In a recent security incident, the Wiz Research Team uncovered a sophisticated cyberattack targeting TeamCity, a popular continuous integration and delivery (CI/CD) platform, by abusing an exposed Java Debug Wire Protocol (JDWP) interface.
This attack highlights the risks of misconfigured debugging utilities and the rapid exploitation capabilities of modern threat actors.
Fast, Stealthy Attacks – How JDWP Became a Target
JDWP is a built-in Java protocol designed for remote debugging of applications. While invaluable during development, JDWP lacks default authentication or access control mechanisms.
If left exposed to the internet, often due to misconfiguration or careless deployment, it enables attackers to inspect and control live Java applications remotely.
JDWP is not enabled by default but is frequently activated in debug environments for widely used platforms, such as TeamCity, Jenkins, Selenium Grid, and Apache Tomcat.
In this incident, attackers rapidly identified and compromised a honeypot CI server with an open JDWP port (5005). Wiz observed that malware was deployed within hours of exposure, reflecting JDWP’s popularity among cybercriminals.
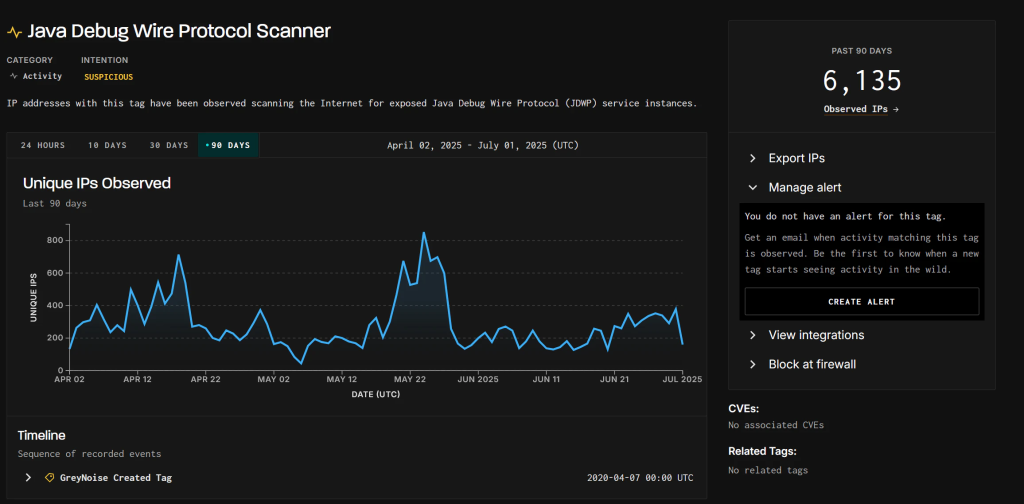
Further analysis, including GreyNoise data, revealed over 6,000 unique IPs scanning for JDWP instances in just 90 days.
From Exploit to Persistence – The Attack Chain Unveiled
After confirming the open JDWP port via handshake, the attackers leveraged protocol features to enumerate loaded Java classes and methods.
By interacting directly with the JVM through JDWP, they invoked java.lang.Runtime.getRuntime(). exec () to execute custom shell commands. These commands fetched and executed a dropper script (logservice.sh) from attacker-controlled domains.
The dropper script implemented several malicious actions:
- Termination of Competing Processes: Any process consuming more than 60% of the CPU (except those on a limited allowlist) was targeted and terminated to maximize mining efficiency.
- Cryptominer Deployment: A renamed, customized XMRig miner binary was downloaded and placed in a concealed directory, with its configuration hardcoded to avoid detection by traditional security tools.
- Multi-layered Persistence: The miner setup registered itself in system startup files (
.bashrc,.zshrc,rc.local), created cron jobs, and established a persistent systemd service—each camouflaged as legitimate utilities.
To further evade detection, the miner communicated via mining pool proxies, which obscured the wallet address and made forensic attribution challenging.
Detection and Mitigation
Wiz’s agentless malware detection and runtime sensors proved effective in flagging each phase of the attack, from the initial JDWP exploitation to cryptomining activity.
The company’s catalog of YARA rules and behavioral analytics can recognize not only the malicious scripts (logservice.sh, modified XMRig binaries) but also system modifications such as unauthorized cron job insertions and new systemd service files.
This incident highlights the importance of securing debug interfaces, particularly JDWP, by restricting network exposure, enforcing robust access controls, and monitoring for suspicious configuration changes.
As cryptomining attacks evolve, layered detection and rapid remediation remain essential for protecting CI/CD infrastructure.
.webp?w=696&resize=696,0&ssl=1)





