A sophisticated open-source tool designed to automate GitHub Device Code Phishing attacks, addressing critical operational challenges that have previously limited the effectiveness of these social engineering techniques.
The tool, called GitPhish, represents a significant advancement in cybersecurity testing capabilities for organizations seeking to validate their defenses against increasingly sophisticated supply chain attacks.
GitPhish emerged from research conducted two weeks prior on GitHub Device Code Phishing, a technique that can leverage an eight-digit code and a phone call to completely compromise an organization’s GitHub repositories and software supply chain.
While the underlying concept appears straightforward, executing these attacks in practice involves multiple layers of complexity that have historically limited their scalability and effectiveness.
The primary challenge stems from OAuth 2.0 Device Authorization Grant implementations, commonly known as device code flows, which typically provide only a 15-minute window from user and device code pair generation until expiration.
This time constraint forces attackers to actively generate tokens while targets are engaged, effectively limiting attacks to one user at a time.
Previous attempts at asynchronous, scaled phishing required attackers to rush targets through authentication processes, often compromising the quality of social engineering ruses and creating significant operational barriers for security professionals attempting to validate organizational defenses.
Dynamic Code Generation
GitPhish addresses these operational challenges through two core technological innovations that fundamentally transform the attack methodology.
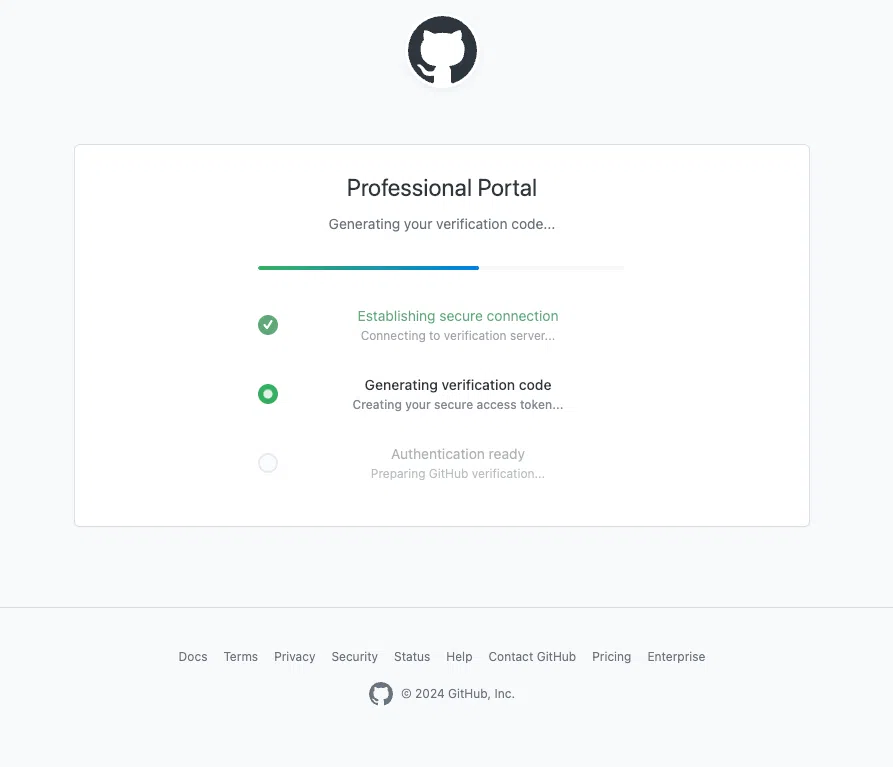
The platform’s first major feature involves the complete automation of GitHub Pages deployment, which builds instant credibility with targets while guiding them through the Device Code login flow.
The tool is immediately available as an open-source project on GitHub, requiring only Python installation, a GitHub personal access token, and minimal setup time.
This professional presentation significantly enhances the believability of phishing attempts by leveraging GitHub’s trusted domain infrastructure.
The second critical innovation centers on dynamic device code generation, which generates codes just-in-time rather than when attackers initially send lures.
This approach effectively starts the expiration clock upon target interaction instead of during the initial attack phase, enabling red team operators to execute GitHub Device Code Phishing attacks across multiple targets simultaneously without concerning themselves with device code expiration limitations.
The tool supports both command-line interface and web dashboard operations, providing comprehensive logging, analytics, and token management capabilities.
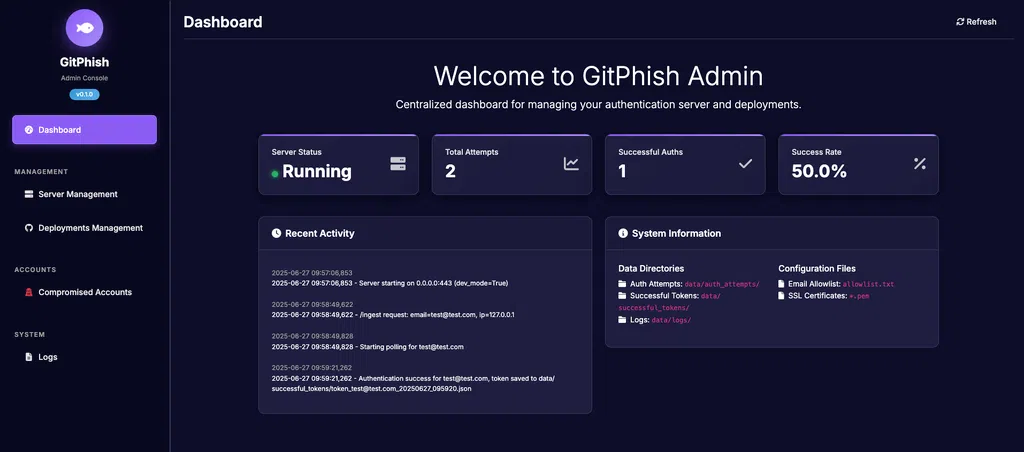
Security teams can monitor attack progress, analyze target responses, and manage compromised tokens through an intuitive interface designed specifically for professional security assessments.
Security Training Programs Expand
According to Report, GitPhish has been specifically designed for security teams conducting assessments and building detection capabilities around Device Code Phishing in GitHub environments.
Red team professionals can simulate realistic attack scenarios to test organizational resilience, while detection engineers can validate their ability to identify suspicious OAuth flows, unusual GitHub authentication patterns, and potential social engineering attempts.
Security teams can clone the repository, execute pip install commands, launch the dashboard, and deploy professional landing pages within minutes.
The project includes extensive documentation with real-world examples tailored for both red team operations and detection engineering scenarios.
Additionally, security professionals seeking advanced CI/CD attack technique mastery can attend “Pipeline to Pwn: Mastering Modern CI/CD Attack Chains” training at BlackHat USA 2025, scheduled for August 2-3 and August 4-5, featuring hands-on instruction in pipeline secrets extraction, self-hosted runner abuse, and comprehensive attack scenarios.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




