A critical vulnerability that transforms ordinary USB webcams into sophisticated cyber weapons, marking the first documented case where attackers can remotely weaponize USB devices already connected to computers.
The groundbreaking research by Eclypsium’s Jesse Michael and Mickey Shkatov, presented at DEF CON 2025, demonstrates how specific Lenovo webcam models can be converted into BadUSB attack tools capable of injecting malicious keystrokes and maintaining persistent access to infected systems.
The discovery represents a significant evolution in BadUSB attacks, which traditionally required physical device replacement or insertion of malicious hardware.

Unlike conventional BadUSB tools like the Hak5 Rubber Ducky that must be physically plugged into target systems, this new attack vector allows remote adversaries to compromise existing webcams without any physical interaction.
The vulnerability affects Lenovo 510 FHD and Performance FHD webcams manufactured by SigmaStar, which run full Linux operating systems on ARM-powered System-on-Chip processors.
These devices utilize Linux USB Gadget functionality, enabling them to masquerade as various USB peripherals including keyboards, storage devices, or network adapters.
Technical Exploitation
The attack leverages the cameras’ embedded Linux environment running on SigmaStar’s SSC9351D processor, which features dual-core ARM Cortex-A7 CPUs with embedded DDR3 memory.
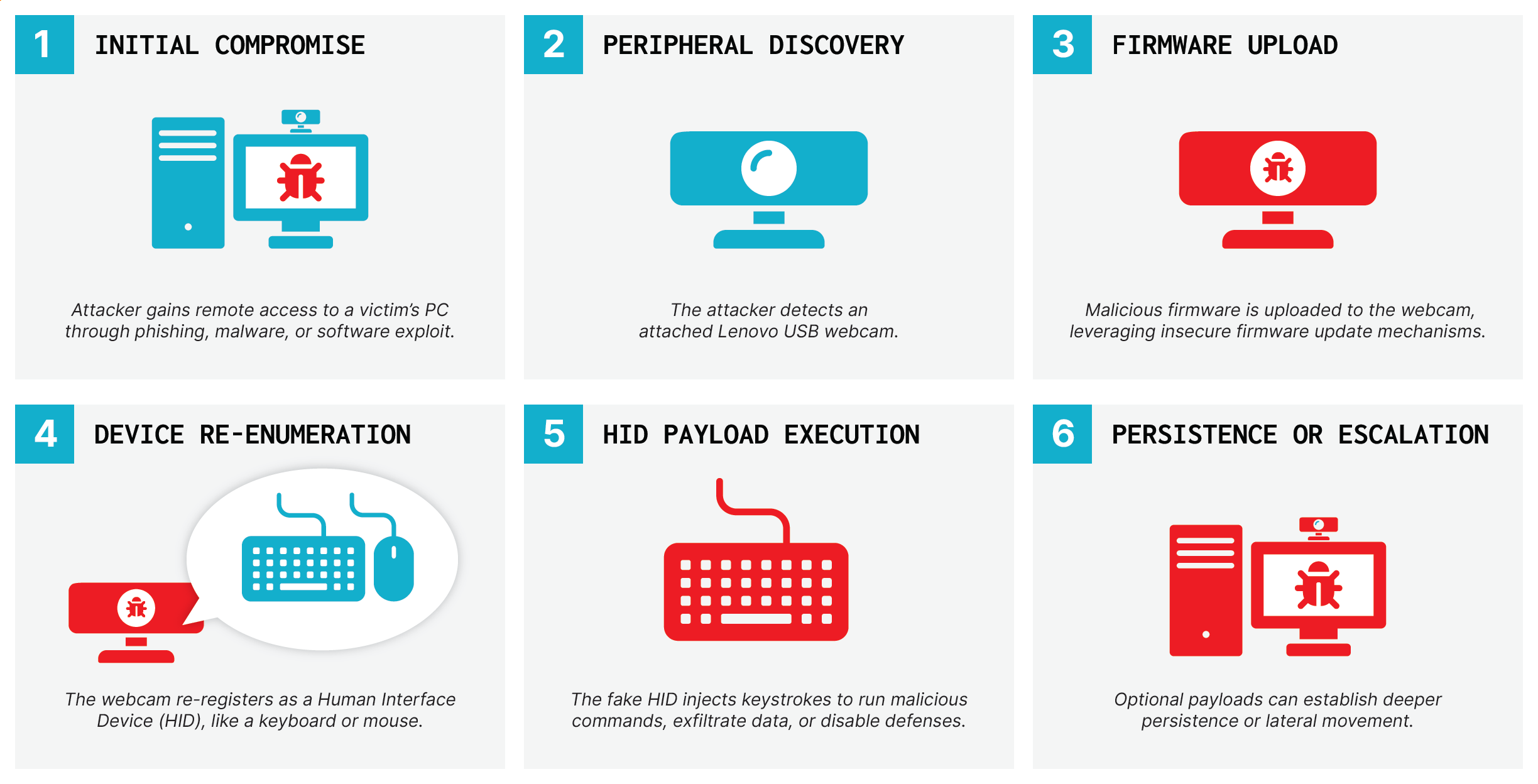
Attackers can exploit the insecure firmware update process by sending specific commands over USB to erase the onboard 8MB SPI flash memory and install malicious firmware.
Once compromised, the weaponized webcam can inject keystrokes, execute commands, and establish covert communication channels while maintaining its original camera functionality.
The attack provides unprecedented persistence, as the malicious firmware survives complete operating system reinstallations and can repeatedly reinfect host computers.
Detection proves extremely challenging since the malicious code operates independently of the host operating system and traditional endpoint security solutions.
The researchers warn that this vulnerability extends beyond the tested Lenovo models, potentially affecting numerous USB peripherals that run Linux without proper firmware validation.
The attack scope could encompass various smart devices, industrial equipment, and IoT peripherals that utilize similar Linux-based architectures.
The researchers identified that these webcams lack firmware signature validation, allowing attackers to completely overwrite the device’s software through a simple USB command sequence.
Mitigations
Following responsible disclosure, Lenovo collaborated with SigmaStar to address the security flaws and released firmware version 4.8.0 for affected webcam models.
The updated firmware installation tool now includes signature validation mechanisms to prevent unauthorized firmware modifications.
Users of affected devices can obtain security updates through Lenovo’s official support channels.
The vulnerability has been cataloged as LEN-194466 in Lenovo’s security advisory system, with the company providing specific firmware update links for the 510 FHD Webcam and Performance FHD Webcam models.
Security experts emphasize that organizations must reassess their hardware trust models and implement more granular monitoring of USB peripheral behavior to defend against this emerging threat vector.
This research highlights critical gaps in device supply chain security and underscores the urgent need for mandatory firmware signing across all USB-connected devices.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.
.webp?w=696&resize=696,0&ssl=1)
.webp?w=356&resize=356,220&ssl=1)




