A newly uncovered cyber espionage toolkit used by the GrayAlpha threat group, strongly linked to the notorious FIN7 cybercrime syndicate, has security experts warning organizations about increasingly sophisticated, multi-layered attack campaigns targeting standard software update processes.
Security researchers with Insikt Group have identified a potent combination of custom PowerShell loaders and malware payloads deployed by GrayAlpha, including the newly disclosed PowerNet loader and its follow-on payload, NetSupport RAT (Remote Access Trojan).
The group mimics legitimate software update pages, most notably for popular browsers and utilities such as 7-Zip and Advanced IP Scanner, to trick victims into downloading malicious files.
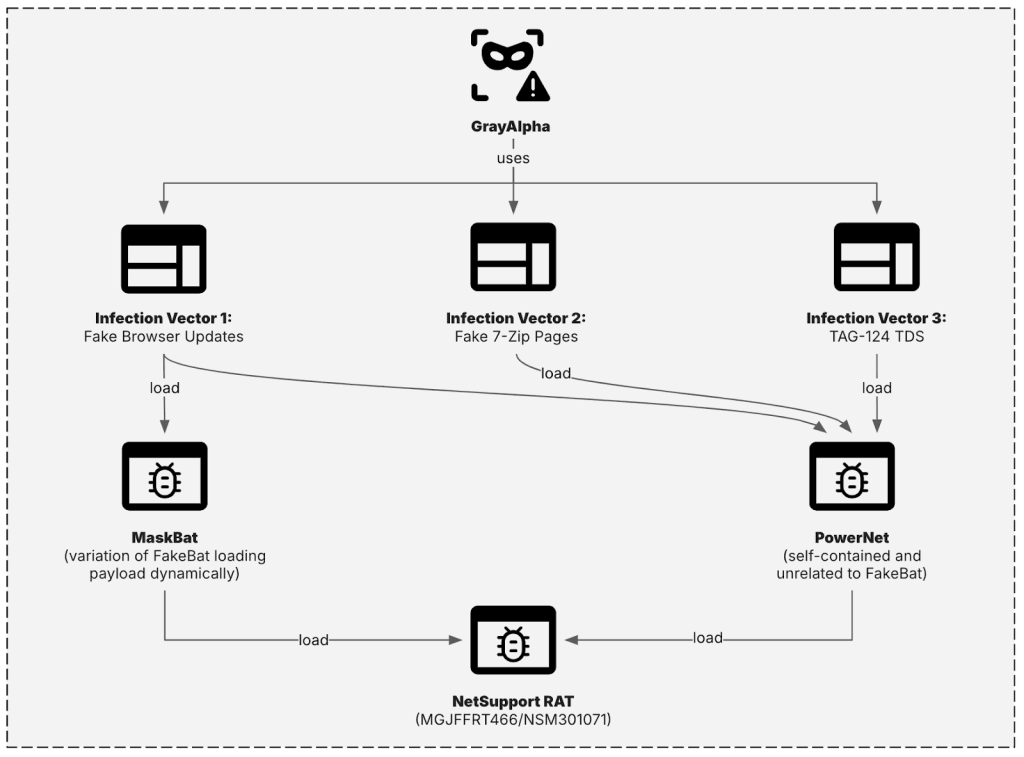
According to technical data, these campaigns leverage at least three main infection vectors: counterfeit browser update pages, fake 7-Zip download sites, and the previously undocumented “TAG-124” Traffic Distribution System (TDS).
All vectors converge on NetSupport RAT infections, allowing attackers to maintain persistent remote control over compromised systems.
Attack Techniques and Infrastructure
GrayAlpha’s campaigns are marked by their high degree of obfuscation and evasion. The group’s custom PowerNet loader operates by decompressing and executing NetSupport RAT directly in memory, minimizing disk signatures and evading traditional endpoint defenses.
Another script, dubbed MaskBat, is a dynamic variant of the widely observed FakeBat loader, obfuscated with strings unique to GrayAlpha.
Attackers push these payloads via fraudulent browser update prompts that impersonate Google Meet, LexisNexis, SAP Concur, and other enterprise platforms.
The group’s infrastructure relies heavily on bulletproof hosting providers, most notably Stark Industries Solutions (AS44477) and FORTIS-AS (AS41745), a network tied to previous FIN7 operations.
Technical analysis reveals domains such as “advanced-ip-scanner.link,” “aimp.day,” and “concur.life,” among others, as vehicles for malware distribution.
Remarkably, some domains were registered as recently as April 2025, indicating active and ongoing operations.
The use of TAG-124 TDS, not previously documented in connection with GrayAlpha, suggests the group’s continuous efforts to diversify its delivery methods and evade detection.
Defensive Recommendations and Outlook
In response to these threats, security professionals are advised to enforce application allow lists and integrate advanced detection mechanisms, such as YARA rules and Malware Intelligence Hunting queries.
Employee security awareness training is crucial, as attackers exploit human error using convincing browser update prompts and malvertising redirects.
Monitoring network artifacts, especially communications with known malicious IP addresses, and utilizing threat intelligence feeds are essential for identifying and mitigating infections.
The continued evolution and professionalization of GrayAlpha’s operations mirror broader trends in cybercrime, with actors leveraging specialized tools and collaborative tactics often associated with advanced persistent threats (APTs).
However, unlike nation-state APTs, GrayAlpha and FIN7 focus relentlessly on financial gain, targeting organizations globally with sophisticated attack techniques and rapidly shifting infrastructure.
As defenders adapt, the cybercriminal landscape becomes increasingly complex an ongoing arms race between evolving attack methods and resilient defensive strategies.
.webp?w=696&resize=696,0&ssl=1)





