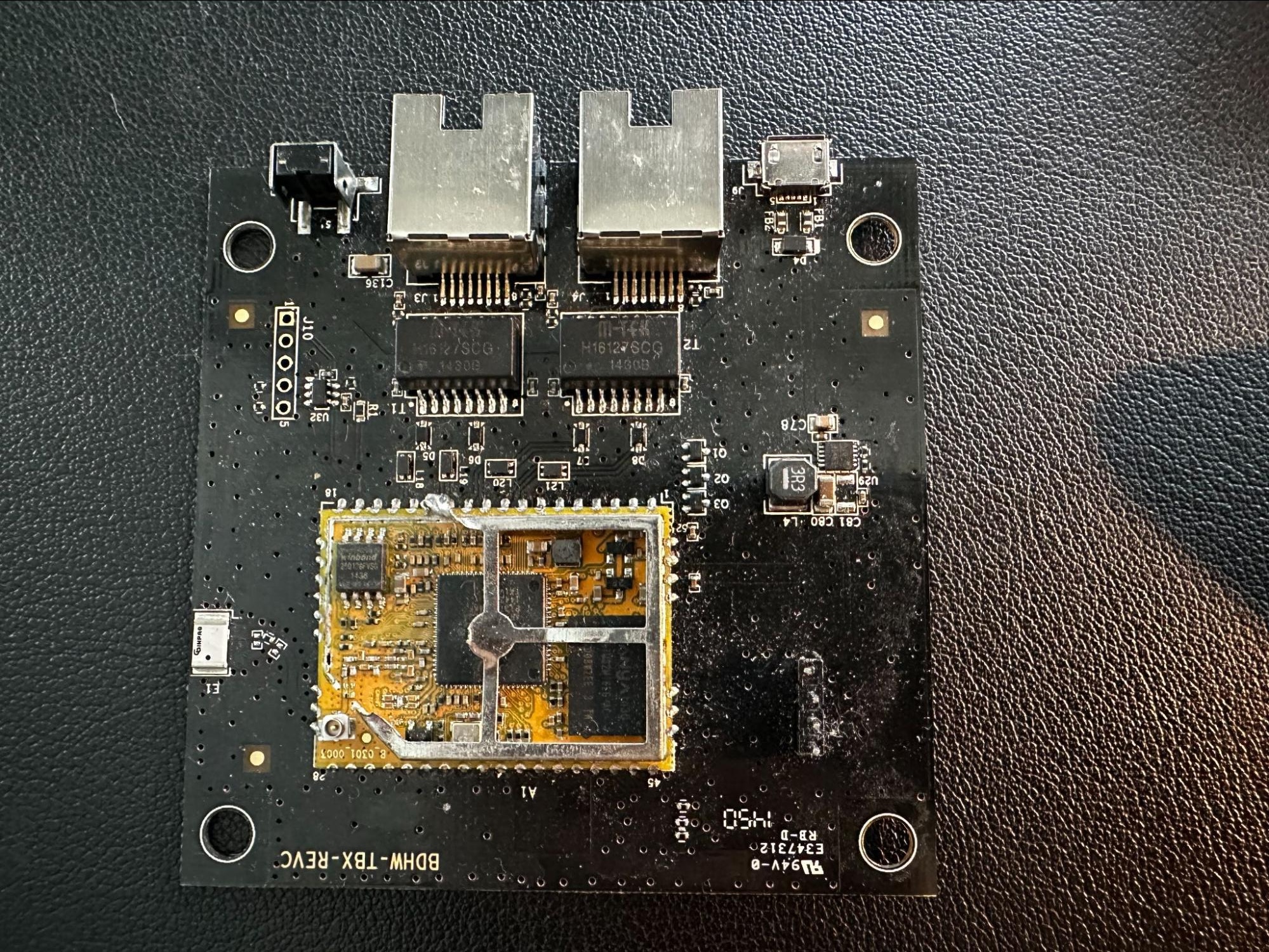
BitDefender Security Appliance
According to Report, BitDefender Box V1 presented an ironic target—a security appliance discontinued in July 2021 that was originally designed to protect home networks.
The device operated by inserting itself into network paths and redirecting traffic through its proxy for threat scanning, yet contained a completely unauthenticated firmware update mechanism.
Researchers extracted firmware using hardware techniques, accessing a Winbond W25Q128FV SPI NOR flash chip with specialized programming equipment.
Despite the device implementing RSA signature verification for firmware updates, the team discovered that BitDefender had distributed vulnerable older firmware versions within their mobile application APKs.
By locating an ancient APK version on VirusTotal, researchers recovered firmware version 1.3.11.490 with valid signatures but lacking critical security protections.
The exploitation chain involved multiple endpoints including authentication token clearing, firmware upload, image decoding, and a vulnerable MD5 parameter containing a basic command injection vulnerability.
The newer firmware versions had implemented proper input validation, but the downgrade attack bypassed these protections entirely.
These discoveries underscore broader IoT security patterns and highlight the importance of robust version verification in update mechanisms.
The researchers recommend that consumers evaluate manufacturer support timelines before purchasing devices and consider open-source alternatives when possible.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




