Fortinet has disclosed a critical authentication bypass vulnerability in its FortiWeb web application firewall that allows unauthenticated attackers to log in as any existing user on affected devices.
The vulnerability, tracked as CVE-2025-52970 and dubbed “Fort-Majeure” by security researcher Aviv Y, affects multiple versions of FortiWeb and has been assigned a high CVSS score of 7.7.
The vulnerability stems from improper handling of parameters in FortiWeb’s session cookie parsing code, specifically in how the system selects encryption keys based on user-controlled input.
According to the official advisory published on August 12, 2025, the vulnerability allows an “unauthenticated remote attacker in possession of non-public information (pertaining to both the device and to the targeted user) to log in as any existing user on the device via a specially crafted request”.
The exploit targets FortiWeb’s session cookie structure, which consists of three components: an “Era” parameter that determines the type of session, an encrypted payload containing user information, and an authentication hash for verification.
Security researcher Aviv Y discovered that by manipulating the Era parameter with values outside the expected range (0 or 1), attackers can force the system to read uninitialized memory and use a predictable zero-value key for both encryption and session signing.
This effectively removes all entropy from the cryptographic process, making session forgery trivial for attackers who know the target username.
FortiWeb Vulnerability
The vulnerability affects FortiWeb versions across multiple major releases, with FortiWeb 8.0 remaining unaffected.
Vulnerable versions include FortiWeb 7.6.0 through 7.6.3, FortiWeb 7.4.0 through 7.4.7, FortiWeb 7.2.0 through 7.2.10, and FortiWeb 7.0.0 through 7.0.10.
Organizations running these versions must immediately upgrade to the patched releases: FortiWeb 7.6.4 or above, 7.4.8 or above, 7.2.11 or above, or 7.0.11 or above.
The vulnerability requires specific conditions for successful exploitation, including knowledge of a valid username and the target user having an active session during the attack.
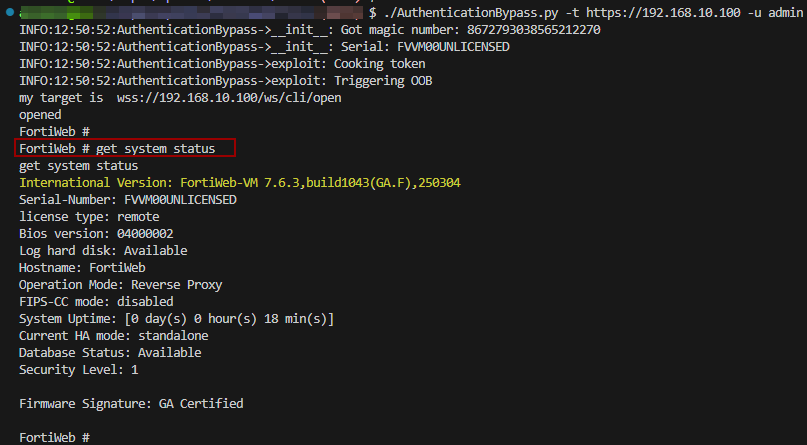
However, once these conditions are met, attackers can leverage endpoints like /api/v2.0/system/status.systemstatus or /ws/cli/open to impersonate administrators and gain elevated privileges.
It is possible to use the /ws/cli/open endpoint to open a connection to the FortiWeb CLI:
The vulnerability was responsibly disclosed by Aviv Y (@0x_shaq) and appears to be a sequel to previous FortiWeb vulnerabilities, highlighting ongoing security challenges in Fortinet’s web application firewall products.
Growing Pattern of Fortinet Security Issues
This latest vulnerability adds to a concerning pattern of critical security vulnerabilities in Fortinet products throughout 2025.
Earlier this year, CVE-2025-25257, a critical SQL injection vulnerability in FortiWeb’s Fabric Connector, was actively exploited in the wild shortly after proof-of-concept code became public.
That vulnerability, with a CVSS score of 9.6, allowed unauthenticated attackers to achieve remote code execution and prompted urgent warnings from cybersecurity agencies worldwide.
The rapid succession of critical vulnerabilities in FortiWeb underscores the importance of maintaining current patch levels and implementing defense-in-depth strategies for organizations relying on Fortinet security products.
While there is currently no evidence of CVE-2025-52970 being exploited in the wild, the publication of technical details and the historical pattern of Fortinet vulnerabilities being quickly weaponized suggests that organizations should prioritize immediate patching to prevent potential compromise of their web application firewall infrastructure.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




