Recent cybersecurity research has exposed a sophisticated malware campaign targeting macOS users through a technique dubbed “Clickfix.”
This attack leverages malicious AppleScripts (osascripts) to siphon sensitive data, including browser cookies, passwords, cryptocurrency wallet details, and browser plugin information.
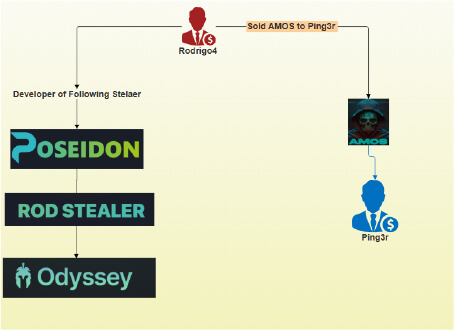
The operation, attributed to a rebranded infostealer known as Odyssey Stealer, highlights the growing threat landscape for Mac users, particularly those involved in finance and cryptocurrency.
The Clickfix Attack Chain
The Clickfix technique begins with the creation of typosquatted or visually similar domains, often mimicking official Apple App Store, finance, or cryptocurrency news sites.
When users inadvertently visit these domains, they encounter a fake Cloudflare-style CAPTCHA prompt. Beneath this prompt, instructions are displayed for macOS users to copy a command and paste it into their terminal.
If accessed from a Windows device, the site provides Windows-specific instructions; however, the malware is currently focused on macOS.
Once users copy and paste the Base64-encoded command into their terminal, the script fetches and executes a lengthy AppleScript from a command-and-control (C2) server (such as odyssey1[.]to or 45[.]135.232.33).
This script is not heavily obfuscated, allowing straightforward analysis by security researchers. Upon execution, it presents a fake authentication prompt designed to capture the user’s password.
To validate stolen credentials silently, it uses the macOS dscl command with the authonly parameter, ensuring the process remains hidden.
Technical Execution and Data Harvesting
The malware script uses the mkdir -p A command to create nested directories within /tmp (notably /tmp/lovemrtrump) for storing collected data. It copies macOS Keychain files to these directories, enabling decryption if the user’s password is captured.
The script also targets desktop wallets (such as Electrum, Coinomi, and Exodus), browser data from Chrome, Firefox, and Safari, as well as over 100 browser extensions, particularly cryptocurrency wallets like MetaMask.
For Chromium-based browsers, the malware extracts private keys, seed phrases, session tokens, and password manager configurations.
Firefox users are vulnerable to theft via the logins.json file, which is decrypted using the key4.db file. Safari users risk losing cookies, autofill data, and browsing history.
The script compiles stolen data—including browser histories, wallets, and personal documents into a ZIP file (out.zip) and exfiltrates it to the attacker’s server using a curl POST request.
If the upload fails, the script retries up to 10 times with 60-second delays, ensuring persistent data delivery. Hard-coded headers (build ID, username) are used to tag stolen data for tracking.
Mitigation and Recommendations
To counter the Odyssey Stealer and similar threats, organizations are advised to implement robust endpoint security solutions, network intrusion detection/prevention systems (NIDS/NIPS), and web application firewalls.
Firewalls should block outbound communications to known malicious IPs and domains. Behavior-based monitoring can detect unusual activity, while application whitelisting prevents unauthorized executables from running.
Users should only install apps from the official Mac App Store or verified developer sites and avoid running scripts from untrusted sources.
Security awareness training is crucial to prevent social engineering attacks. Organizations should also develop comprehensive incident response plans to isolate and remediate affected systems quickly.
In summary, the Clickfix tactic demonstrates how threat actors exploit user trust and technical sophistication to harvest credentials and sensitive data. Vigilance, robust security controls, and user education remain the best defenses against these evolving threats.
.webp?w=696&resize=696,0&ssl=1)





