An advanced espionage campaign designated “Fire Ant” that has been targeting virtualization and networking infrastructure since early 2025.
The sophisticated threat actors demonstrated exceptional persistence and operational resilience, adapting in real-time to eradication efforts while maintaining prolonged access to compromised systems.
The campaign’s techniques and tooling show strong alignment with previous operations attributed to the Chinese-linked threat group UNC3886.
Fire Ant’s operations centered on exploiting VMware ESXi hypervisors and vCenter management servers to establish deep, persistent access within target organizations.
The attackers initially compromised vCenter servers by exploiting CVE-2023-34048, an out-of-bounds write vulnerability that enables unauthenticated remote code execution.
This critical vulnerability allowed the threat actors to gain control over the entire virtualization management layer without requiring valid credentials.
Once inside vCenter environments, the attackers extracted ‘vpxuser’ service account credentials, which provided administrative access to all connected ESXi hosts.
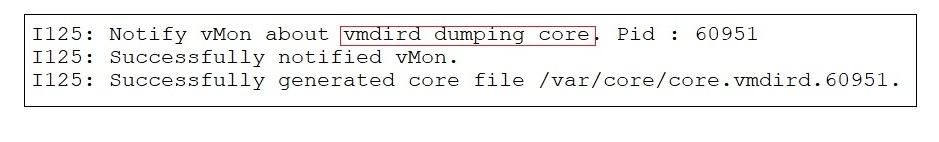
The group then deployed multiple persistent backdoors across the infrastructure, including malicious vSphere Installation Bundles (VIBs) that bypassed signature validation and custom Python-based backdoors that survived system reboots.

These tools were strategically named to blend with legitimate system processes, such as ‘ksmd’ binaries placed in system directories.
VMware ESXi and vCenter Vulnerabilities
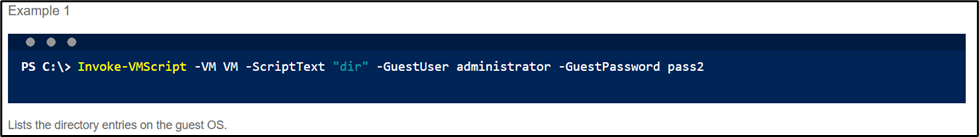
The most concerning aspect of Fire Ant’s capabilities involved their exploitation of CVE-2023-20867, a VMware Tools vulnerability that permits unauthenticated command execution from hypervisor hosts directly into guest virtual machines.
Using PowerCLI commands routed through ‘vmtoolsd.exe’, the attackers could execute encoded PowerShell commands on guest systems without generating typical user activity logs.
The threat actors also demonstrated advanced credential harvesting techniques by creating memory snapshots of virtual machines and using a compiled variant of the Volatility Framework to extract sensitive data, including domain controller credentials.

This method left minimal forensic evidence since snapshots could be quickly created and removed.
Additionally, the group deployed tools to disable endpoint detection and response (EDR) solutions, specifically targeting SentinelOne agents while leaving other monitoring systems operational.
Network Segmentation Rendered Ineffective
According to Report, Fire Ant systematically bypassed network segmentation by compromising infrastructure components that naturally bridge network boundaries.
The attackers exploited F5 load balancers using CVE-2022-1388, deploying tunneling webshells that enabled cross-network communication.
They also leveraged IPv6 traffic to bypass IPv4-focused filtering rules, exploiting common gaps in dual-stack network configurations.
The group’s operational resilience proved particularly challenging for defenders. When eradication efforts began, Fire Ant actively monitored response activities, rotated toolsets, and re-compromised cleaned systems through redundant access paths.
In some instances, they renamed their malicious tools to impersonate legitimate forensic utilities being used by incident responders.
This campaign underscores critical blind spots in traditional security approaches, as virtualization infrastructure often lacks comprehensive monitoring and detection capabilities.
Organizations must implement enhanced logging for ESXi hosts, monitor for unauthorized VIB installations, and establish detection rules for anomalous host-to-guest command execution patterns to defend against similar advanced persistent threats.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




