Instagram implements an unusual certificate management strategy, replacing their TLS certificates on a daily basis using certificates with approximately one-week validity periods.
This practice deviates significantly from industry standards where certificates typically remain valid for 90 to 365 days, marking a potentially significant shift in how major tech platforms approach digital security infrastructure.
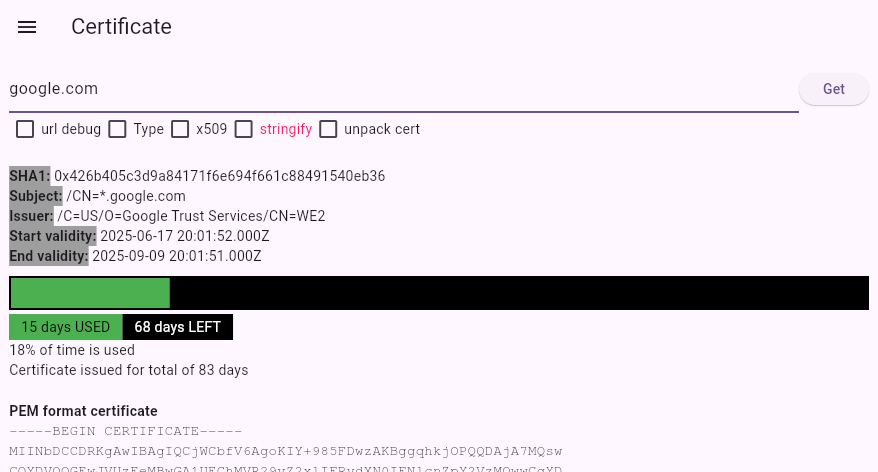
The unusual certificate behavior was first discovered during routine network debugging when a researcher noticed Instagram’s TLS certificate had an anomalous 53-day validity period, far shorter than the typical 90, 180, or 365-day certificates commonly used across the internet.
Further investigation revealed that Instagram consistently maintains certificates with approximately eight days remaining until expiration, replacing them daily when about seven days of validity remain.
Through systematic monitoring over several weeks, the research documented Instagram’s precise certificate replacement schedule.
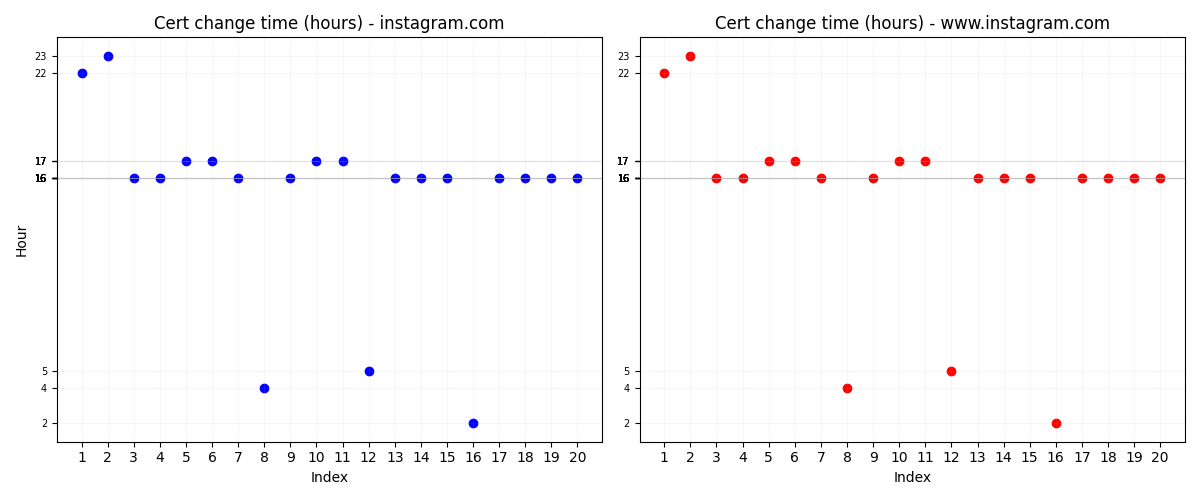

The platform changes certificates between 16:00 and 17:00 UTC, typically within a 25-30 minute window.
This daily rotation pattern was consistent across multiple domains, with data showing that Instagram processes approximately one certificate change per day for each monitored domain.
The consistency of this timing suggests an automated system managing the certificate lifecycle.
A certificate for Instagram was issued for 53 days. Usually, I expect a certificate to be issued for 90, 180, 365, or close to those values and this seemed very odd.
This deliberate separation indicates a strategic decision to maintain distinct certificate chains for different service endpoints, possibly for enhanced security compartmentalization or operational flexibility.
Technical Implementation
The monitoring setup revealed the sophisticated nature of Instagram certificate management infrastructure.
In general, Instagram starts using a certificate that has a lifetime of slightly more than 8 days and replaces it one day later when it has left a little more than 7 days before expiration.
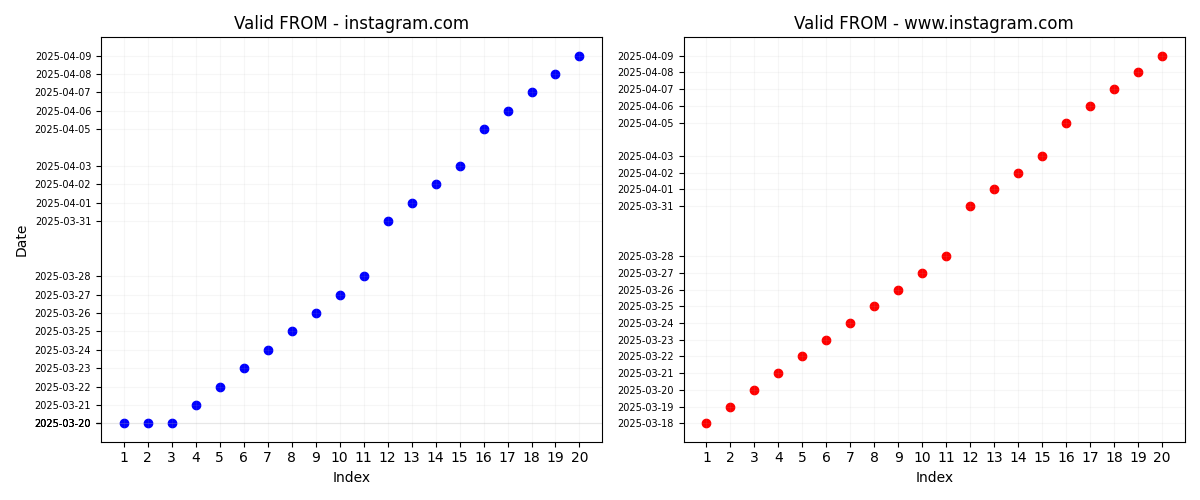
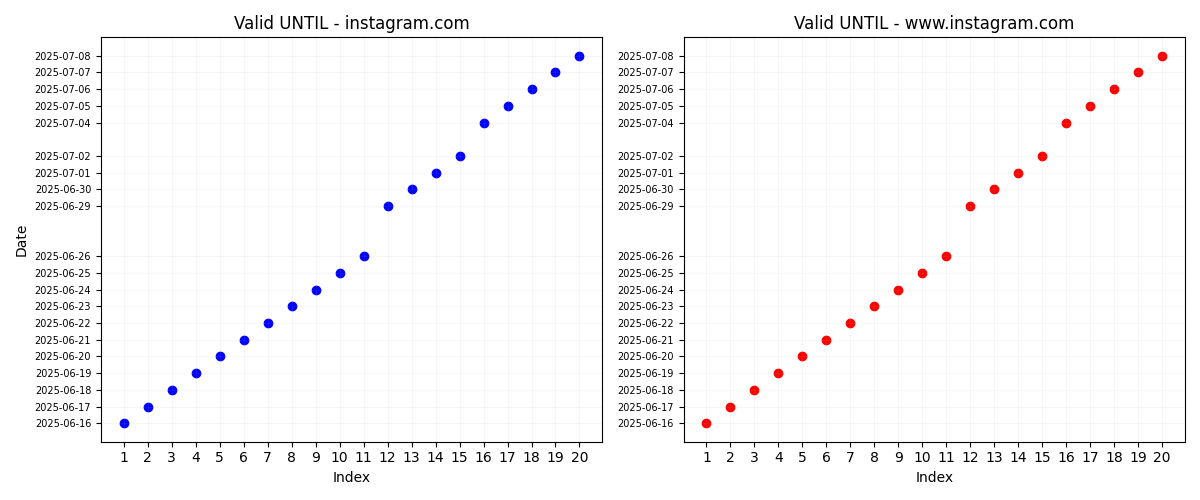
Each certificate follows a predictable pattern where validity periods start and end times increase by exactly one day with each replacement cycle.
The certificates are issued by DigiCert SHA2 High Assurance Server CA and include comprehensive subject alternative names covering multiple Instagram-related domains including CDN endpoints and associated services.
The research methodology involved automated certificate retrieval every five minutes, extracting key information including serial numbers, SHA-1 hashes, validity periods, and issuer details.
This granular monitoring approach provided precise timing data about certificate transitions and revealed the mechanical precision of Instagram’s certificate rotation system.
The collected data spans approximately one month and encompasses 20 different certificates per monitored domain.
Certificate validity periods consistently begin with approximately 8.5 days remaining and conclude when roughly 7.5 days remain, creating a narrow operational window that minimizes certificate lifetime while maintaining service continuity.
This tight rotation schedule suggests Instagram prioritizes certificate freshness over the operational simplicity of longer-lived certificates.
Security Implications
Instagram’s daily certificate rotation strategy represents a significant departure from conventional TLS certificate management practices and may signal broader industry trends toward reduced certificate lifespans.
According to Report, the effectiveness of this approach depends heavily on how Instagram isolates and protects its certificate generation infrastructure.
While this approach theoretically limits the exposure window if private keys become compromised, security experts debate whether the practical benefits justify the operational complexity.
The strategy addresses growing concerns about certificate compromise by minimizing the timeframe during which stolen private keys remain valid.
However, critics argue that if attackers gain access to Instagram’s certificate infrastructure, they would likely access the entire key generation and storage system rather than individual certificates.
The effectiveness of this approach depends heavily on how Instagram isolates and protects its certificate generation infrastructure.
This development could influence industry standards for certificate management, particularly among major technology platforms seeking to demonstrate enhanced security postures.
The practice may become more prevalent as automation tools make frequent certificate rotation operationally feasible for organizations with sophisticated infrastructure capabilities.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




