Three critical vulnerabilities in SonicWall’s SMA100 series SSL-VPN appliances, highlighting persistent security vulnerabilities in network infrastructure devices.
The vulnerabilities, affecting firmware version 10.2.1.15, include two pre-authentication buffer overflow conditions and a cross-site scripting vulnerability, demonstrating what researchers describe as “trivially avoidable” programming errors that continue to plague modern network appliances.
The most severe vulnerability, designated CVE-2025-40596, represents a stack-based buffer overflow that can be triggered without authentication.
Researchers identified the vulnerability within the /usr/src/EasyAccess/bin/httpd binary, which handles incoming HTTP requests for the SSL-VPN service. The vulnerability stems from improper use of the sscanf function when parsing URIs beginning with /__api__/.
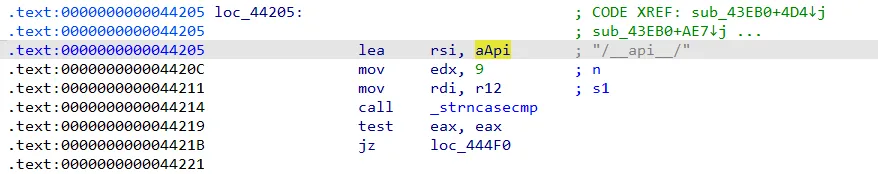
The affected code attempts to extract user-provided URI components into a fixed 0x800-byte stack buffer without implementing proper bounds checking.
Specifically, it copies part of the user-provided URI into the memory address stored in the rcx register.
Attackers can exploit this by sending malformed requests with excessively long URI paths, potentially triggering a crash or, in some configurations, achieving code execution.
The vulnerability can be reproduced with a simple HTTP request containing approximately 3,000 ‘A’ characters in the URI path.
A second buffer overflow, CVE-2025-40597, affects heap memory management within the mod_httprp.so shared library responsible for HTTP reverse proxy functionality.
This vulnerability occurs during Host header parsing, where developers attempted to use the supposedly safer __sprintf_chk function but undermined its protection by passing -1 as the bounds-checking parameter, effectively disabling overflow protection entirely.
N-day Vulnerabilities in SonicWall SMA100
The heap-based overflow in CVE-2025-40597 demonstrates particularly concerning coding practices.
The vulnerable code allocates an 0x80-byte heap chunk via calloc but fails to enforce proper size limits during string copying operations.
When processing oversized Host headers, the overflow can corrupt adjacent heap metadata, potentially leading to arbitrary code execution under specific conditions.
Researchers successfully demonstrated heap corruption by sending HTTP requests with Host headers containing approximately 750 characters.
While the vulnerability requires precise timing and heap manipulation for reliable exploitation, its presence in a pre-authentication code path represents a significant security risk for organizations relying on SonicWall SSL-VPN infrastructure.
The result? A good old-fashioned alert(1) – 2005 (or Fortinet in 2025) called, it wants its vuln back.
The research team noted challenges in developing reliable exploitation techniques due to concurrent background processes interfering with heap state manipulation, though they emphasized that the fundamental vulnerability remains exploitable under controlled conditions.
Legacy XSS Vulnerability
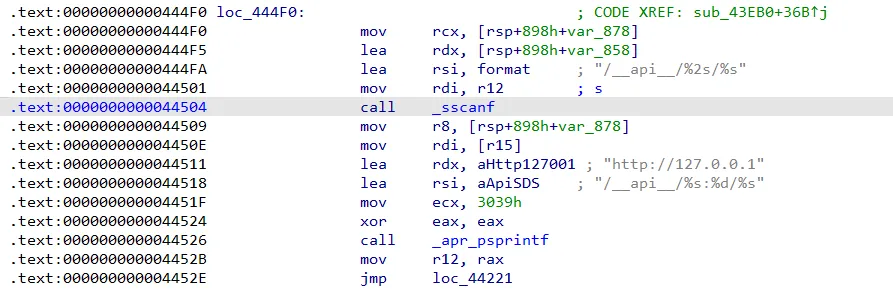
Completing the trio of vulnerabilities, CVE-2025-40598 represents a reflected cross-site scripting vulnerability discovered in the radiusChallengeLogin CGI endpoint.
SonicWall has addressed these vulnerabilities and published security advisory SNWLID-2025-0012, recommending immediate firmware updates for affected systems.
The vulnerability allows attackers to inject arbitrary JavaScript code through the state parameter, which is reflected directly into HTTP responses without sanitization.
Despite SMA100 devices offering web application firewall capabilities, researchers found these protections disabled on management interfaces, allowing even basic XSS payloads to execute successfully.
The vulnerability requires user interaction but could facilitate credential theft or session hijacking in targeted attacks.
The discoveries underscore ongoing challenges in network appliance security, where fundamental programming errors continue to create significant attack surfaces in critical infrastructure components.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




